## Sequence Diagram: Secure Build Process
### Overview
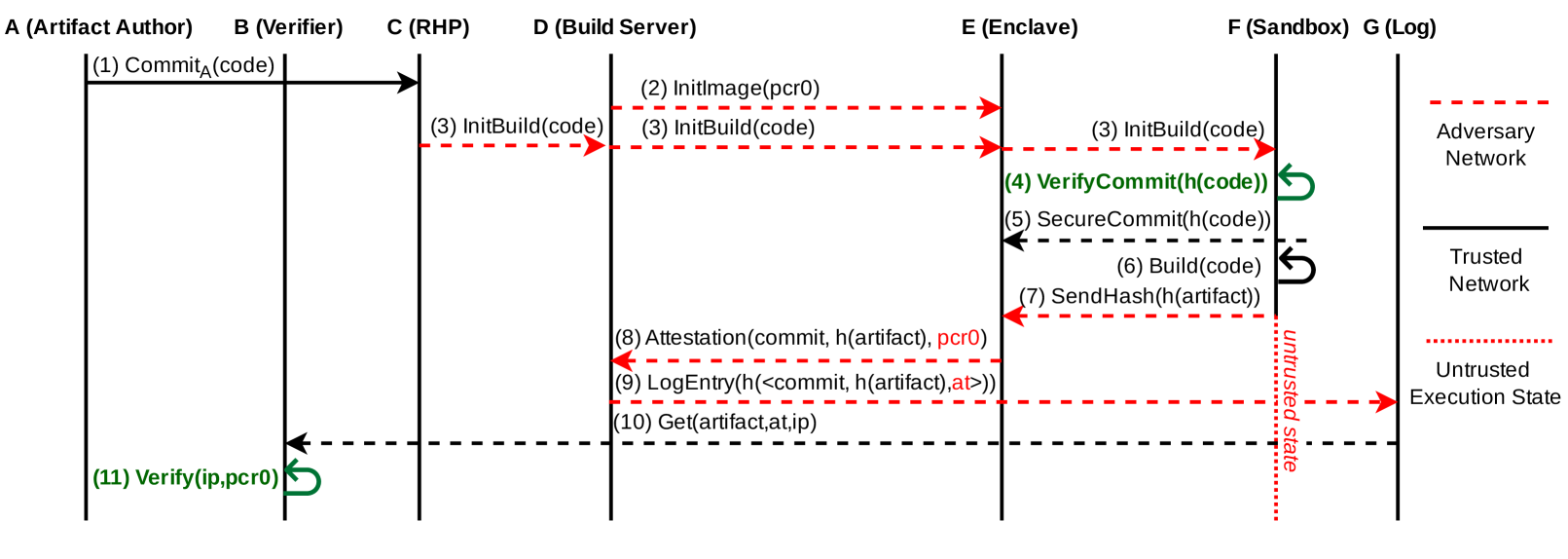
The image is a sequence diagram illustrating a secure build process involving multiple entities: Artifact Author, Verifier, RHP (Remote Hypervisor Provider), Build Server, Enclave, Sandbox, and Log. The diagram depicts the flow of information and actions between these entities, highlighting the use of trusted and untrusted networks and execution states.
### Components/Axes
* **Entities (Top)**:
* A (Artifact Author)
* B (Verifier)
* C (RHP)
* D (Build Server)
* E (Enclave)
* F (Sandbox)
* G (Log)
* **Vertical Lines**: Represent the lifeline of each entity, indicating the passage of time.
* **Arrows**: Indicate the direction of information flow between entities.
* **Labels on Arrows**: Describe the action or data being transmitted.
* **Legend (Right)**:
* Red dashed line: Adversary Network
* Black solid line: Trusted Network
* Red dotted line: Untrusted Execution State
### Detailed Analysis
Here's a breakdown of the sequence of events:
1. **(1) CommitA(code)**: The Artifact Author (A) commits code to the Verifier (B) over a trusted network (solid black line).
2. **(2) InitImage(pcr0)**: The Build Server (D) initializes an image with PCR0 (Platform Configuration Register 0) from the Adversary Network (red dashed line) to the Enclave (E).
3. **(3) InitBuild(code)**: The RHP (C) initiates a build with the code to the Build Server (D) over the Adversary Network (red dashed line). The Build Server (D) then forwards the InitBuild(code) to the Sandbox (F) over the Adversary Network (red dashed line). The Sandbox (F) then forwards the InitBuild(code) to the Enclave (E) over the Adversary Network (red dashed line).
4. **(4) VerifyCommit(h(code))**: The Enclave (E) verifies the commit using a hash of the code. This communication is internal to the Enclave (green arrow with a loop back to itself).
5. **(5) SecureCommit(h(code))**: The Enclave (E) secures the commit using a hash of the code. This communication is over a trusted network (black dashed line) to the Sandbox (F).
6. **(6) Build(code)**: The Sandbox (F) builds the code. This communication is internal to the Sandbox (black arrow with a loop back to itself).
7. **(7) SendHash(h(artifact))**: The Sandbox (F) sends the hash of the artifact to the Enclave (E) over the Adversary Network (red dashed line).
8. **(8) Attestation(commit, h(artifact), pcr0)**: The Enclave (E) sends an attestation containing the commit, hash of the artifact, and PCR0 to the Build Server (D) over the Adversary Network (red dashed line).
9. **(9) LogEntry(h(<commit, h(artifact), at>))**: The Build Server (D) logs an entry containing the hash of the commit, hash of the artifact, and attestation to the Log (G) over the Adversary Network (red dashed line).
10. **(10) Get(artifact, at, ip)**: The Build Server (D) retrieves the artifact, attestation, and IP address from the Log (G) over a trusted network (black dashed line).
11. **(11) Verify(ip, pcr0)**: The Verifier (B) verifies the IP address and PCR0. This communication is over a trusted network (black dashed line) to the Artifact Author (A) and loops back to itself (green arrow with a loop back to itself).
### Key Observations
* The Enclave (E) plays a crucial role in verifying the commit and securing the build process.
* The Sandbox (F) is used for building the code.
* The Adversary Network (red dashed line) is used for communication between several entities, including the Build Server, Enclave, and Sandbox.
* The Log (G) stores information about the build process.
* The Verifier (B) verifies the IP address and PCR0.
### Interpretation
The sequence diagram illustrates a secure build process designed to protect against potential attacks. The use of an enclave and sandboxing helps to isolate the build process from untrusted environments. The attestation process provides evidence of the integrity of the build. The logging of build information allows for auditing and verification. The diagram highlights the importance of using trusted networks for sensitive communications and untrusted execution states for potentially vulnerable processes. The process ensures that the artifact is built in a secure environment and that its integrity can be verified.