\n
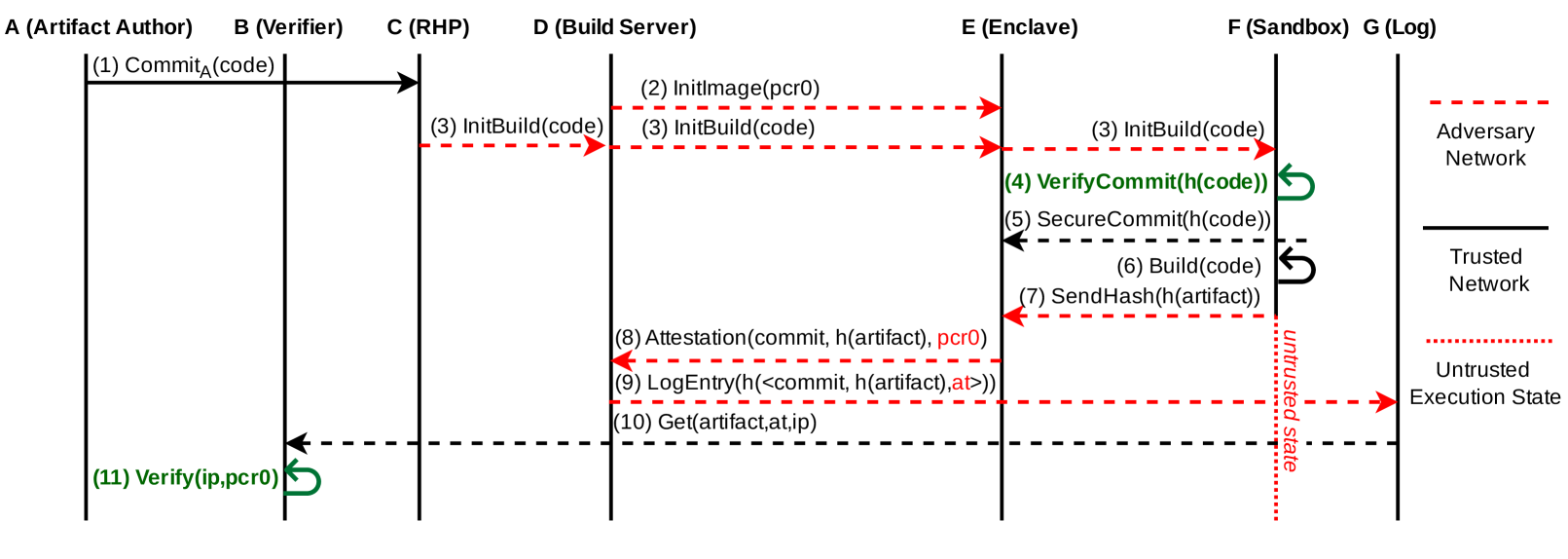
## Diagram: Secure Build Process Flow
### Overview
This diagram illustrates a secure build process involving multiple parties: an Artifact Author, a Verifier, a Remote Hardware Provider (RHP), a Build Server, an Enclave, a Sandbox (Log), and an Adversary Network. The diagram depicts the flow of messages and data between these parties, highlighting trusted and untrusted network segments and execution states. The process appears to focus on verifying the integrity of code and artifacts during a build process.
### Components/Axes
The diagram consists of seven vertical columns representing the different parties involved:
* **A (Artifact Author)**
* **B (Verifier)**
* **C (RHP)**
* **D (Build Server)**
* **E (Enclave)**
* **F (Sandbox (Log))**
* **G (Adversary Network)**
Horizontal lines with numbered labels represent the sequence of interactions. Three types of lines are used to indicate trust levels:
* Solid lines: Trusted Network
* Dashed lines: Adversary Network
* Dot-dashed lines: Untrusted Execution State
A legend on the right side defines these line types.
### Detailed Analysis or Content Details
The diagram shows the following sequence of events:
1. **(1) Commit<sub>A</sub>(code)**: Artifact Author (A) commits code. A solid arrow indicates this is over a trusted network.
2. **(2) InitImage(pcr0)**: Build Server (D) initializes an image using pcr0. A dashed arrow indicates this is over an adversary network.
3. **(3) InitBuild(code)**: RHP (C) and Build Server (D) initiate the build process with the code. Solid and dashed arrows respectively.
4. **(4) VerifyCommit(h(code))**: Enclave (E) verifies the commit hash of the code. A solid arrow.
5. **(5) SecureCommit(h(code))**: Enclave (E) securely commits the hash of the code. A solid arrow.
6. **(6) Build(code)**: Enclave (E) builds the code. A solid arrow.
7. **(7) SendHash(h(artifact))**: Enclave (E) sends the hash of the artifact. A solid arrow.
8. **(8) Attestation(commit, h(artifact), pcr0)**: RHP (C) provides attestation with the commit, artifact hash, and pcr0. A solid arrow.
9. **(9) LogEntry(h(<commit, h(artifact),at>>))**: Sandbox (F) logs an entry containing the hash of the commit, artifact hash, and attestation. A dot-dashed arrow.
10. **(10) Get(artifact,at,ip)**: Verifier (B) retrieves the artifact, attestation, and IP. A dot-dashed arrow.
11. **(11) Verify(ip,pcr0)**: Verifier (B) verifies the IP and pcr0. A solid arrow.
The diagram also indicates the following execution states:
* **Adversary Network**: Represented by dashed lines.
* **Trusted Network**: Represented by solid lines.
* **Untrusted Execution State**: Represented by dot-dashed lines.
### Key Observations
The diagram highlights a process where code integrity is verified at multiple stages, particularly within the Enclave (E). The use of hashes (h()) and attestation suggests a strong emphasis on preventing tampering and ensuring the authenticity of the build process. The separation of networks and execution states emphasizes the security boundaries. The Verifier (B) is the final point of verification, confirming the integrity of the artifact.
### Interpretation
This diagram demonstrates a secure remote build process designed to mitigate risks associated with untrusted build environments. The Enclave acts as a trusted execution environment, protecting the build process from malicious interference. The use of cryptographic hashes and attestation provides verifiable proof of the code's integrity. The separation of concerns between the different parties (Author, Verifier, RHP, Build Server, Enclave, Sandbox) enhances security by limiting the potential impact of a compromise in any single component. The process appears to be designed to ensure that the final artifact is built from trusted code and can be verified by an independent party. The inclusion of the Adversary Network indicates an awareness of potential threats and a proactive approach to security. The flow suggests a remote attestation scheme is in place, allowing the Verifier to trust the build process based on the Enclave's attestation. The logging component (Sandbox) provides an audit trail for security analysis. The diagram illustrates a sophisticated security architecture aimed at establishing a high level of confidence in the integrity of the build process.