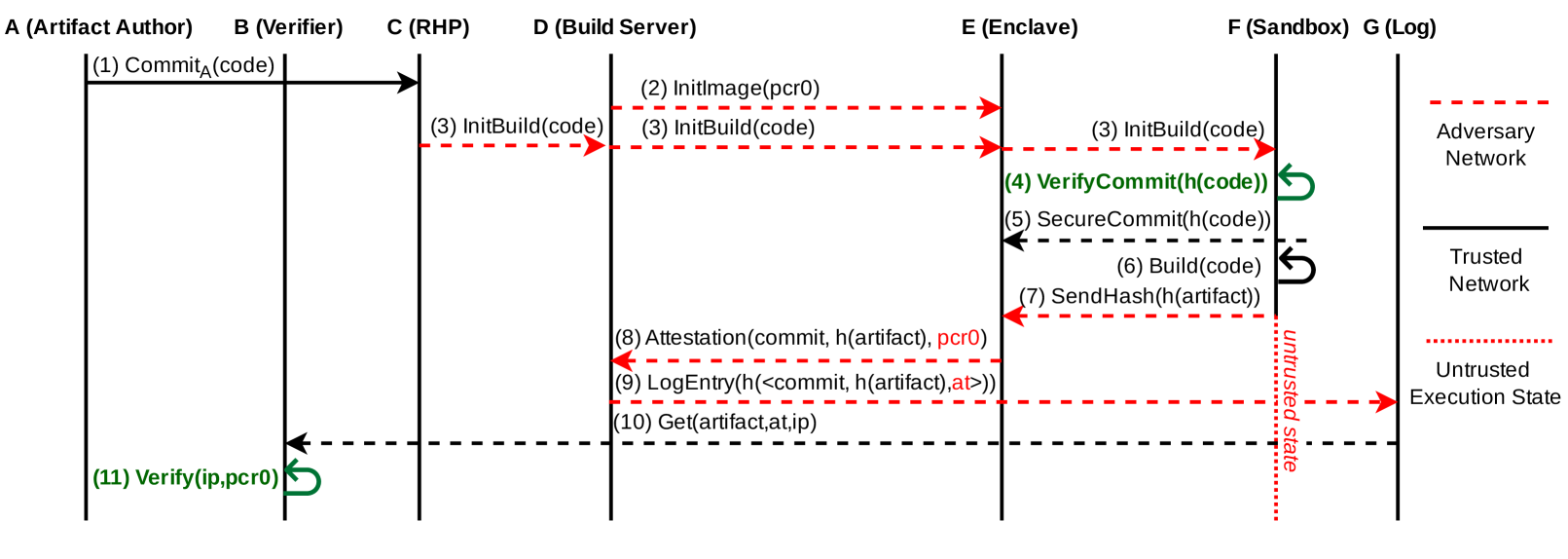
## Flowchart: Artifact Verification and Build Process
### Overview
This flowchart illustrates a multi-stage process for verifying and building software artifacts, emphasizing trust boundaries and execution states. The diagram uses color-coded edges to distinguish between trusted, untrusted, and secure network paths, with a focus on secure commit verification and sandboxed execution.
### Components/Axes
**Nodes (Entities):**
- **A (Artifact Author)**: Initiates the process by committing code.
- **B (Verifier)**: Validates code integrity using PCR0 (Platform Configuration Register).
- **C (RHP)**: Receives initial build instructions and code.
- **D (Build Server)**: Executes code builds and attests to commit hashes.
- **E (Enclave)**: Secure environment for commit verification and artifact retrieval.
- **F (Sandbox)**: Untrusted execution environment for code.
- **G (Log)**: Records system events and attestations.
**Edges (Flow/Relationships):**
- **Red Dashed Lines**: Untrusted network paths (e.g., adversary interactions).
- **Green Lines**: Trusted network paths (secure communication).
- **Black Lines**: Secure network paths (enclave-to-trusted network).
- **Dotted Red Lines**: Untrusted execution state transitions.
**Legend (Right Side):**
- **Adversary Network**: Red dashed lines.
- **Trusted Network**: Green lines.
- **Secure Network**: Black lines.
- **Untrusted Execution State**: Dotted red lines.
### Detailed Analysis
1. **Step 1**: Artifact Author (`A`) commits code (`Commit_A(code)`).
2. **Step 11**: Verifier (`B`) validates the commit using PCR0 (`Verify(ip,pcr0)`), creating a feedback loop to ensure integrity.
3. **Steps 2-3**: RHP (`C`) initializes build images (`InitImage(pcr0)`) and code (`InitBuild(code)`).
4. **Step 4**: Enclave (`E`) verifies commit hashes (`VerifyCommit(h(code))`) and secures them (`SecureCommit(h(code))`).
5. **Step 6**: Build Server (`D`) compiles code (`Build(code)`) and sends artifact hashes (`SendHash(h(artifact))`).
6. **Steps 8-9**: Build Server attests to commit hashes (`Attestation(commit, h(artifact), pcr0)`) and logs entries (`LogEntry(...)`).
7. **Step 10**: Enclave retrieves artifacts (`Get(artifact, at, ip)`).
8. **Flow to Sandbox/Log**:
- Untrusted code flows to Sandbox (`F`) via dotted red lines.
- Log entries (`G`) are secured via black lines to the Trusted Network.
### Key Observations
- **Trust Boundaries**:
- The Enclave (`E`) acts as a secure intermediary between untrusted and trusted networks.
- Adversary Network (`F`) is isolated via red dashed lines, preventing direct access to secure components.
- **Execution States**:
- Code transitions to an "Untrusted Execution State" (dotted red) before sandbox execution.
- SecureCommit (`E`) ensures hashes are cryptographically protected before network transmission.
- **Feedback Loops**:
- Verifier (`B`) continuously validates PCR0, creating a self-correcting integrity check.
### Interpretation
This diagram models a **secure software supply chain** with layered trust assumptions:
1. **Author Trust**: Code is initially untrusted but validated by the Verifier (`B`) using hardware-backed PCR0.
2. **Build Integrity**: The Build Server (`D`) and Enclave (`E`) collaborate to ensure code authenticity via attestations and secure hashing.
3. **Execution Isolation**: Untrusted code is sandboxed (`F`), while logs (`G`) remain in the Trusted Network to prevent tampering.
4. **Adversary Mitigation**: Red dashed lines represent potential attack vectors, emphasizing the need for enclave-based verification to prevent compromise.
The process highlights a **zero-trust architecture** where trust is earned through cryptographic proofs (e.g., PCR0, commit hashes) rather than implicit trust in network paths. The Enclave (`E`) serves as the critical trust anchor, ensuring secure execution and attestation even in untrusted environments.