## Diagram: Cloud Environment Secure Computation Flow
### Overview
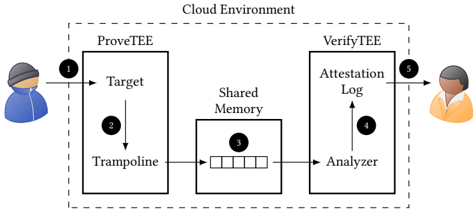
The image is a technical diagram illustrating a secure computation or attestation process within a "Cloud Environment." It depicts a two-phase workflow involving a "ProveTEE" component and a "VerifyTEE" component, connected via "Shared Memory." The process is initiated by a user (left) and results in an output to another user (right). The diagram uses numbered steps (1-5) to indicate the sequence of operations.
### Components/Axes
The diagram is segmented into three primary regions within a dashed boundary labeled "Cloud Environment":
1. **Left Region (ProveTEE):** A rectangular box labeled "ProveTEE." Inside, it contains two elements: "Target" (top) and "Trampoline" (bottom), connected by a downward arrow.
2. **Center Region (Shared Memory):** A rectangular box labeled "Shared Memory." Inside, it contains a grid of five empty squares, representing a data structure or buffer.
3. **Right Region (VerifyTEE):** A rectangular box labeled "VerifyTEE." Inside, it contains two elements: "Analyzer" (bottom) and "Attestation Log" (top), connected by an upward arrow.
**Flow Indicators (Numbered Steps):**
* **Step 1:** An arrow originates from a user icon (person in blue) on the far left and points to the "ProveTEE" box.
* **Step 2:** A numbered circle "2" is placed next to the "Target" element inside "ProveTEE."
* **Step 3:** A numbered circle "3" is placed inside the "Shared Memory" box, over the grid. An arrow points from the "Trampoline" element in "ProveTEE" to the "Shared Memory" box.
* **Step 4:** A numbered circle "4" is placed next to the "Analyzer" element inside "VerifyTEE." An arrow points from the "Shared Memory" box to the "Analyzer."
* **Step 5:** An arrow originates from the "VerifyTEE" box and points to a second user icon (person in orange) on the far right. A numbered circle "5" is placed near this arrow.
### Detailed Analysis
The diagram outlines a sequential, five-step process:
1. **Initiation (Step 1):** A user (blue icon) submits a request or data to the "ProveTEE" component within the cloud environment.
2. **Processing in ProveTEE (Step 2):** The "Target" element within "ProveTEE" is activated. The flow then moves to the "Trampoline" element.
3. **Data Transfer via Shared Memory (Step 3):** The "Trampoline" writes data to the "Shared Memory" structure (the 5-square grid). This acts as an intermediary communication channel.
4. **Verification in VerifyTEE (Step 4):** The "Analyzer" element within "VerifyTEE" reads the data from "Shared Memory." It processes this data to generate an "Attestation Log."
5. **Output (Step 5):** The "Attestation Log" is delivered to a second user (orange icon), presumably for verification or audit purposes.
**Spatial Grounding:** The "ProveTEE" is positioned on the left side of the cloud environment, "Shared Memory" is centrally located, and "VerifyTEE" is on the right. The numbered steps are placed in close proximity to the components they reference (e.g., circle "2" is adjacent to "Target").
### Key Observations
* **Component Isolation:** The architecture clearly separates the proving phase ("ProveTEE") from the verification phase ("VerifyTEE"), with "Shared Memory" as the sole, controlled interface between them.
* **Asymmetric User Roles:** The two user icons are distinct (blue vs. orange), suggesting different roles—possibly a "client" who initiates the process and an "auditor" or "relying party" who receives the attestation.
* **Abstract Data Representation:** The "Shared Memory" is depicted as a simple grid, abstracting the specific data format. The "Trampoline" and "Analyzer" are functional labels, not specific technical implementations.
* **Unidirectional Flow:** The overall data flow is strictly left-to-right, from the initiating user through the proving system, to the shared memory, to the verifying system, and finally to the receiving user.
### Interpretation
This diagram represents a **Trusted Execution Environment (TEE) attestation or remote verification protocol**. The "ProveTEE" likely executes a computation or holds sensitive data within a secure enclave. The "Trampoline" may be a secure gateway or shim that prepares data for output. The "Shared Memory" is a secure, isolated channel for passing information between the two TEEs. The "Analyzer" in the "VerifyTEE" validates the integrity or correctness of the computation/data from the "ProveTEE," producing a cryptographically verifiable "Attestation Log."
The process demonstrates a **separation of concerns** for security: the entity performing the sensitive operation (ProveTEE) is distinct from the entity verifying it (VerifyTEE). This pattern is common in confidential computing, where a cloud provider might host the TEEs, but the attestation log allows an external user to verify that the computation was performed correctly and securely without trusting the cloud infrastructure itself. The numbered steps provide a clear, auditable trail of the data's journey through the secure system.