TECHNICAL ASSET FINGERPRINT
0590463b194110ac863050e0
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
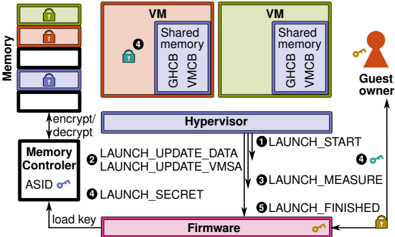
## System Security Diagram: Virtual Machine Launch Process
### Overview
The image is a diagram illustrating a secure virtual machine (VM) launch process, emphasizing memory encryption and integrity. It depicts the interaction between various components, including memory, memory controller, hypervisor, firmware, and the guest owner. The diagram highlights the steps involved in launching a VM, focusing on security measures like encryption, measurement, and secret management.
### Components/Axes
* **Memory:** Stack of memory blocks, each potentially encrypted (indicated by lock icons). The stack has three blocks, colored green, red, and blue from top to bottom.
* **VM (Virtual Machine):** Two VM blocks, colored orange and green. Each contains "Shared memory", "GHCB", and "VMCB".
* **Guest Owner:** A figure representing the guest owner, holding a key.
* **Hypervisor:** A central component mediating access between VMs and the underlying hardware.
* **Memory Controller:** Responsible for encrypting/decrypting memory. It has an "ASID" (Address Space Identifier) and a key icon.
* **Firmware:** The lowest-level software, responsible for initializing the system. It also has a key icon.
* **Numbered Arrows:** Indicate the sequence of steps in the VM launch process.
### Detailed Analysis
1. **Memory:**
* The memory stack shows three blocks, each with a lock icon, suggesting encryption.
* The blocks are colored green (top), red (middle), and blue (bottom).
2. **VMs:**
* Two VMs are shown, one orange and one green.
* Each VM contains "Shared memory", "GHCB", and "VMCB".
* The orange VM has a blue lock icon.
3. **Hypervisor:**
* Positioned centrally, mediating access between VMs and hardware.
4. **Memory Controller:**
* Connected to the memory stack and the hypervisor.
* Handles encryption/decryption of memory.
* Has an "ASID" and a key icon.
5. **Firmware:**
* Located at the bottom of the diagram.
* Connected to the memory controller and the hypervisor.
* Has a key icon.
6. **Guest Owner:**
* Located on the right side of the diagram.
* Connected to the hypervisor.
* Holds a key.
7. **Launch Process Steps:**
* **① LAUNCH\_START:** Arrow from Hypervisor to Firmware.
* **② LAUNCH\_UPDATE\_DATA, LAUNCH\_UPDATE\_VMSA:** Arrow from Hypervisor to Firmware.
* **③ LAUNCH\_MEASURE:** Arrow from Hypervisor to Firmware.
* **④ LAUNCH\_SECRET:** Arrow from Hypervisor to Firmware. A blue key is associated with this step, also present in the orange VM.
* **⑤ LAUNCH\_FINISHED:** Arrow from Hypervisor to Firmware.
8. **Other Connections:**
* "encrypt/decrypt" arrow between Memory Controller and Memory.
* "load key" arrow between Firmware and Memory Controller.
* Arrow from Guest Owner to Hypervisor.
### Key Observations
* The diagram emphasizes security through encryption (lock icons) and controlled access (Hypervisor).
* The launch process involves multiple steps, each potentially involving security checks or updates.
* The Firmware plays a crucial role in the launch process, interacting with the Hypervisor and Memory Controller.
* The Guest Owner interacts with the Hypervisor, likely for VM management.
### Interpretation
The diagram illustrates a secure VM launch process, highlighting the importance of memory encryption, integrity checks, and controlled access. The Hypervisor acts as a central mediator, ensuring that the VM is launched securely. The Firmware plays a critical role in initializing the system and loading keys. The numbered steps indicate a sequence of actions that must be performed to ensure a secure launch. The presence of lock icons on memory blocks and VMs suggests that encryption is used to protect sensitive data. The "LAUNCH\_MEASURE" step indicates that the system measures the VM's state to ensure its integrity. The "LAUNCH\_SECRET" step suggests that secrets are securely managed during the launch process. The overall process aims to prevent unauthorized access to the VM and protect it from tampering.
DECODING INTELLIGENCE...
EXPERT: gemma-3-27b-it-free VERSION 1
RUNTIME: google-free/gemma-3-27b-it
INTEL_VERIFIED
\n
## Diagram: Secure Virtual Machine Launch Process
### Overview
The image depicts a diagram illustrating the secure launch process of two Virtual Machines (VMs) managed by a Hypervisor, with interactions involving Firmware and a Memory Controller. The diagram highlights the encryption/decryption flow and the sequence of launch stages. The diagram is oriented horizontally, with components stacked vertically.
### Components/Axes
The diagram includes the following components:
* **Memory:** Represented as a stack of four locked containers on the left side, labeled "Memory".
* **VMs (Virtual Machines):** Two rectangular blocks, one orange and one green, labeled "VM". Each VM contains "Shared memory", "GHCB", and "VMCB".
* **Hypervisor:** A large blue rectangular block positioned between the VMs and the Firmware.
* **Memory Controller:** A rectangular block below the Hypervisor, labeled "Memory Controller" and containing "ASID on".
* **Firmware:** A large pink rectangular block at the bottom of the diagram.
* **Guest Owner:** A small figure with a key on the right side of the diagram.
* **Launch Stages:** Numbered circles (1-5) with associated labels indicating the launch process steps.
* **Arrows:** Indicate the flow of data and control between components.
* **Locks:** Represent security states.
### Detailed Analysis or Content Details
The diagram illustrates the following process:
1. **LAUNCH\_START (1):** An arrow originates from the Hypervisor and points towards the Guest Owner, with a lock symbol at the end.
2. **LAUNCH\_UPDATE\_DATA (2):** An arrow originates from the Hypervisor and points towards the Memory Controller.
3. **LAUNCH\_MEASURE (3):** An arrow originates from the Hypervisor and points towards the Guest Owner, with a lock symbol at the end.
4. **LAUNCH\_SECRET (4):** An arrow originates from the Memory Controller and points towards the Hypervisor, with a key symbol at the end. The Memory Controller has "ASID on" indicated. The VMs each have a lock symbol (4) within them.
5. **LAUNCH\_FINISHED (5):** An arrow originates from the Hypervisor and points towards the Firmware, with a lock symbol at the end.
6. **Encryption/Decryption:** A bidirectional arrow labeled "encrypt/decrypt" connects the Memory and the Hypervisor.
7. **Load Key:** An arrow labeled "load key" connects the Firmware and the Memory Controller.
The Memory stack has four containers, each with a lock symbol. The VMs are colored orange and green, each containing "Shared memory", "GHCB", and "VMCB". The Guest Owner holds a key.
### Key Observations
* The diagram emphasizes the secure launch process, with locks representing security states at various stages.
* The Memory Controller plays a role in loading keys and interacting with the Hypervisor during the launch process.
* The Hypervisor acts as a central component, coordinating the launch stages and managing the VMs.
* The Firmware is involved in the final stage of the launch process.
* The Guest Owner is involved in the start and measure stages.
### Interpretation
The diagram illustrates a secure virtual machine launch process that leverages hardware-based security features like memory encryption and ASID (Address Space ID) to protect the VMs from unauthorized access. The process begins with the Hypervisor initiating the launch sequence, involving the Firmware for key loading and the Memory Controller for managing memory access. The launch stages (START, UPDATE\_DATA, MEASURE, SECRET, FINISHED) represent a series of checks and validations to ensure the integrity and confidentiality of the VMs. The Guest Owner is involved in the initial and measurement phases, suggesting a role in attestation or verification. The locks symbolize the security measures in place at each stage, and the key represents the cryptographic keys used for encryption and authentication. The diagram suggests a trusted computing base (TCB) encompassing the Firmware, Memory Controller, Hypervisor, and potentially the Guest Owner, working together to establish a secure environment for the VMs. The use of ASID in the Memory Controller indicates memory isolation between VMs, enhancing security. The encryption/decryption flow between Memory and Hypervisor suggests that the VM's memory is encrypted to protect its contents from unauthorized access. The diagram is a high-level overview and does not provide specific details about the cryptographic algorithms or security protocols used.
DECODING INTELLIGENCE...
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
\n
## Technical Diagram: Secure Virtual Machine Launch Architecture (AMD SEV-SNP Inspired)
### Overview
This image is a technical block diagram illustrating the components and data flow for launching and managing secure virtual machines (VMs) with hardware-assisted memory encryption and attestation. The architecture depicts a chain of trust involving firmware, a hypervisor, a memory controller, and guest VMs, with a focus on secure launch sequences and memory isolation.
### Components/Axes
The diagram is organized into several key functional blocks and regions:
1. **Memory (Top-Left):** A vertical stack of four rectangular blocks representing system memory. Each block has a lock icon (green, red, blue, black) on its left side, indicating encrypted or protected memory regions.
2. **Memory Controller (Left):** A block labeled "Memory Controller" with an "ASID" (Address Space Identifier) label and a key icon. An arrow labeled "load key" points from the Firmware to this controller. It has a bidirectional arrow labeled "encrypt/decrypt" connecting it to the Memory block.
3. **Hypervisor (Center):** A wide, central block labeled "Hypervisor". It is the orchestrator of the launch process, sending commands to the Firmware and receiving measurements.
4. **Firmware (Bottom):** A long block labeled "Firmware" at the bottom of the diagram. It interacts with the Hypervisor, Memory Controller, and Guest Owner. It has key and lock icons associated with it.
5. **Virtual Machines (Top-Right):** Two side-by-side blocks, each labeled "VM".
* Each VM contains a "Shared memory" sub-block.
* Each VM contains two smaller blocks labeled "GHCB" (Guest-Hypervisor Communication Block) and "VMCB" (Virtual Machine Control Block).
* The left VM has a lock icon next to its "Shared memory" block.
6. **Guest Owner (Far Right):** An icon of a person with a key, labeled "Guest owner". This entity is involved in the attestation and secret injection phase.
### Detailed Analysis
The diagram details a multi-step, numbered launch and measurement process (steps ① through ⑥) and subsequent attestation.
**Launch Sequence Flow:**
1. **① LAUNCH_START:** An arrow flows from the Hypervisor to the Firmware, initiating the VM launch.
2. **② LAUNCH_MEASURE:** An arrow flows from the Firmware back to the Hypervisor, likely providing an initial measurement (hash) of the VM's initial state.
3. **③ LAUNCH_UPDATE_DATA:** An arrow flows from the Hypervisor to the Firmware, used to provide initial data (e.g., OS image) to the VM.
4. **④ LAUNCH_UPDATE_VMSA:** An arrow flows from the Hypervisor to the Firmware, used to update the VM's State Save Area (VMSA), which contains register state.
5. **⑤ LAUNCH_SECRET:** An arrow flows from the Hypervisor to the Firmware, used to inject secrets (e.g., attestation keys) into the VM.
6. **⑥ LAUNCH_FINISHED:** An arrow flows from the Firmware to the Hypervisor, signaling the completion of the secure launch process.
**Attestation and Key Flow:**
* A key icon and an arrow flow from the **Guest owner** to the **Firmware**, representing the owner providing a key or credential for attestation.
* A lock icon is shown on the **Firmware** block, indicating it is a trusted entity.
* The **Firmware** has a "load key" arrow pointing to the **Memory Controller**, establishing the encryption key for memory accesses.
* The **Memory Controller** performs "encrypt/decrypt" operations on data going to/from the main **Memory** blocks.
**VM Internal Structure:**
* Each VM has a **Shared memory** region for communication with the hypervisor.
* The **GHCB** is a standardized page for communication between the guest VM and the hypervisor.
* The **VMCB** is a hardware-defined structure that holds the state of the virtual CPU for the VM.
### Key Observations
* **Chain of Trust:** The process establishes a clear chain from the hardware **Firmware** (root of trust) through the **Hypervisor** to the **VMs**.
* **Memory Encryption:** The **Memory Controller** is central to runtime security, transparently encrypting/decrypting all VM memory accesses using a key loaded from secure firmware.
* **Attestation Model:** The **Guest owner** is an external entity that participates in attestation, receiving measurements (from step ②) and providing secrets (step ⑤) to establish trust in the VM's environment.
* **Component Isolation:** The two VMs are depicted as separate, isolated containers, each with its own communication blocks (GHCB, VMCB) and shared memory.
* **Symbolism:** Lock icons consistently represent protected or encrypted resources (memory regions, firmware). Key icons represent cryptographic keys or secrets being loaded or transferred.
### Interpretation
This diagram illustrates a hardware-based confidential computing architecture, strongly resembling AMD's Secure Encrypted Virtualization-Secure Nested Paging (SEV-SNP) technology. The core principle is to protect VM data not only at rest (in encrypted memory) but also during execution and launch.
* **Security Model:** The hypervisor, while managing VMs, is kept *outside* the trust boundary for the VM's memory contents. It can schedule and manage the VM but cannot inspect its private memory or CPU state, which are encrypted and controlled by the secure processor (firmware).
* **Process Significance:** The numbered steps (①-⑥) represent a measured and attested launch. Each step updates the VM's state in a controlled manner, and the initial measurement (②) allows the Guest Owner to cryptographically verify that the VM was launched correctly on genuine hardware before trusting it with secrets (⑤).
* **Role of Components:** The **Firmware** acts as the hardware root of trust, validating commands from the hypervisor and managing the secure processor. The **Memory Controller** enforces memory encryption policies based on the ASID, ensuring isolation between different VMs and the hypervisor itself.
* **Anomaly/Notable Design:** The "Shared memory" within each VM is a designated region that is *not* encrypted with the VM's private key, allowing for controlled, performant communication with the hypervisor for I/O and management operations, representing a necessary trade-off between security and functionality.
In essence, the diagram details a system where a cloud provider (operating the hypervisor) can host VMs for customers (Guest Owners) who can verify their workload's integrity and confidentiality, even from the cloud provider itself.
DECODING INTELLIGENCE...
EXPERT: nemotron-free VERSION 1
RUNTIME: free/nvidia/nemotron-nano-12b-v2-vl:free
INTEL_VERIFIED
## System Architecture Diagram: Secure Virtual Machine Launch Process
### Overview
The diagram illustrates a secure virtual machine (VM) launch process involving memory encryption, hypervisor operations, firmware interactions, and guest owner authentication. Key components include memory regions, VMs with shared memory, a hypervisor, firmware, and a guest owner entity. Arrows represent data flow and process steps.
### Components/Axes
1. **Memory**:
- Stacked blocks with colored locks (green, red, blue, black) labeled "Memory."
- Arrows labeled "encrypt/decrypt" connect to the Memory Controller.
2. **VMs**:
- Two VM boxes (orange and green) labeled "VM" with "Shared memory" sub-boxes containing "GHCB" and "VM CB."
3. **Hypervisor**:
- Central purple box labeled "Hypervisor" with numbered steps:
1. LAUNCH_START
2. LAUNCH_UPDATE_DATA
3. LAUNCH_UPDATE_VMSA
4. LAUNCH_SECRET
5. LAUNCH_FINISHED
4. **Firmware**:
- Pink box labeled "Firmware" with a key icon.
5. **Guest Owner**:
- Red silhouette with a key icon, connected to Firmware via an arrow labeled "load key."
6. **Memory Controller**:
- Black box labeled "Memory Controller" with "ASID" and a key icon.
### Detailed Analysis
- **Memory**:
- Four memory regions with distinct locks (green, red, blue, black) suggest tiered security or access levels.
- Encryption/decryption arrows indicate dynamic memory protection.
- **VMs**:
- Shared memory regions (GHCB, VM CB) imply inter-VM communication or resource sharing.
- Orange and green colors may differentiate VM types or security domains.
- **Hypervisor**:
- Sequential steps (1–5) outline VM launch phases, including data updates, measurement, and secret handling.
- Step 3 ("LAUNCH_MEASURE") likely involves integrity checks.
- **Firmware**:
- Key icon suggests cryptographic operations or secure boot functionality.
- **Guest Owner**:
- Key icon implies ownership verification or authorization.
- **Memory Controller**:
- ASID (Address Space Identifier) and key icon indicate memory isolation and encryption key management.
### Key Observations
- **Sequential Process**: VM launch follows a strict workflow from start to finish, with hypervisor mediating security-critical steps.
- **Shared Memory Risks**: GHCB/VM CB in VMs could be attack vectors; hypervisor updates (steps 2–4) likely mitigate this.
- **Key Management**: Keys are central to encryption (Memory Controller), firmware, and guest owner authentication.
- **Color Coding**:
- Green (Memory), red/orange (VMs), purple (Hypervisor), pink (Firmware), black (Memory Controller) visually segregate components.
- No explicit legend, but colors align with component roles (e.g., red for "Guest Owner" matches the silhouette).
### Interpretation
This diagram represents a **secure enclave architecture** for VMs, emphasizing memory encryption, hypervisor-mediated security, and firmware/firmware-rooted trust. The Guest Owner’s key suggests a hardware-rooted identity (e.g., TPM or secure element) validating VM launches. The hypervisor’s role in updating data and measuring VM state aligns with attestation processes, ensuring VMs are launched in a trusted state. The Memory Controller’s ASID and key management highlight memory-level isolation, critical for preventing side-channel attacks. The shared memory in VMs (GHCB/VM CB) may enable secure inter-VM communication but requires hypervisor oversight to prevent leaks. The absence of explicit numerical data suggests this is a conceptual flow rather than a performance benchmark.
DECODING INTELLIGENCE...