\n
## Diagram: Secure Virtual Machine Launch Process
### Overview
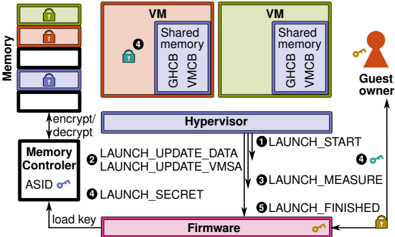
The image depicts a diagram illustrating the secure launch process of two Virtual Machines (VMs) managed by a Hypervisor, with interactions involving Firmware and a Memory Controller. The diagram highlights the encryption/decryption flow and the sequence of launch stages. The diagram is oriented horizontally, with components stacked vertically.
### Components/Axes
The diagram includes the following components:
* **Memory:** Represented as a stack of four locked containers on the left side, labeled "Memory".
* **VMs (Virtual Machines):** Two rectangular blocks, one orange and one green, labeled "VM". Each VM contains "Shared memory", "GHCB", and "VMCB".
* **Hypervisor:** A large blue rectangular block positioned between the VMs and the Firmware.
* **Memory Controller:** A rectangular block below the Hypervisor, labeled "Memory Controller" and containing "ASID on".
* **Firmware:** A large pink rectangular block at the bottom of the diagram.
* **Guest Owner:** A small figure with a key on the right side of the diagram.
* **Launch Stages:** Numbered circles (1-5) with associated labels indicating the launch process steps.
* **Arrows:** Indicate the flow of data and control between components.
* **Locks:** Represent security states.
### Detailed Analysis or Content Details
The diagram illustrates the following process:
1. **LAUNCH\_START (1):** An arrow originates from the Hypervisor and points towards the Guest Owner, with a lock symbol at the end.
2. **LAUNCH\_UPDATE\_DATA (2):** An arrow originates from the Hypervisor and points towards the Memory Controller.
3. **LAUNCH\_MEASURE (3):** An arrow originates from the Hypervisor and points towards the Guest Owner, with a lock symbol at the end.
4. **LAUNCH\_SECRET (4):** An arrow originates from the Memory Controller and points towards the Hypervisor, with a key symbol at the end. The Memory Controller has "ASID on" indicated. The VMs each have a lock symbol (4) within them.
5. **LAUNCH\_FINISHED (5):** An arrow originates from the Hypervisor and points towards the Firmware, with a lock symbol at the end.
6. **Encryption/Decryption:** A bidirectional arrow labeled "encrypt/decrypt" connects the Memory and the Hypervisor.
7. **Load Key:** An arrow labeled "load key" connects the Firmware and the Memory Controller.
The Memory stack has four containers, each with a lock symbol. The VMs are colored orange and green, each containing "Shared memory", "GHCB", and "VMCB". The Guest Owner holds a key.
### Key Observations
* The diagram emphasizes the secure launch process, with locks representing security states at various stages.
* The Memory Controller plays a role in loading keys and interacting with the Hypervisor during the launch process.
* The Hypervisor acts as a central component, coordinating the launch stages and managing the VMs.
* The Firmware is involved in the final stage of the launch process.
* The Guest Owner is involved in the start and measure stages.
### Interpretation
The diagram illustrates a secure virtual machine launch process that leverages hardware-based security features like memory encryption and ASID (Address Space ID) to protect the VMs from unauthorized access. The process begins with the Hypervisor initiating the launch sequence, involving the Firmware for key loading and the Memory Controller for managing memory access. The launch stages (START, UPDATE\_DATA, MEASURE, SECRET, FINISHED) represent a series of checks and validations to ensure the integrity and confidentiality of the VMs. The Guest Owner is involved in the initial and measurement phases, suggesting a role in attestation or verification. The locks symbolize the security measures in place at each stage, and the key represents the cryptographic keys used for encryption and authentication. The diagram suggests a trusted computing base (TCB) encompassing the Firmware, Memory Controller, Hypervisor, and potentially the Guest Owner, working together to establish a secure environment for the VMs. The use of ASID in the Memory Controller indicates memory isolation between VMs, enhancing security. The encryption/decryption flow between Memory and Hypervisor suggests that the VM's memory is encrypted to protect its contents from unauthorized access. The diagram is a high-level overview and does not provide specific details about the cryptographic algorithms or security protocols used.