## Scatter Plots: Timing vs. Guess for Cookie Bytes
### Overview
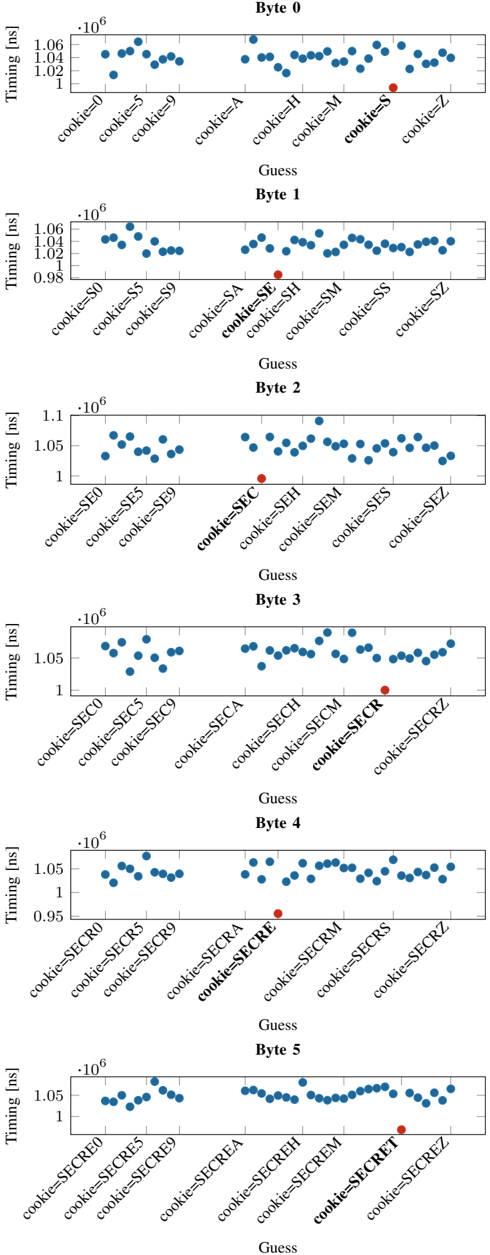
The image presents six separate scatter plots, each representing the timing (in nanoseconds) required to guess a specific byte of a "cookie". Each plot focuses on a different byte (Byte 0 through Byte 5). The x-axis represents the "Guess" (possible values for the byte), and the y-axis represents the "Timing" (in nanoseconds). Each plot displays data points for various guesses, with the color of the points varying between plots.
### Components/Axes
* **Title:** Each plot is labeled with "Byte [Number]" (0-5) at the top-right corner.
* **X-axis:** "Guess" - Categorical values representing possible byte values. The values are:
* Byte 0: cookie=0, cookie=5, cookie=9, cookie=A, cookie=H, cookie=M, cookie=S, cookie=Z
* Byte 1: cookie=S0, cookie=S5, cookie=S9, cookie=SA, cookie=SE, cookie=SH, cookie=SM, cookie=SS, cookie=SZ
* Byte 2: cookie=SE0, cookie=SE5, cookie=SE9, cookie=SEC, cookie=SEH, cookie=SEM, cookie=SES, cookie=SEZ
* Byte 3: cookie=SEC0, cookie=SEC5, cookie=SEC9, cookie=SECA, cookie=SECH, cookie=SECM, cookie=SECR, cookie=SECZ
* Byte 4: cookie=SECR0, cookie=SECR5, cookie=SECR9, cookie=SECRA, cookie=SECRE, cookie=SECRM, cookie=SECRS, cookie=SECRZ
* Byte 5: cookie=SECRED, cookie=SECRE5, cookie=SECRE9, cookie=SECREA, cookie=SECREH, cookie=SECREM, cookie=SECRES, cookie=SECREZ
* **Y-axis:** "Timing (ns)" - Scale ranges from approximately 0.98 x 10<sup>6</sup> to 1.1 x 10<sup>6</sup> nanoseconds.
* **Data Points:** Scatter points representing the timing for each guess.
* **Colors:** Each byte plot uses a distinct color for its data points:
* Byte 0: Blue
* Byte 1: Orange
* Byte 2: Purple
* Byte 3: Red
* Byte 4: Green
* Byte 5: Teal
### Detailed Analysis or Content Details
**Byte 0 (Blue):** The timing appears relatively constant across all guesses, hovering around 1.03 x 10<sup>6</sup> ns. There's minimal variation.
* Approximate values: ~1.03 x 10<sup>6</sup> ns for all guesses.
**Byte 1 (Orange):** The timing generally increases as the guess value increases.
* cookie=S0: ~0.985 x 10<sup>6</sup> ns
* cookie=S5: ~0.99 x 10<sup>6</sup> ns
* cookie=S9: ~1.01 x 10<sup>6</sup> ns
* cookie=SA: ~1.02 x 10<sup>6</sup> ns
* cookie=SE: ~1.03 x 10<sup>6</sup> ns
* cookie=SH: ~1.04 x 10<sup>6</sup> ns
* cookie=SM: ~1.05 x 10<sup>6</sup> ns
* cookie=SS: ~1.06 x 10<sup>6</sup> ns
* cookie=SZ: ~1.06 x 10<sup>6</sup> ns
**Byte 2 (Purple):** Similar to Byte 1, the timing generally increases with the guess value.
* cookie=SE0: ~1.01 x 10<sup>6</sup> ns
* cookie=SE5: ~1.02 x 10<sup>6</sup> ns
* cookie=SE9: ~1.04 x 10<sup>6</sup> ns
* cookie=SEC: ~1.05 x 10<sup>6</sup> ns
* cookie=SEH: ~1.06 x 10<sup>6</sup> ns
* cookie=SEM: ~1.06 x 10<sup>6</sup> ns
* cookie=SES: ~1.07 x 10<sup>6</sup> ns
* cookie=SEZ: ~1.08 x 10<sup>6</sup> ns
**Byte 3 (Red):** Most guesses have similar timing around 1.05 x 10<sup>6</sup> ns. However, cookie=SECR is a clear outlier.
* cookie=SEC0: ~1.01 x 10<sup>6</sup> ns
* cookie=SEC5: ~1.02 x 10<sup>6</sup> ns
* cookie=SEC9: ~1.03 x 10<sup>6</sup> ns
* cookie=SECA: ~1.04 x 10<sup>6</sup> ns
* cookie=SECH: ~1.04 x 10<sup>6</sup> ns
* cookie=SECM: ~1.05 x 10<sup>6</sup> ns
* cookie=SECR: ~0.99 x 10<sup>6</sup> ns (Outlier - significantly lower timing)
* cookie=SECZ: ~1.06 x 10<sup>6</sup> ns
**Byte 4 (Green):** Timing increases with the guess value.
* cookie=SECR0: ~0.98 x 10<sup>6</sup> ns
* cookie=SECR5: ~0.99 x 10<sup>6</sup> ns
* cookie=SECR9: ~1.01 x 10<sup>6</sup> ns
* cookie=SECRA: ~1.02 x 10<sup>6</sup> ns
* cookie=SECRE: ~1.03 x 10<sup>6</sup> ns
* cookie=SECRM: ~1.04 x 10<sup>6</sup> ns
* cookie=SECRS: ~1.05 x 10<sup>6</sup> ns
* cookie=SECRZ: ~1.05 x 10<sup>6</sup> ns
**Byte 5 (Teal):** Timing is relatively constant, with a slight increase towards the end.
* cookie=SECRED: ~1.03 x 10<sup>6</sup> ns
* cookie=SECRE5: ~1.04 x 10<sup>6</sup> ns
* cookie=SECRE9: ~1.04 x 10<sup>6</sup> ns
* cookie=SECREA: ~1.05 x 10<sup>6</sup> ns
* cookie=SECREH: ~1.05 x 10<sup>6</sup> ns
* cookie=SECREM: ~1.05 x 10<sup>6</sup> ns
* cookie=SECRES: ~1.05 x 10<sup>6</sup> ns
* cookie=SECREZ: ~1.06 x 10<sup>6</sup> ns
### Key Observations
* Byte 0 shows almost no timing variation, suggesting it's easily guessed or has a very predictable timing.
* Bytes 1, 2, and 4 exhibit a positive correlation between the guess value and timing. Higher guesses take longer.
* Byte 3 has a significant outlier (cookie=SECR) with a much lower timing than other guesses. This could indicate a vulnerability or a specific characteristic of that byte value.
* Byte 5 shows minimal variation, similar to Byte 0.
### Interpretation
The plots likely represent a timing attack against a system that uses a "cookie" for authentication or session management. The goal of the attack is to determine the value of each byte of the cookie by measuring the time it takes for the server to respond to different guesses.
The consistent timing for Byte 0 and Byte 5 suggests these bytes might be static or have a simple validation process. The increasing timing for Bytes 1, 2, and 4 indicates that the server performs more complex operations or checks as the guess value increases. This could be due to conditional statements or more extensive validation routines.
The outlier in Byte 3 (cookie=SECR) is particularly interesting. It suggests that guessing this specific value is significantly faster than guessing others. This could be because:
1. The server short-circuits the validation process for this value.
2. The value is a default or commonly used value.
3. There's a bug in the server's code that causes it to respond faster for this specific value.
This outlier represents a potential vulnerability that an attacker could exploit to quickly determine the value of this byte. The data suggests that the cookie's bytes are not equally secure, and some bytes are more susceptible to timing attacks than others. Further investigation into the server-side code is needed to understand the cause of the outlier and mitigate the vulnerability.