\n
## Diagram: Evasion Algorithm Workflow
### Overview
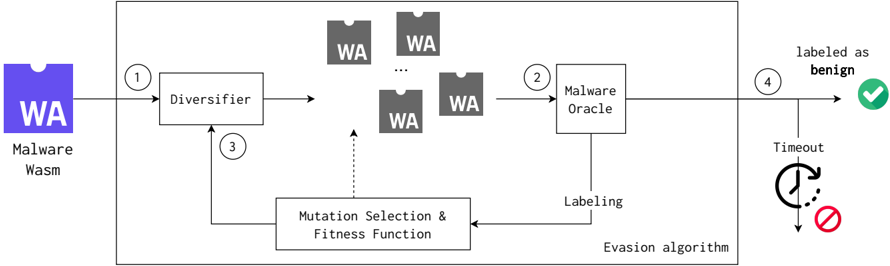
The image depicts a diagram illustrating an evasion algorithm workflow, likely for malware. The process begins with a "Malware Wasm" input and cycles through diversification, malware oracle evaluation, and mutation selection to ultimately attempt to evade detection and be labeled as benign.
### Components/Axes
The diagram consists of the following components:
* **Malware Wasm (Input):** A purple rectangular block labeled "WA Malware Wasm".
* **Diversifier:** A rectangular block labeled "Diversifier".
* **Malware Oracle:** A rectangular block labeled "Malware Oracle".
* **Mutation Selection & Fitness Function:** A rectangular block labeled "Mutation Selection & Fitness Function".
* **Labeled as benign (Output):** A green checkmark within a circle, labeled "labeled as benign".
* **Timeout:** A red circle with a slash through it, and a circular arrow, labeled "Timeout".
* **Arrows:** Solid and dashed arrows indicating the flow of data and control.
* **"WA" blocks:** Multiple grey rectangular blocks labeled "WA", representing diversified malware samples.
The diagram is contained within a larger grey rectangular border. Numbered circles (1-4) are placed along the flow to indicate the sequence of operations.
### Detailed Analysis or Content Details
1. **Step 1:** The "Malware Wasm" (WA) input enters the "Diversifier". A solid arrow indicates the flow.
2. **Step 2:** The "Diversifier" outputs multiple instances of "WA" (diversified malware samples) to the "Malware Oracle". A solid arrow indicates the flow.
3. **Step 3:** A dashed arrow connects the "Mutation Selection & Fitness Function" back to the "Diversifier", indicating a feedback loop for mutation selection.
4. **Step 4:** The "Malware Oracle" outputs a labeling to either "labeled as benign" (green checkmark) or "Timeout" (red circle with slash and circular arrow). A solid arrow indicates the flow to the benign label.
The "Mutation Selection & Fitness Function" also has a solid arrow labeled "Labeling" connecting it to the "Malware Oracle". A separate arrow labeled "Evasion algorithm" connects the "Mutation Selection & Fitness Function" to the "Timeout" component.
### Key Observations
The diagram highlights a closed-loop system where malware is diversified, evaluated by an oracle, and then mutated based on the evaluation results. The goal is to evade detection and be labeled as benign. The "Timeout" component suggests a limit on the number of iterations or the time allowed for the evasion process. The dashed arrow from the "Mutation Selection & Fitness Function" to the "Diversifier" indicates a feedback mechanism for refining the diversification process.
### Interpretation
This diagram illustrates a common approach to adversarial machine learning, specifically in the context of malware evasion. The "Malware Oracle" represents a detection system (e.g., an antivirus engine or a machine learning classifier). The "Diversifier" generates variations of the malware, and the "Mutation Selection & Fitness Function" guides the evolution of the malware to maximize its chances of evading detection. The feedback loop ensures that the malware adapts to the detection system over time. The "Timeout" component is a practical consideration, preventing the algorithm from running indefinitely if it fails to find an evading variant. The entire process is an example of an evasion algorithm attempting to find inputs (malware variants) that are misclassified by the "Malware Oracle". The diagram suggests a dynamic and iterative process, where the malware is continuously refined to bypass security measures.