## Diagram: WebAssembly Malware Evasion Algorithm Flowchart
### Overview
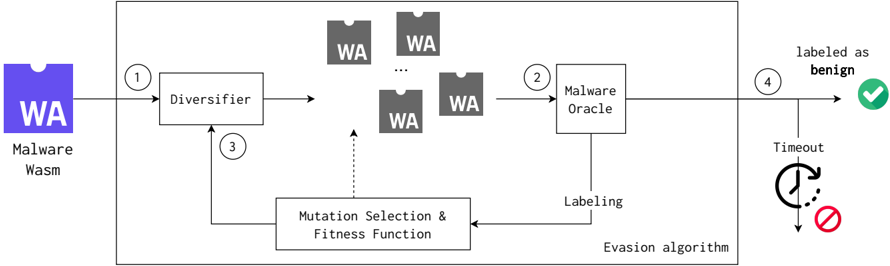
The image is a technical flowchart illustrating an automated evasion algorithm designed to mutate WebAssembly (Wasm) malware until it is classified as benign by a detection system (the "Malware Oracle"). The process is a closed-loop, iterative system contained within a main box labeled "Evasion algorithm."
### Components/Axes
The diagram is structured as a process flow with numbered steps (1-4) and distinct components:
**Input (Left Side):**
* **Component:** A blue, puzzle-piece-shaped icon labeled **"WA"**.
* **Text Below Icon:** "Malware Wasm". This is the initial malicious input.
**Main Process Box (Center):**
* **Title:** "Evasion algorithm" (text at the bottom-right of the box).
* **Components within the box:**
1. **Diversifier:** A rectangular process box. It receives input from the initial Malware Wasm (Step 1) and feedback from the Mutation Selection component (Step 3).
2. **WA Instances:** Multiple gray, puzzle-piece-shaped icons labeled **"WA"**. These represent the mutated variants generated by the Diversifier. An ellipsis ("...") indicates there can be many such instances.
3. **Malware Oracle:** A rectangular process box. It receives the mutated WA instances (Step 2) and outputs a "Labeling" decision.
4. **Mutation Selection & Fitness Function:** A rectangular process box. It receives the "Labeling" from the Malware Oracle and provides feedback (Step 3) to the Diversifier to guide future mutations.
**Output (Right Side):**
* **Path 1 (Success):** An arrow labeled **"labeled as benign"** leads to a green circle containing a white checkmark (✓).
* **Path 2 (Failure/Timeout):** An arrow labeled **"Timeout"** leads to a red circle containing a white prohibition sign (🚫). A dotted arrow with a clock icon points from the main path to this timeout condition.
**Flow & Labels:**
* **Step 1:** Arrow from "Malware Wasm" to "Diversifier".
* **Step 2:** Arrow from the collection of "WA" instances to "Malware Oracle".
* **Step 3:** Arrow from "Mutation Selection & Fitness Function" back to "Diversifier".
* **Step 4:** Arrow from "Malware Oracle" to the output decision point.
* **Key Label:** "Labeling" on the arrow from "Malware Oracle" to "Mutation Selection & Fitness Function".
### Detailed Analysis
The diagram depicts a four-stage, iterative feedback loop:
1. **Initialization (Step 1):** A known malicious WebAssembly module ("Malware Wasm") is fed into the system.
2. **Diversification (Step 1 -> WA Instances):** The **Diversifier** component applies mutations to the input malware, generating multiple variant WA instances. The goal is to create versions that may evade detection.
3. **Detection/Labeling (Step 2 -> Labeling):** Each mutated WA instance is submitted to the **Malware Oracle**. This component acts as a classifier or detector, outputting a "Labeling" decision (presumably "malicious" or "benign").
4. **Feedback & Optimization (Step 3):** The labeling result is fed into the **Mutation Selection & Fitness Function**. This component evaluates which mutations were successful (i.e., evaded detection) and uses a fitness function to guide the Diversifier. The feedback loop (Step 3) tells the Diversifier which types of mutations to apply more frequently in the next iteration.
5. **Termination (Step 4):** The process has two exit conditions:
* **Success:** If the Malware Oracle labels a variant as **"benign"**, the evasion is successful (green checkmark).
* **Failure:** If the process exceeds a **"Timeout"** (indicated by the clock icon), it terminates without success (red prohibition sign).
### Key Observations
* **Closed-Loop System:** The core of the algorithm is the feedback loop between the Malware Oracle's output and the Mutation Selection component, which directly influences the Diversifier. This is characteristic of evolutionary or genetic algorithms.
* **One-Way Flow to Oracle:** The mutated WA instances flow only *to* the Malware Oracle; there is no direct feedback from the Oracle to the Diversifier. All feedback is mediated through the "Mutation Selection & Fitness Function."
* **Visual Metaphor:** The use of puzzle-piece icons for "WA" suggests that the malware modules are components meant to fit into a larger system (the victim's environment or browser).
* **Timeout as a Constraint:** The inclusion of a "Timeout" condition indicates the evasion attempt is computationally bounded and may not always succeed within a given resource limit.
### Interpretation
This diagram illustrates an **adversarial machine learning or genetic programming approach to malware evasion**. The system's purpose is to automatically generate obfuscated or mutated versions of a WebAssembly malware sample that can bypass a specific detector (the Malware Oracle).
* **What it demonstrates:** It shows a method for *automating* the creation of evasion techniques, moving beyond manual obfuscation. The "Fitness Function" implies that mutations are not random but are scored based on their ability to fool the oracle, leading to increasingly effective evasive variants over successive generations.
* **Relationships:** The Malware Oracle is the adversary in this loop. The Mutation Selection component is the "brain" that learns from the oracle's behavior. The Diversifier is the "hands" that execute the mutation strategy.
* **Notable Implications:**
* **Security Arms Race:** This represents a tool in the ongoing arms race between malware authors and security vendors. If the Malware Oracle is a static analysis tool, this system could be used to probe its weaknesses and generate bypasses at scale.
* **Dependency on Oracle Quality:** The effectiveness of the entire evasion algorithm is critically dependent on the quality and consistency of the "Labeling" from the Malware Oracle. An oracle with inconsistent or easily gamed logic would lead to faster successful evasion.
* **Resource-Bounded Attack:** The "Timeout" element highlights that such automated attacks are not infinite; they are constrained by time or computational resources, which is a key defensive consideration.