## Flowchart: Malware Analysis System with Genetic Algorithm Components
### Overview
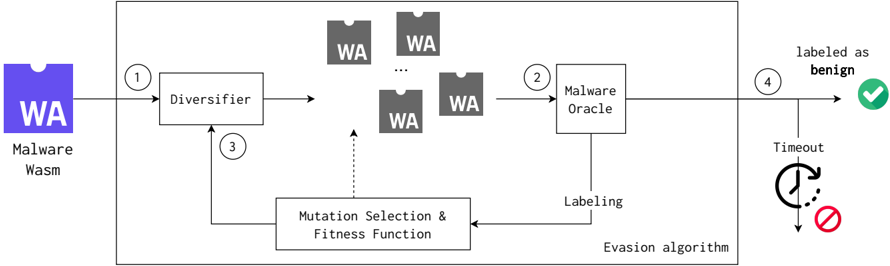
The flowchart depicts a malware analysis system that employs a genetic algorithm (GA) approach to evaluate and classify malware samples. The process involves iterative mutation, selection, and evasion testing to determine whether a sample is benign or malicious.
### Components/Axes
1. **Input**: "Malware Wasm" (purple box) - Entry point for WebAssembly (Wasm) malware samples.
2. **Diversifier** (step 1): Generates mutated variants of the input malware.
3. **Mutation Selection & Fitness Function** (step 3): Iterative loop refining mutations based on fitness criteria.
4. **Malware Oracle** (step 2): Evaluates mutated samples against malware signatures.
5. **Labeling**: Classifies samples as "benign" (green checkmark) or "timeout" (red cross).
6. **Evasion Algorithm**: Determines whether mutated samples evade detection.
### Detailed Analysis
- **Flow Direction**:
- Starts at "Malware Wasm" → "Diversifier" (step 1).
- Mutated samples (WA boxes) flow to "Malware Oracle" (step 2) for analysis.
- "Mutation Selection & Fitness Function" (step 3) loops back to the Diversifier, indicating iterative refinement.
- Final outcomes branch to "Labeling" (step 4), with two possible results:
- **Timeout** (red clock icon): Sample fails to evade detection within a time limit.
- **Labeled as benign** (green checkmark): Sample successfully evades detection.
- **Key Symbols**:
- **WA boxes**: Represent mutated malware variants.
- **Dashed arrow**: Indicates feedback loop between "Mutation Selection & Fitness Function" and "Diversifier".
- **Clock icon**: Represents a timeout threshold for evasion testing.
### Key Observations
1. **Iterative Process**: The system uses a genetic algorithm to iteratively refine malware mutations, suggesting an optimization loop for evasion.
2. **Branching Outcomes**: The final classification depends on the evasion algorithm's success, with a clear binary outcome (benign vs. timeout).
3. **Parallel Paths**: Multiple "WA" boxes indicate parallel testing of mutated samples against the Malware Oracle.
### Interpretation
This flowchart represents a **genetic algorithm-based malware analysis framework**. The system:
- **Evolves malware variants** through mutation and selection to test evasion capabilities.
- **Relies on a Malware Oracle** (likely a signature-based detection system) to evaluate samples.
- **Classifies outcomes** based on whether mutations successfully evade detection within a defined timeframe.
The "timeout" outcome implies a trade-off between computational resources and detection evasion success. The green checkmark for "benign" suggests the system identifies samples that avoid detection, potentially for benign purposes (e.g., testing security tools). The iterative loop highlights the importance of balancing mutation diversity with fitness criteria to optimize evasion strategies.