## Diagram: Trust Vulnerability Map in Retrieval-Augmented Generation Systems
### Overview
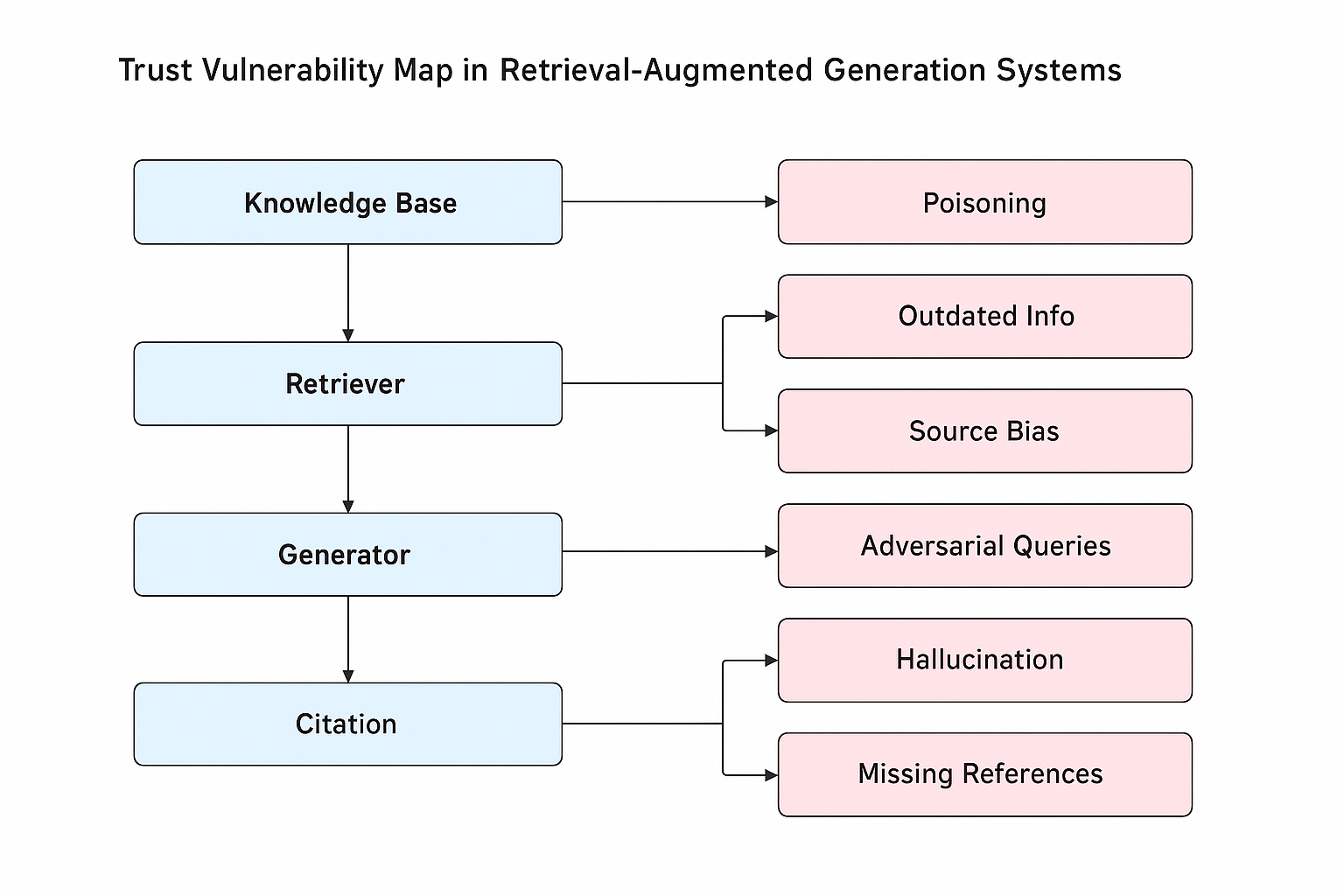
The image is a flowchart illustrating potential vulnerabilities in a Retrieval-Augmented Generation (RAG) system. The diagram outlines the flow of information from the Knowledge Base to Citation, highlighting potential trust issues at each stage. The diagram uses blue rounded rectangles to represent components of the RAG system and pink rounded rectangles to represent vulnerabilities.
### Components/Axes
* **Title:** Trust Vulnerability Map in Retrieval-Augmented Generation Systems
* **Nodes (Blue):**
* Knowledge Base (top)
* Retriever (below Knowledge Base)
* Generator (below Retriever)
* Citation (below Generator)
* **Nodes (Pink):**
* Poisoning (right of Knowledge Base)
* Outdated Info (right of Retriever, top)
* Source Bias (right of Retriever, bottom)
* Adversarial Queries (right of Generator)
* Hallucination (right of Citation, top)
* Missing References (right of Citation, bottom)
* **Arrows:** Arrows indicate the flow of information or potential impact.
### Detailed Analysis
The diagram shows a sequential flow from the Knowledge Base down to Citation. Each stage in the RAG system (Knowledge Base, Retriever, Generator, Citation) is linked to one or more potential vulnerabilities.
* **Knowledge Base** is linked to **Poisoning**.
* **Retriever** is linked to **Outdated Info** and **Source Bias**.
* **Generator** is linked to **Adversarial Queries**.
* **Citation** is linked to **Hallucination** and **Missing References**.
### Key Observations
* The diagram highlights that vulnerabilities can arise at each stage of the RAG pipeline.
* The Retriever and Citation stages are each associated with two potential vulnerabilities, while the Knowledge Base and Generator are each associated with one.
* The diagram provides a high-level overview of trust-related issues in RAG systems.
### Interpretation
The diagram illustrates the potential points of failure in a Retrieval-Augmented Generation system that can lead to untrustworthy outputs. It emphasizes that ensuring the reliability of RAG systems requires careful consideration of data quality (Poisoning, Outdated Info, Source Bias), query robustness (Adversarial Queries), and the generation and citation processes (Hallucination, Missing References). The diagram suggests that a holistic approach is needed to address trust vulnerabilities across the entire RAG pipeline.