\n
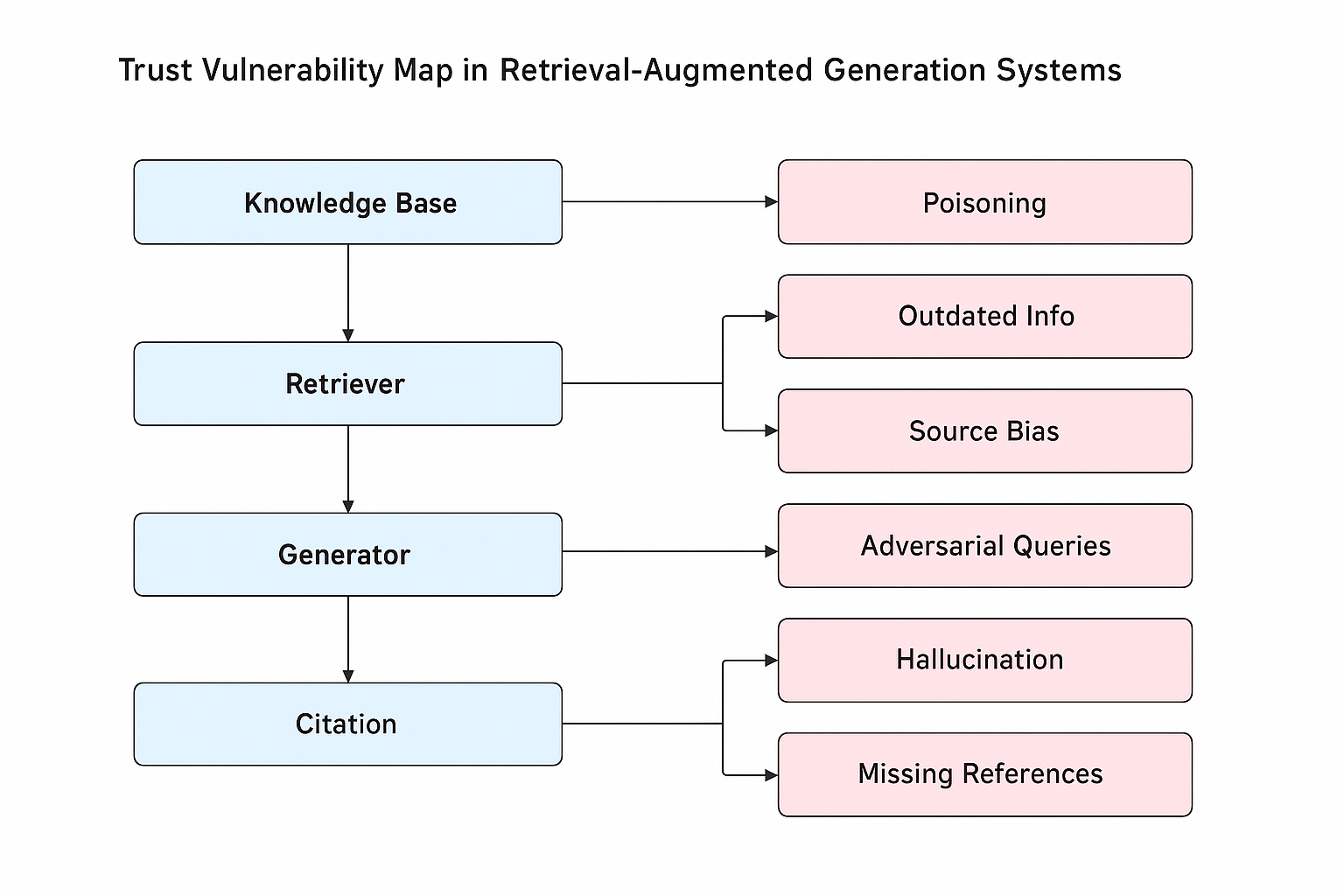
## Diagram: Trust Vulnerability Map in Retrieval-Augmented Generation Systems
### Overview
This image is a flowchart diagram illustrating the components of a Retrieval-Augmented Generation (RAG) system and the specific trust vulnerabilities associated with each component. The diagram is structured in two vertical columns. The left column, in light blue boxes, represents the core system components in a top-down flow. The right column, in light pink boxes, lists the vulnerabilities, with arrows connecting each vulnerability to its associated component(s).
### Components/Axes
**Title:** "Trust Vulnerability Map in Retrieval-Augmented Generation Systems" (centered at the top).
**Left Column (System Components - Light Blue Boxes):**
1. **Knowledge Base** (Top-most box)
2. **Retriever** (Below Knowledge Base)
3. **Generator** (Below Retriever)
4. **Citation** (Bottom-most box)
**Right Column (Vulnerabilities - Light Pink Boxes):**
1. **Poisoning**
2. **Outdated Info**
3. **Source Bias**
4. **Adversarial Queries**
5. **Hallucination**
6. **Missing References**
**Flow and Connections:**
* A vertical arrow points downward from **Knowledge Base** to **Retriever**.
* A vertical arrow points downward from **Retriever** to **Generator**.
* A vertical arrow points downward from **Generator** to **Citation**.
* A horizontal arrow points from **Knowledge Base** to **Poisoning**.
* A branching arrow originates from **Retriever** and splits to point to both **Outdated Info** and **Source Bias**.
* A horizontal arrow points from **Generator** to **Adversarial Queries**.
* A branching arrow originates from **Citation** and splits to point to both **Hallucination** and **Missing References**.
### Detailed Analysis
The diagram explicitly maps vulnerabilities to stages in the RAG pipeline:
* **Knowledge Base Stage:** Vulnerable to **Poisoning**, where malicious or incorrect data is inserted into the foundational data source.
* **Retriever Stage:** Vulnerable to two issues: **Outdated Info** (retrieving stale data) and **Source Bias** (retrieving information from sources with inherent skew).
* **Generator Stage:** Vulnerable to **Adversarial Queries**, where user inputs are crafted to manipulate or trick the generation model.
* **Citation Stage:** Vulnerable to two issues: **Hallucination** (generating citations for non-existent sources) and **Missing References** (failing to cite sources for generated claims).
### Key Observations
1. The diagram presents a clear, linear pipeline (Knowledge Base -> Retriever -> Generator -> Citation) with vulnerabilities branching off at each stage.
2. The **Retriever** and **Citation** components are each associated with two distinct vulnerabilities, suggesting these are particularly complex or failure-prone stages.
3. The vulnerabilities are categorized as external threats (e.g., Poisoning, Adversarial Queries) and internal failures (e.g., Outdated Info, Hallucination, Missing References, Source Bias).
4. The visual design uses color coding (blue for components, pink for vulnerabilities) and directional arrows to create an unambiguous relationship map.
### Interpretation
This diagram serves as a conceptual model for analyzing the trustworthiness of RAG systems. It argues that trust is not a single point of failure but is distributed across the entire pipeline, with each component introducing specific risks.
* **Systemic View:** It emphasizes that ensuring a trustworthy output requires securing every step, from the integrity of the source data (Knowledge Base) to the accuracy of the final attribution (Citation).
* **Attack Surface Mapping:** The right column effectively outlines an "attack surface" for malicious actors or points of degradation for system engineers to monitor. For example, poisoning the knowledge base is a pre-emptive attack, while adversarial queries are an runtime attack.
* **Root Cause Analysis:** The map provides a framework for diagnosing failures. If a system produces hallucinated citations, the diagram directs investigation to the Citation component's processes. If outputs are biased, the Retriever's source selection logic becomes a primary suspect.
* **Design Implication:** The diagram implies that building a robust RAG system requires targeted defenses at each stage: data validation for the Knowledge Base, freshness and de-biasing mechanisms for the Retriever, query sanitization for the Generator, and rigorous fact-checking and source-linking for the Citation module.