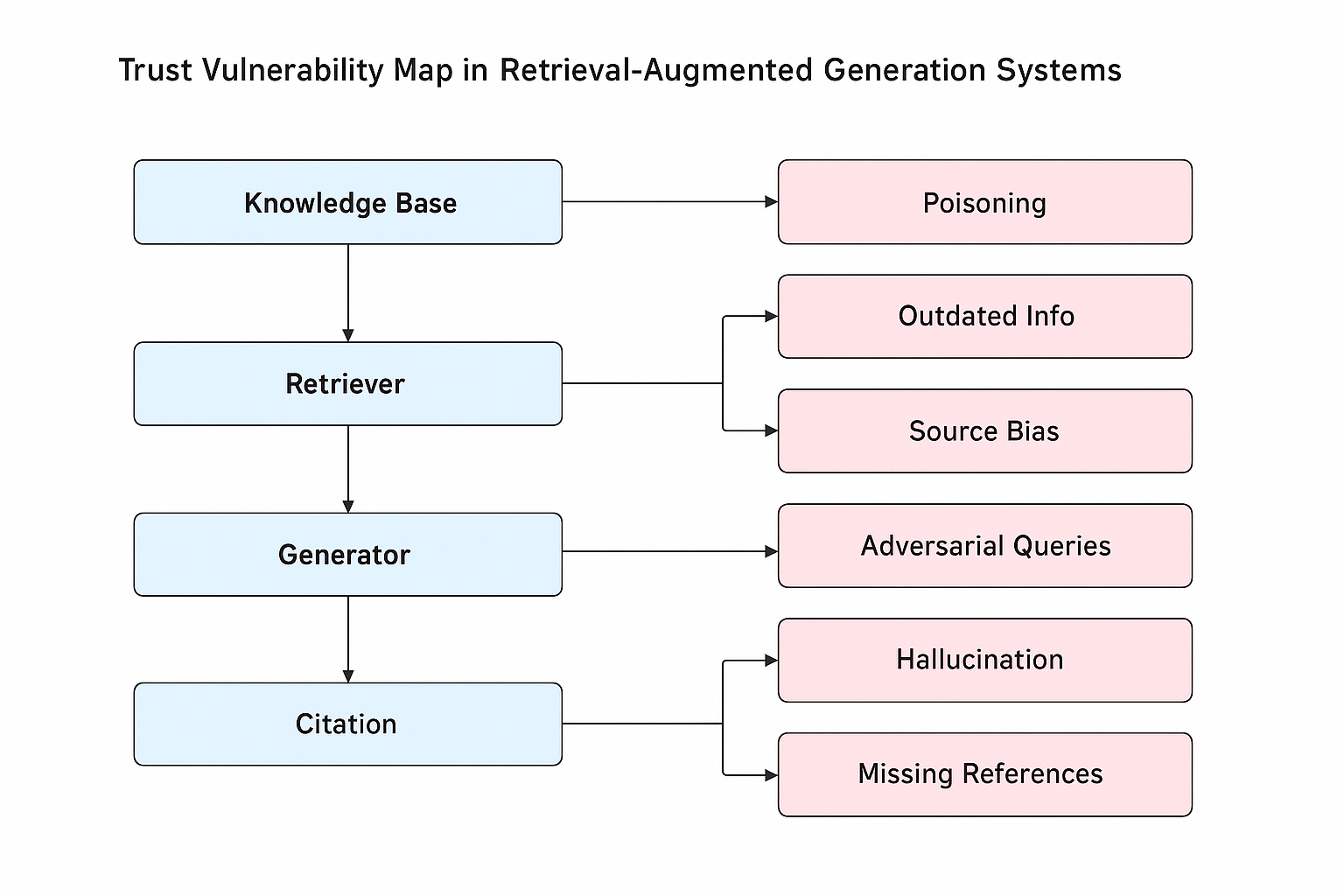
## Flowchart: Trust Vulnerability Map in Retrieval-Augmented Generation Systems
### Overview
The diagram illustrates a trust vulnerability map for retrieval-augmented generation (RAG) systems, showing how vulnerabilities propagate through system components. It uses blue rectangles for system components and pink rectangles for associated vulnerabilities, connected by directional arrows.
### Components/Axes
**System Components (Blue):**
1. **Knowledge Base** (top-left)
2. **Retriever** (center-left)
3. **Generator** (center-right)
4. **Citation** (bottom-center)
**Vulnerabilities (Pink):**
1. **Poisoning** (connected to Knowledge Base)
2. **Outdated Info** (connected to Retriever)
3. **Source Bias** (connected to Retriever)
4. **Adversarial Queries** (connected to Generator)
5. **Hallucination** (connected to Citation)
6. **Missing References** (connected to Citation)
**Flow Direction:**
- Arrows point from system components to their associated vulnerabilities, indicating causal relationships.
### Detailed Analysis
- **Knowledge Base** → **Poisoning**: Direct connection suggests data contamination risks.
- **Retriever** → **Outdated Info** and **Source Bias**: Dual vulnerabilities highlight retrieval-stage trust issues.
- **Generator** → **Adversarial Queries**: Indicates susceptibility to manipulated inputs.
- **Citation** → **Hallucination** and **Missing References**: Dual citation-related trust risks.
### Key Observations
1. **Component-Specific Vulnerabilities**: Each system component has distinct trust risks.
2. **Retriever and Citation Dual Risks**: Both components have two associated vulnerabilities, suggesting higher complexity in trust management.
3. **Unidirectional Flow**: Vulnerabilities only propagate from components to outputs, not vice versa.
### Interpretation
This map reveals systemic trust challenges in RAG architectures:
- **Knowledge Base Poisoning** implies foundational data integrity is critical.
- **Retriever Vulnerabilities** suggest challenges in maintaining up-to-date, unbiased information sources.
- **Generator's Adversarial Query Risk** highlights input validation needs.
- **Citation Issues** (hallucination/missing references) point to post-generation trust verification requirements.
The diagram emphasizes that trust in RAG systems requires safeguards at every stage: data ingestion (Knowledge Base), information retrieval (Retriever), content generation (Generator), and output verification (Citation). The absence of bidirectional arrows suggests vulnerabilities are primarily output-oriented rather than feedback-loop issues.