## Diagram: Agent Communication Network with Proxy
### Overview
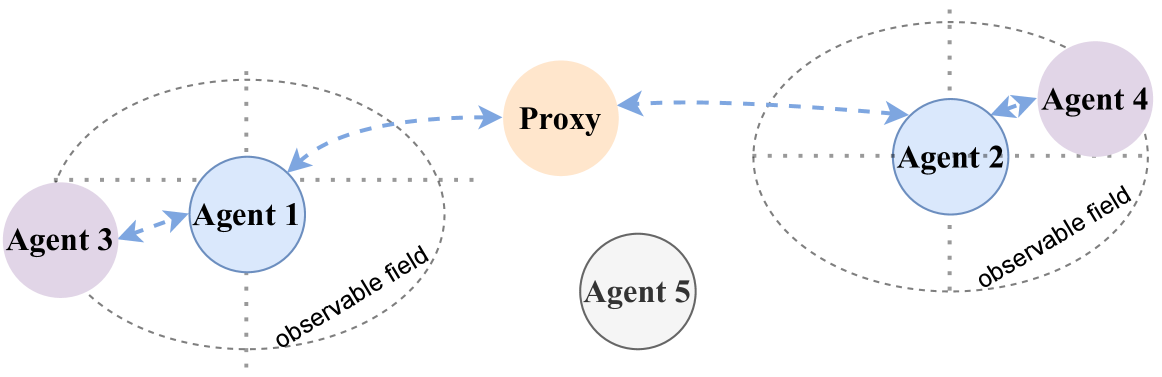
The diagram illustrates a distributed agent communication system divided into two observable fields, connected via a central proxy. Five agents (1-5) and one proxy are depicted, with directional arrows indicating communication flow. Two dashed ovals labeled "observable field" demarcate spatial boundaries for agents 1-3 and agents 2-4, while agent 5 exists outside both fields.
### Components/Axes
- **Agents**:
- Agent 1 (blue circle, left field)
- Agent 2 (blue circle, right field)
- Agent 3 (purple circle, left field)
- Agent 4 (purple circle, right field)
- Agent 5 (gray circle, outside fields)
- **Proxy**: Orange circle between fields
- **Communication Flow**:
- Dashed blue arrows show:
- Agent 3 → Agent 1
- Agent 1 → Proxy
- Proxy → Agent 2
- Agent 2 → Agent 4
- **Spatial Boundaries**:
- Left observable field (agents 1-3)
- Right observable field (agents 2-4)
- Agent 5 positioned centrally between fields
### Detailed Analysis
- **Color Coding**:
- Blue: Primary agents (1, 2)
- Purple: Secondary agents (3, 4)
- Orange: Proxy
- Gray: Isolated agent (5)
- **Communication Path**:
- Left field agents (3→1) communicate internally, then route through proxy to right field (1→Proxy→2→4)
- No direct communication between fields without proxy
- **Agent 5**:
- Positioned outside both observable fields
- No incoming/outgoing arrows
- Gray color suggests non-participation in current network
### Key Observations
1. **Proxy as Mediator**: All inter-field communication requires proxy involvement
2. **Field Isolation**: Observable fields maintain strict boundaries (no direct agent-to-agent cross-field communication)
3. **Agent 5's Role**: Exists outside the network, potentially representing an external entity or unconnected system component
4. **Hierarchical Structure**:
- Left field: Agent 3 → Agent 1 (potential command flow)
- Right field: Agent 2 → Agent 4 (potential command flow)
### Interpretation
This architecture suggests a security-conscious system design where:
- The proxy acts as a controlled gateway between separate operational domains
- Agent 3 and 4 may represent peripheral systems requiring restricted access
- Agent 5's isolation could indicate:
- A monitoring system
- An external threat actor
- A future expansion point
- The two-tier communication flow (internal → proxy → external) implies:
- Data sanitization/validation at proxy
- Potential latency introduction
- Single point of failure risk
The diagram emphasizes controlled information flow between segregated systems, with the proxy serving as both connector and potential bottleneck. Agent 5's positioning raises questions about its relationship to the network - whether it's intentionally excluded or represents an unknown variable in the system.