\n
## Diagram: Execution Flow with QEMU and Real Device
### Overview
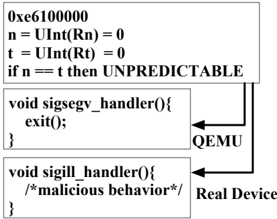
The image presents a diagram illustrating the execution flow of code snippets under two different environments: QEMU and a Real Device. It highlights how signal handlers are invoked and the resulting behavior in each environment. The diagram consists of three code blocks and arrows indicating the flow of execution.
### Components/Axes
The diagram contains the following components:
* **Code Block 1 (Top):** Contains assembly-like code with initializations and a conditional statement.
* **Code Block 2 (Middle):** Contains a C function definition for a `sigsegv_handler` which calls `exit(0)`.
* **Code Block 3 (Bottom):** Contains a C function definition for a `sigill_handler` with a comment indicating "malicious behavior".
* **QEMU Label:** Located to the right of Code Block 2, indicating the execution environment.
* **Real Device Label:** Located to the right of Code Block 3, indicating the execution environment.
* **Arrows:** Indicate the flow of execution from Code Block 1 to Code Block 2 (QEMU) and Code Block 1 to Code Block 3 (Real Device).
### Detailed Analysis or Content Details
**Code Block 1:**
* `0xe6100000`: This appears to be a memory address.
* `n = UInt(Rn) = 0`: Initializes a variable `n` to 0, where `Rn` is likely a register. `UInt` suggests an unsigned integer type.
* `t = UInt(Rt) = 0`: Initializes a variable `t` to 0, where `Rt` is likely a register. `UInt` suggests an unsigned integer type.
* `if n == t then UNPREDICTABLE`: A conditional statement. If `n` is equal to `t`, the behavior is labeled as "UNPREDICTABLE".
**Code Block 2:**
* `void sigsegv_handler(){ exit(0); }`: Defines a signal handler function named `sigsegv_handler`. When this handler is invoked (likely due to a segmentation fault), it calls the `exit(0)` function, terminating the program.
**Code Block 3:**
* `void sigill_handler(){ /* malicious behavior */ }`: Defines a signal handler function named `sigill_handler`. The comment indicates that this handler is associated with "malicious behavior".
**Execution Flow:**
* An arrow originates from Code Block 1 and points to Code Block 2, labeled "QEMU". This suggests that under QEMU, the condition in Code Block 1 triggers the `sigsegv_handler`.
* An arrow originates from Code Block 1 and points to Code Block 3, labeled "Real Device". This suggests that on a Real Device, the condition in Code Block 1 triggers the `sigill_handler`.
### Key Observations
* The diagram highlights a divergence in execution paths based on the environment (QEMU vs. Real Device).
* QEMU appears to handle the condition in Code Block 1 by invoking a segmentation fault handler (`sigsegv_handler`), leading to program termination.
* The Real Device appears to handle the same condition by invoking an illegal instruction handler (`sigill_handler`), which is associated with malicious behavior.
* The "UNPREDICTABLE" label suggests that the outcome of the condition in Code Block 1 is not deterministic.
### Interpretation
The diagram illustrates a potential vulnerability exploitation scenario. The initial code block sets up a condition that, when met, triggers different signal handlers depending on whether the code is running in QEMU or on a real device. This difference in behavior is exploited.
In QEMU, a segmentation fault is triggered, which is handled by the `sigsegv_handler`, resulting in a clean exit. This is a safe and expected outcome.
However, on a real device, the same condition triggers an illegal instruction signal, handled by the `sigill_handler`. The comment "malicious behavior" indicates that this handler is designed to execute harmful code. This suggests that the code is designed to behave benignly in a controlled environment (QEMU) for analysis, but to execute malicious code on a real device.
The use of `UInt(Rn)` and `UInt(Rt)` suggests that the condition `n == t` is likely related to register values. The "UNPREDICTABLE" label implies that the values of these registers are not easily predictable, potentially making it difficult to debug or analyze the code's behavior.
This diagram demonstrates a technique for creating malware that is difficult to detect during analysis, as it exhibits different behavior in different environments. The QEMU environment provides a safe sandbox for analysis, while the real device environment reveals the malicious intent.