## Flowchart: Secure AI Model Evaluation and Verification Process
### Overview
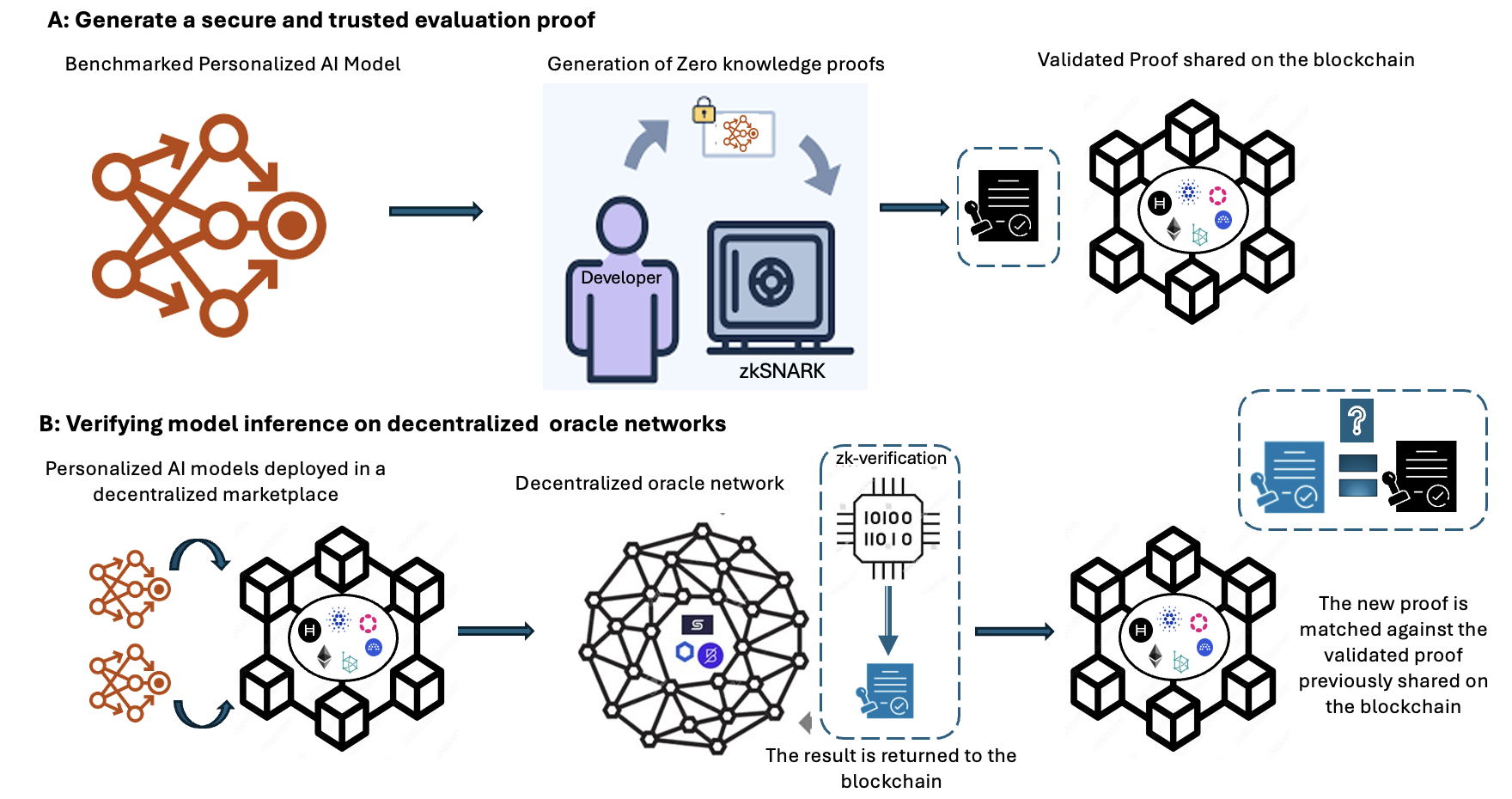
The diagram illustrates a two-phase process for generating and verifying secure, trustworthy AI model evaluations using zero-knowledge proofs (zk-proofs) and blockchain technology. It emphasizes decentralization, cryptographic verification, and trustless validation.
### Components/Axes
1. **Section A: Generate a Secure and Trusted Evaluation Proof**
- **Components**:
- **Benchmarked Personalized AI Model**: Represented by interconnected nodes with directional arrows (orange).
- **Developer**: A human figure interacting with a locked "zkSNARK" box (blue).
- **zkSNARK**: A cryptographic proof system (blue box with a lock icon).
- **Validated Proof Shared on the Blockchain**: A hexagonal blockchain structure with symbols (H, Ethereum, etc.) and cubes.
- **Flow**:
- AI model → Generation of zk-proofs (locked box) → Validation → Blockchain storage.
2. **Section B: Verifying Model Inference on Decentralized Oracle Networks**
- **Components**:
- **Personalized AI Models in a Decentralized Marketplace**: Two orange AI models feeding into a hexagonal oracle network.
- **Decentralized Oracle Network**: A dense hexagonal network with embedded symbols (H, Ethereum, etc.).
- **zk-Verification**: A CPU-like component with binary code (10100, 11010) and a validation stamp.
- **Blockchain Matching**: A hexagonal blockchain with cubes and a comparison of new vs. validated proofs.
- **Flow**:
- Marketplace models → Oracle network → zk-verification → Blockchain storage and validation.
### Detailed Analysis
- **Section A**:
- The AI model generates zk-proofs via zkSNARK, ensuring privacy and correctness without revealing internal logic.
- The developer interacts with the zkSNARK system, which produces a proof validated and stored on the blockchain.
- Blockchain symbols (H, Ethereum) suggest multi-chain compatibility or interoperability.
- **Section B**:
- AI models deployed in a decentralized marketplace feed into an oracle network for inference.
- The oracle network uses zk-verification (CPU-like component) to validate results cryptographically.
- Validated proofs are matched against prior blockchain entries to ensure consistency and prevent tampering.
### Key Observations
1. **Cryptographic Trust**: zkSNARK and zk-verification ensure proofs are generated and validated without exposing sensitive data.
2. **Decentralization**: Both sections emphasize decentralized systems (oracle networks, blockchain) to avoid single points of failure.
3. **Blockchain as a Ledger**: The hexagonal blockchain structure acts as an immutable record for proofs, with cubes symbolizing data blocks.
4. **Symbolic Representation**:
- **H**: Likely represents Horizen (a blockchain platform).
- **Ethereum**: Indicates compatibility with Ethereum-based systems.
- **Other Symbols**: May denote additional blockchains or cryptographic protocols.
### Interpretation
The diagram outlines a framework for secure AI model evaluation in decentralized environments. By leveraging zk-proofs, the system ensures that AI inferences are both private and verifiable. The blockchain serves as a tamper-proof ledger to store and validate proofs, while decentralized oracle networks enable trustless coordination between AI models and external data sources.
The use of zkSNARK in Section A highlights a focus on privacy-preserving AI, while Section B’s oracle network and zk-verification emphasize scalability and decentralization. The matching of new proofs against prior blockchain entries ensures accountability, preventing malicious actors from submitting invalid results.
This architecture could be critical for applications requiring auditable, secure AI decisions (e.g., finance, healthcare) where trust and transparency are paramount.