## System Diagram: Trusted Execution Environment (TEE) Build Process
### Overview
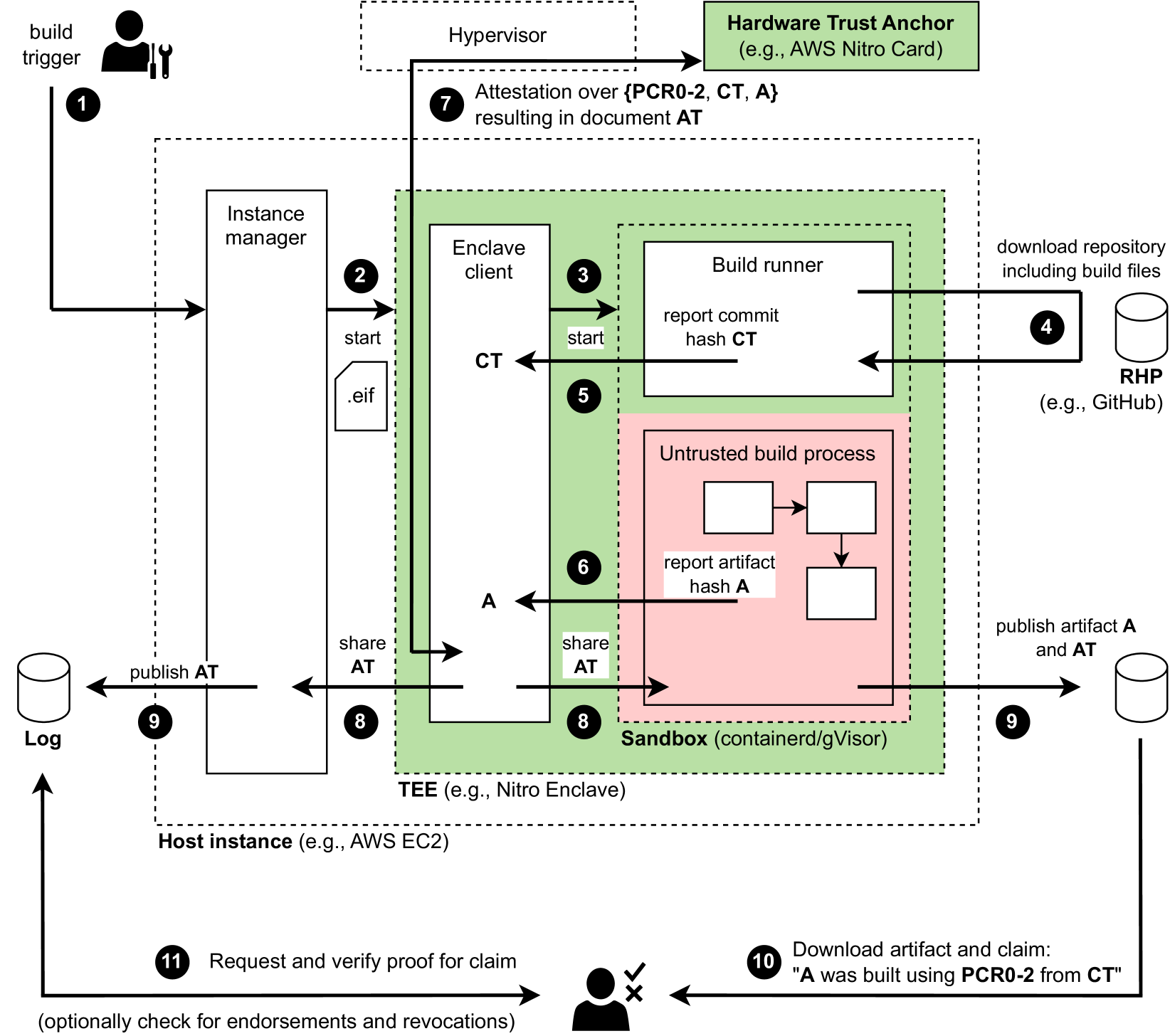
The image is a system diagram illustrating a trusted build process within a Trusted Execution Environment (TEE), specifically using technologies like AWS Nitro Enclave. It outlines the steps involved in building and verifying an artifact using hardware-based attestation.
### Components/Axes
The diagram includes the following components:
1. **Build Trigger:** Initiates the build process.
2. **Instance Manager:** Manages the host instance.
3. **Enclave Client:** A client within the TEE.
4. **Build Runner:** Executes the build process.
5. **Untrusted Build Process:** The actual build steps, isolated within a sandbox.
6. **Hardware Trust Anchor:** Provides hardware-based attestation (e.g., AWS Nitro Card).
7. **Log:** Stores the published attestation.
8. **RHP (Repository Hosting Provider):** Stores the source code (e.g., GitHub).
9. **Hypervisor:** Manages the virtual machine.
10. **TEE (Trusted Execution Environment):** (e.g., Nitro Enclave)
11. **Host Instance:** (e.g., AWS EC2)
12. **Sandbox:** (containerd/gVisor)
The diagram also includes labels for data and control flow, such as "start," ".eif," "report commit hash CT," "report artifact hash A," "share AT," and "publish AT."
### Detailed Analysis or Content Details
The process flow is as follows:
1. **Build Trigger (1):** The process starts with a build trigger.
2. **Instance Manager (2):** The instance manager starts the enclave client with a `.eif` file.
3. **Enclave Client (3):** The enclave client starts the build runner.
4. **RHP (4):** The build runner downloads the repository including build files from a repository hosting provider (e.g., GitHub).
5. **Build Runner (5):** The build runner reports the commit hash (CT) to the enclave client.
6. **Untrusted Build Process (6):** The untrusted build process reports the artifact hash (A) to the sandbox.
7. **Attestation (7):** Attestation over {PCR0-2, CT, A} resulting in document AT.
8. **Sharing Attestation (8):** The enclave client and sandbox share the attestation (AT).
9. **Publishing (9):** The artifact (A) and attestation (AT) are published to a log.
10. **Download and Claim (10):** A user downloads the artifact and claim: "A was built using PCR0-2 from CT".
11. **Request and Verify (11):** The user requests and verifies the proof for the claim, optionally checking for endorsements and revocations.
### Key Observations
* The diagram highlights the isolation of the untrusted build process within a sandbox inside a TEE.
* Hardware-based attestation is used to verify the integrity of the build process and the resulting artifact.
* The process involves multiple components, including the instance manager, enclave client, build runner, and hardware trust anchor.
### Interpretation
The diagram illustrates a secure build process that leverages a Trusted Execution Environment (TEE) and hardware-based attestation to ensure the integrity and trustworthiness of the built artifact. The TEE isolates the build process from the host environment, while attestation provides a verifiable record of the build process and the artifact's provenance. This approach is valuable for building and distributing software in environments where trust is critical, such as cloud computing and embedded systems. The process ensures that the artifact can be verified to have been built using a specific code commit and within a trusted environment, mitigating the risk of supply chain attacks and other security threats.