## Diagram: Secure Build Process Flow
### Overview
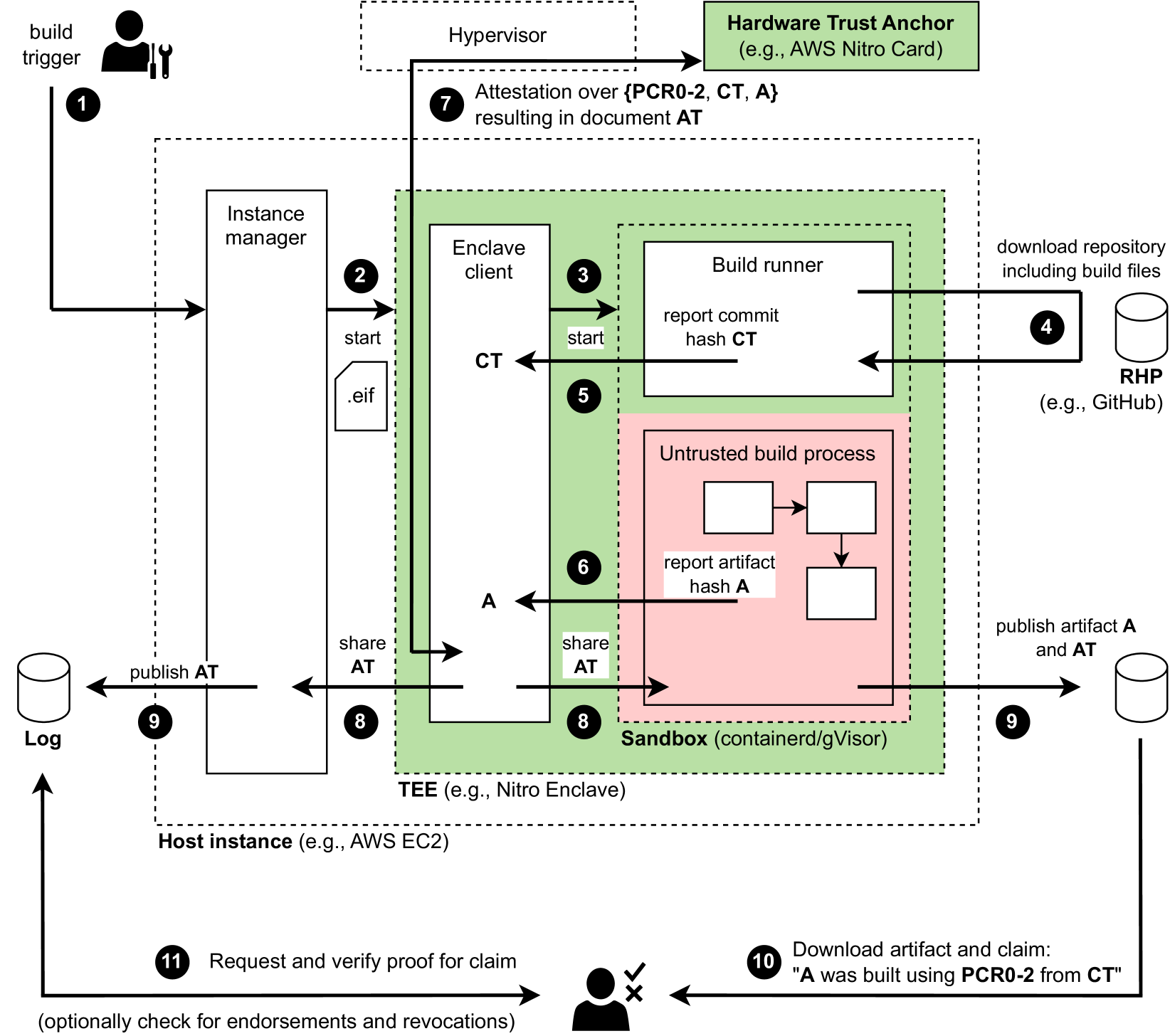
This diagram illustrates a secure build process utilizing a Trusted Execution Environment (TEE) to ensure the integrity and provenance of software artifacts. The process begins with a build trigger and culminates in the verification of the built artifact. The diagram highlights the interaction between various components, including a Hardware Trust Anchor, Hypervisor, Instance Manager, Enclave Client, Build Runner, Sandbox, and external repositories.
### Components/Axes
The diagram consists of several key components:
* **Hardware Trust Anchor:** (e.g., AWS Nitro Card) - Provides a root of trust.
* **Hypervisor:** Responsible for attestation.
* **Host Instance:** (e.g., AWS EC2) - The underlying infrastructure.
* **Instance Manager:** Manages instances within the host.
* **Enclave Client:** Initiates and manages the secure build process within the TEE.
* **Build Runner:** Executes the build process.
* **Untrusted Build Process:** The actual build steps.
* **Sandbox:** (containerd/gVisor) - Isolates the build process.
* **RHP (Repository Host Provider):** (e.g., GitHub) - Source code repository.
* **Log:** Stores build-related information.
* **TEE (Trusted Execution Environment):** (e.g., Nitro Enclave) - Provides a secure environment for the build process.
The diagram uses numbered arrows to indicate the flow of control and data. Key data elements include:
* **CT:** Commit Hash
* **A:** Artifact Hash
* **AT:** Attestation Document
### Detailed Analysis / Content Details
1. **Build Trigger:** Initiates the build process.
2. **Instance Manager to Enclave Client:** The Instance Manager starts the Enclave Client, passing an `.eif` file.
3. **Enclave Client to Build Runner:** The Enclave Client starts the Build Runner.
4. **Build Runner to RHP:** The Build Runner downloads the repository, including build files, from the RHP (e.g., GitHub).
5. **Build Runner to Enclave Client:** The Build Runner reports the commit hash (CT) to the Enclave Client.
6. **Untrusted Build Process to Sandbox:** The untrusted build process executes within the Sandbox.
7. **Hypervisor Attestation:** The Hypervisor performs attestation over (PCR0-2, CT, A) resulting in the Attestation Document (AT).
8. **Sandbox to Enclave Client:** The Sandbox shares the Attestation Document (AT) with the Enclave Client.
9. **Publishing AT and Artifact:** The Attestation Document (AT) and the artifact (A) are published to a Log.
10. **Download and Claim Verification:** An external entity downloads the artifact and claims "A was built using PCR0-2 from CT". This is represented with a checkmark and an X, indicating successful and failed verification respectively.
11. **Request and Verify Proof:** A request is made to verify the proof of claim, optionally checking for endorsements and revocations.
The arrows indicate the following flow:
* A solid arrow indicates a direct flow of control or data.
* A dashed arrow indicates an attestation or verification process.
### Key Observations
* The process emphasizes attestation as a critical security measure. The Hypervisor attests to the integrity of the build environment.
* The use of a TEE (Nitro Enclave) provides a secure environment for the build process, isolating it from the potentially compromised Host Instance.
* The diagram highlights the importance of hashing (CT and A) for verifying the integrity of the source code and the resulting artifact.
* The process includes a mechanism for publishing and verifying the Attestation Document (AT), providing transparency and accountability.
* The diagram shows a clear separation between the trusted and untrusted components of the build process.
### Interpretation
This diagram demonstrates a secure software build pipeline designed to mitigate supply chain attacks. By leveraging a Hardware Trust Anchor, TEE, and attestation mechanisms, the process aims to establish a strong chain of trust from the source code to the final artifact. The attestation process ensures that the build environment is in a known and trusted state, and the hashing of the source code and artifact provides a means to verify their integrity. The publishing of the Attestation Document allows external parties to independently verify the provenance of the artifact.
The inclusion of PCR0-2 in the attestation process suggests that the integrity of the boot process and the initial system configuration are also considered part of the trust establishment. The optional check for endorsements and revocations indicates a potential mechanism for managing trust relationships and responding to security vulnerabilities.
The diagram suggests a robust and comprehensive approach to secure software builds, addressing key concerns related to integrity, provenance, and transparency. The use of specific technologies like AWS Nitro Card and Nitro Enclave indicates a cloud-native security model.