## Flowchart: Secure Build Process with Attestation
### Overview
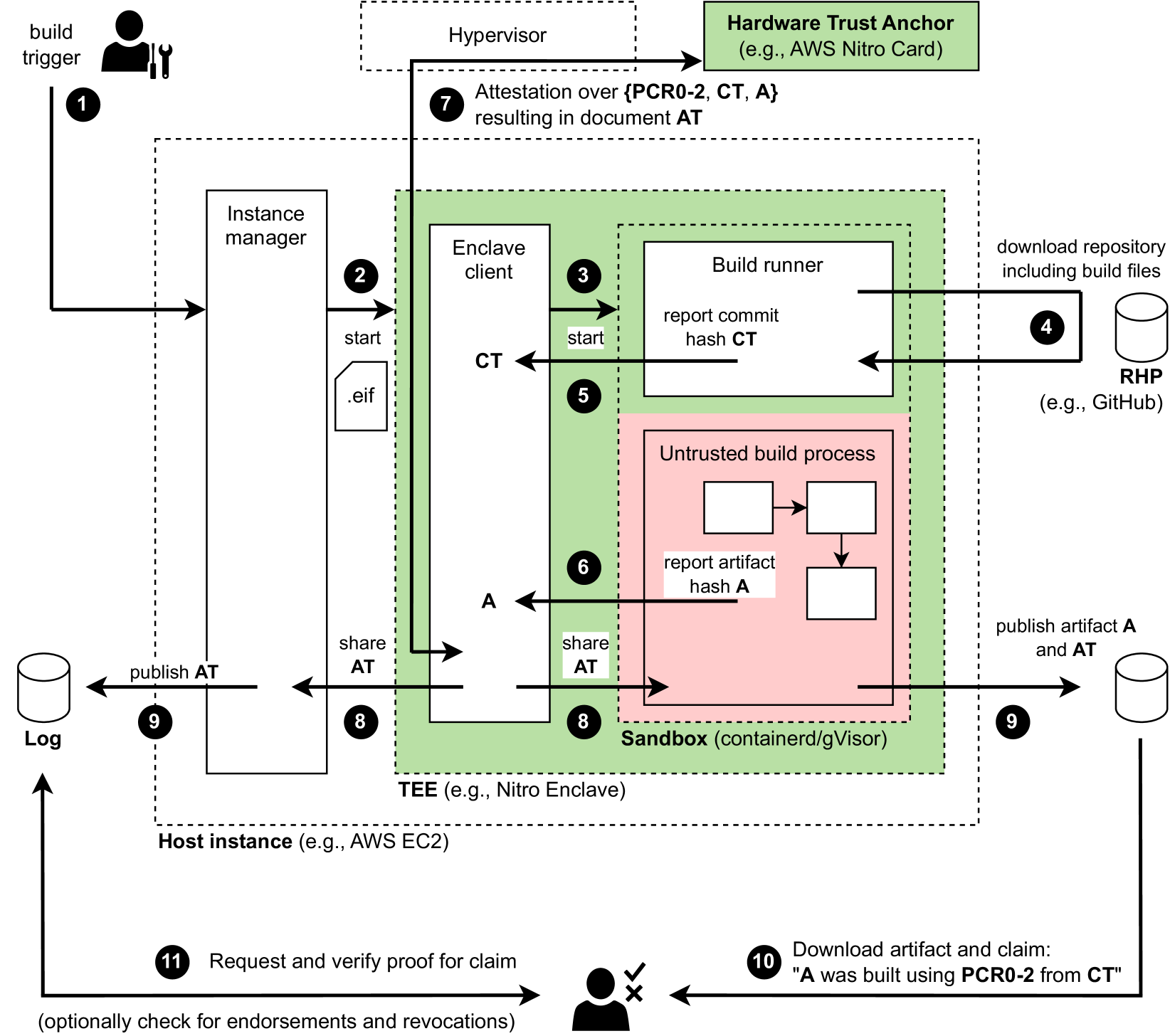
This flowchart illustrates a secure build process involving hardware-based attestation, enclave computing, and artifact verification. It outlines steps from code commit to final artifact validation, emphasizing trust anchors, secure execution environments, and cryptographic verification.
### Components/Axes
1. **Key Components**:
- **Build Trigger**: Initiates the process (Step 1)
- **Hypervisor**: Manages virtualization (Step 2)
- **Hardware Trust Anchor**: Includes PCR0-2, CT, A (Step 7)
- **Instance Manager**: Coordinates build instances (Step 2)
- **Enclave Client**: Manages secure enclave operations (Step 3)
- **Build Runner**: Executes build process (Step 4)
- **Untrusted Build Process**: Non-secure build components (Step 6)
- **Sandbox**: Isolated execution environment (Step 8)
- **TEE (Trusted Execution Environment)**: e.g., Nitro Enclave (Step 8)
- **Host Instance**: Physical/cloud infrastructure (Step 8)
- **Log**: Central repository for attestation documents (Step 9)
- **RHP (Repository Hosting Platform)**: e.g., GitHub (Step 4)
- **User Interaction**: Final verification step (Step 11)
2. **Flow Direction**:
- Left-to-right progression from code commit to artifact validation
- Vertical connections between components (e.g., build runner → sandbox)
- Feedback loops for attestation and verification
### Detailed Analysis
1. **Build Process Flow**:
- **Step 1-3**: Code commit (CT) triggers build instance creation
- **Step 4-5**: Build runner executes in sandbox, reporting commit hash
- **Step 6-7**: Untrusted build process generates artifact hash (A)
- **Step 8**: TEE sandbox executes in host instance (AWS EC2)
- **Step 9**: Attestation document (AT) published to log
- **Step 10-11**: Artifact and AT published to RHP
- **Step 12**: User verifies claim: "A was built using PCR0-2 from CT"
2. **Security Mechanisms**:
- Hardware Trust Anchor (green box) anchors PCR measurements
- Enclave client (Step 3) manages secure enclave operations
- Sandbox (Step 8) isolates untrusted build process
- TEE (Step 8) provides memory encryption and integrity
3. **Artifact Verification**:
- Commit hash (CT) and artifact hash (A) cryptographically linked
- Attestation document (AT) combines PCR0-2, CT, and A
- Final verification checks PCR0-2 against CT
### Key Observations
1. **Trust Chain**:
- Hardware Trust Anchor (Step 7) provides root of trust
- PCR0-2 measurements anchor build environment state
- CT (commit hash) anchors source code integrity
2. **Isolation Layers**:
- Sandbox (Step 8) isolates untrusted build process
- TEE (Step 8) provides additional memory protection
- Enclave client (Step 3) manages secure communication
3. **Verification Flow**:
- Attestation document (Step 9) combines multiple trust elements
- Final verification (Step 12) checks cryptographic proof
- Optional endorsement/revocation checks (Step 11)
### Interpretation
This diagram demonstrates a multi-layered security approach for build artifact verification:
1. **Hardware Root of Trust**: PCR0-2 measurements from the Hardware Trust Anchor (e.g., AWS Nitro Card) provide foundational trust.
2. **Secure Execution**: The build process occurs in isolated environments (sandbox/TEE) to prevent tampering.
3. **Cryptographic Verification**: The attestation document (AT) combines hardware measurements, commit hashes, and artifact hashes for end-to-end verification.
4. **User Validation**: Final step allows users to verify claims about build provenance, ensuring artifacts were built using specific hardware configurations.
The process emphasizes defense-in-depth security, combining hardware isolation, cryptographic attestation, and secure execution environments to prevent supply chain attacks and ensure build integrity.