\n
## Diagram: Secret Sharing Scheme using DFT/IDFT
### Overview
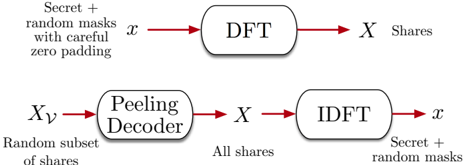
The image depicts a diagram illustrating a secret sharing scheme based on the Discrete Fourier Transform (DFT) and its inverse, the Inverse Discrete Fourier Transform (IDFT). The diagram shows the process of encoding a secret into shares and then reconstructing the secret from those shares. It consists of two main flows: encoding (top) and decoding (bottom).
### Components/Axes
The diagram contains the following components:
* **Input:** `x` - Represents the secret plus random masks with careful zero padding.
* **DFT Block:** A rectangular block labeled "DFT".
* **Output (Encoding):** `X` - Represents the shares.
* **Input (Decoding):** `X_y` - Represents a random subset of shares.
* **Peeling Decoder Block:** A rectangular block labeled "Peeling Decoder".
* **IDFT Block:** A rectangular block labeled "IDFT".
* **Output (Decoding):** `x` - Represents the reconstructed secret plus random masks.
* **Text Labels:** Descriptive text accompanying each component, explaining the input and output.
### Detailed Analysis or Content Details
The diagram shows a two-step process:
**Encoding (Top Row):**
1. The secret `x` (along with random masks and zero padding) is input into the DFT block.
2. The DFT block transforms `x` into `X`, which represents the shares. An arrow indicates the flow from `x` to DFT, and from DFT to `X`.
**Decoding (Bottom Row):**
1. A random subset of shares `X_y` is input into the Peeling Decoder block.
2. The Peeling Decoder block processes `X_y` to produce `X` (all shares). An arrow indicates the flow from `X_y` to Peeling Decoder, and from Peeling Decoder to `X`.
3. `X` is then input into the IDFT block.
4. The IDFT block transforms `X` back into `x`, reconstructing the original secret plus the random masks. An arrow indicates the flow from `X` to IDFT, and from IDFT to `x`.
The text labels provide additional context:
* "Secret + random masks with careful zero padding" describes the input `x`.
* "Shares" describes the output `X`.
* "Random subset of shares" describes the input `X_y`.
* "All shares" describes the output of the Peeling Decoder.
* "Secret + random masks" describes the output `x`.
### Key Observations
The diagram illustrates a method for distributing a secret among multiple parties (shares) such that the secret can only be reconstructed if a sufficient number of shares are combined. The use of DFT and IDFT suggests a frequency-domain approach to secret sharing. The "Peeling Decoder" is a key component in reconstructing the full set of shares from a subset.
### Interpretation
This diagram represents a cryptographic technique for secure secret sharing. The DFT and IDFT are used to transform the secret into a different domain (frequency domain) where it can be split into shares. The Peeling Decoder is a crucial step in recovering the complete set of shares from a random subset. This scheme leverages the properties of the DFT to ensure that the secret remains hidden unless a sufficient number of shares are available. The addition of random masks and zero padding likely enhances the security of the scheme by obscuring the original secret and preventing attacks based on known plaintext. The diagram demonstrates a mathematical approach to information security, relying on the properties of signal processing to achieve confidentiality. The diagram does not provide any specific numerical data or parameters, but rather illustrates the conceptual flow of the secret sharing process.