## Diagram: Two-Stage Signal Processing Flowchart
### Overview
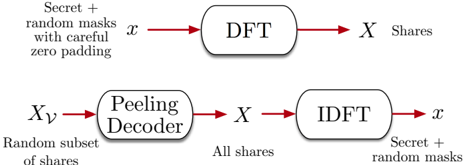
The image displays a two-part technical flowchart illustrating a signal processing or cryptographic scheme. The diagram is divided into two horizontal sections, each representing a distinct process flow. The top section depicts an **encoding or sharing process**, while the bottom section depicts a corresponding **decoding or reconstruction process**. The flows are connected by shared variables and mathematical operations.
### Components/Axes
The diagram contains no traditional chart axes. It is composed of the following textual and graphical components:
**Top Process (Encoding/Sharing):**
1. **Input Label (Left):** "Secret + random masks with careful zero padding"
2. **Input Variable:** `x` (placed above the arrow leading from the input label to the first block).
3. **Processing Block:** A rounded rectangle labeled "DFT" (likely Discrete Fourier Transform).
4. **Output Variable:** `X` (placed above the arrow leading from the DFT block to the output label).
5. **Output Label (Right):** "Shares"
**Bottom Process (Decoding/Reconstruction):**
1. **Input Label (Left):** "Random subset of shares"
2. **Input Variable:** `Xν` (Greek letter nu, placed above the arrow leading from the input label to the first block).
3. **Processing Block 1:** A rounded rectangle labeled "Peeling Decoder".
4. **Intermediate Variable:** `X` (placed above the arrow leading from the Peeling Decoder to the next label).
5. **Intermediate Label:** "All shares"
6. **Processing Block 2:** A rounded rectangle labeled "IDFT" (likely Inverse Discrete Fourier Transform).
7. **Output Variable:** `x` (placed above the arrow leading from the IDFT block to the final label).
8. **Output Label (Right):** "Secret + random masks"
**Visual Structure:**
* The two processes are arranged vertically, with the encoding process on top and the decoding process on the bottom.
* Each process flows unidirectionally from left to right, indicated by red arrows.
* The variables `x` and `X` act as the primary links between the two processes, appearing in both.
### Detailed Analysis
**Process Flow & Variable Mapping:**
1. **Top Flow (Encoding):**
* **Start:** A composite signal consisting of a "Secret" combined with "random masks" and prepared with "careful zero padding". This is represented by the variable `x`.
* **Operation:** The signal `x` undergoes a Discrete Fourier Transform (DFT).
* **End:** The output is a set of "Shares", represented by the variable `X` (the frequency-domain representation of `x`).
2. **Bottom Flow (Decoding):**
* **Start:** A "Random subset of shares" is available, represented by the variable `Xν`. The subscript `ν` (nu) likely denotes a subset or index.
* **Operation 1:** This subset `Xν` is processed by a "Peeling Decoder". The output of this decoder is the complete set of "All shares", represented by the variable `X`.
* **Operation 2:** The complete shares `X` undergo an Inverse Discrete Fourier Transform (IDFT).
* **End:** The output is the original composite signal: "Secret + random masks", represented by the variable `x`.
**Key Relationships:**
* The variable `X` (frequency-domain shares) is the output of the top process and the required input for the final step of the bottom process.
* The variable `x` (time/spatial-domain secret+masks) is the input to the top process and the final output of the bottom process.
* The "Peeling Decoder" is the critical component that enables the reconstruction of the full share set `X` from only a random subset `Xν`.
### Key Observations
* **Symmetry and Inversion:** The diagram shows a clear symmetric relationship. The top process transforms `x` to `X` via DFT. The bottom process inverts this, transforming `X` back to `x` via IDFT, but only after the missing shares are recovered.
* **Core Challenge Addressed:** The system is designed to handle incomplete data. The starting point of the bottom process is a "Random subset," implying the system is robust to data loss or is designed for scenarios where only partial information is initially available.
* **Mathematical Foundation:** The use of DFT/IDFT places this scheme firmly in the domain of signal processing, coding theory, or cryptography that leverages frequency-domain techniques (e.g., certain secret sharing schemes, error-correcting codes, or secure multi-party computation protocols).
* **"Peeling" Mechanism:** The term "Peeling Decoder" suggests an iterative or sequential algorithm that "peels away" layers of information or interference to recover the full signal, a concept common in modern coding theory (e.g., LDPC codes).
### Interpretation
This diagram illustrates a **robust secret sharing or data recovery scheme based on the Discrete Fourier Transform**.
The core idea is to encode a secret (protected by random masks and zero-padding) into a set of frequency-domain "shares" (`X`). The security or robustness property is that the original secret can be recovered even if only a random subset of these shares (`Xν`) is available. The "Peeling Decoder" is the key algorithmic innovation that reconstructs the complete set of shares from the partial set. Once the full share set `X` is recovered, the original secret+masks (`x`) is easily obtained via the inverse transform (IDFT).
This has applications in:
1. **Secure Distributed Storage:** The secret can be split and stored across multiple servers. The data remains recoverable even if some servers (shares) are offline or compromised.
2. **Secure Multi-Party Computation:** Parties can hold shares of a secret and collaboratively compute functions on it without any single party knowing the full secret.
3. **Error Correction:** The scheme can be viewed as an error-correcting code where the "errors" are missing shares, and the peeling decoder corrects them.
The "careful zero padding" is a crucial technical detail, likely ensuring the DFT operates correctly on the signal length and possibly contributing to the security or recoverability properties of the scheme. The use of "random masks" is a standard technique to ensure the shares themselves reveal no information about the underlying secret.