## Diagram: Secure Data Transformation Process
### Overview
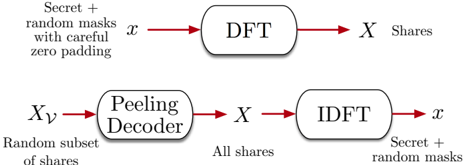
The diagram illustrates a two-stage process for transforming a secret signal `x` into encrypted shares and reconstructing it. It involves Discrete Fourier Transform (DFT), Inverse Discrete Fourier Transform (IDFT), and a Peeling Decoder, with explicit handling of random masks and zero padding for security.
### Components/Axes
1. **Top Process (Encoding):**
- **Input:** `x` (Secret + random masks with careful zero padding)
- **Component:** DFT (Discrete Fourier Transform)
- **Output:** `X` (Shares)
- **Key Labels:** "Secret + random masks with careful zero padding", "DFT", "X Shares"
2. **Bottom Process (Decoding):**
- **Input:** `Xᵥ` (Random subset of shares)
- **Component:** Peeling Decoder
- **Intermediate Output:** `X` (All shares)
- **Component:** IDFT (Inverse Discrete Fourier Transform)
- **Output:** `x` (Secret + random masks)
- **Key Labels:** "Random subset of shares", "Peeling Decoder", "All shares", "IDFT", "Secret + random masks"
3. **Flow Arrows:**
- Red arrows indicate data flow direction.
- Labels on arrows: "Secret + random masks with careful zero padding", "X Shares", "Random subset of shares", "All shares", "Secret + random masks".
### Detailed Analysis
- **Encoding Stage:**
- The secret signal `x` is preprocessed with **random masks** and **zero padding** to enhance security before undergoing DFT.
- DFT converts the time-domain signal `x` into frequency-domain shares `X`, enabling distributed or encrypted storage/transmission.
- **Decoding Stage:**
- A **random subset of shares** (`Xᵥ`) is input to the Peeling Decoder, which reconstructs the full set of shares `X`.
- IDFT then converts the shares back to the original signal `x`, retaining the random masks for security.
### Key Observations
1. **Security Mechanism:** Random masks and zero padding are explicitly used to obscure the original signal, preventing direct inference of `x` from partial shares.
2. **Reversibility:** The process is designed to be lossless, as the original signal `x` is perfectly reconstructed after decoding.
3. **Subset Utilization:** The Peeling Decoder operates on a random subset of shares (`Xᵥ`), suggesting resilience to partial data loss or selective sharing.
### Interpretation
This diagram represents a **secure signal sharing/encryption framework** leveraging Fourier transforms and combinatorial decoding. The use of random masks and zero padding aligns with techniques in **homomorphic encryption** or **secure multi-party computation**, where data is transformed into shares that can be combined without exposing the original secret. The Peeling Decoder’s role in reconstructing all shares from a subset implies a **robust error-correction or redundancy mechanism**, critical for fault-tolerant systems. The bidirectional flow between DFT/IDFT and the Peeling Decoder highlights a **two-way relationship** between frequency-domain shares and time-domain signals, emphasizing the importance of precise mathematical transformations in secure data protocols.