## Diagram: Speculative Execution with Short and Long Access
### Overview
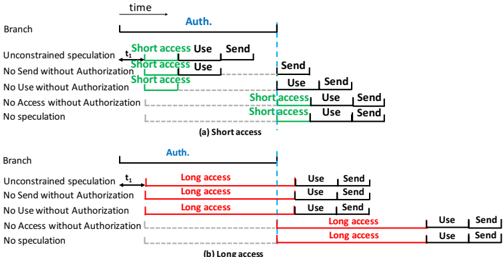
The image presents two diagrams illustrating speculative execution scenarios, contrasting "Short access" and "Long access" patterns across different branches with varying authorization constraints. The diagrams depict the timing of "Access," "Use," and "Send" operations relative to an "Auth." (Authorization) point.
### Components/Axes
* **X-axis:** "time" - Represents the progression of time from left to right.
* **Y-axis:** "Branch" - Lists different branches or execution paths, including:
* Unconstrained speculation
* No Send without Authorization
* No Use without Authorization
* No Access without Authorization
* No speculation
* **Auth.:** Authorization point, indicated by a vertical dashed blue line.
* **t1:** A specific time point marked on the timeline.
* **Operations:** "Short access", "Long access", "Use", "Send" - Represent different operations performed during execution.
* **(a) Short access:** Title for the first diagram.
* **(b) Long access:** Title for the second diagram.
### Detailed Analysis
#### (a) Short access
* **Unconstrained speculation:** Starts with "t1", followed by a "Short access" (green), then "Use", and finally "Send".
* **No Send without Authorization:** Starts with "Short access" (green), then "Use", and finally "Send".
* **No Use without Authorization:** Starts with "Short access" (green), then "Use", and finally "Send".
* **No Access without Authorization:** Starts with "Short access" (green), then "Use", and finally "Send".
* **No speculation:** Starts with "Short access" (green), then "Use", and finally "Send".
#### (b) Long access
* **Unconstrained speculation:** Starts with "t1", followed by a "Long access" (red), then "Use", and finally "Send".
* **No Send without Authorization:** Starts with "Long access" (red), then "Use", and finally "Send".
* **No Use without Authorization:** Starts with "Long access" (red), then "Use", and finally "Send".
* **No Access without Authorization:** Starts with "Long access" (red), then "Use", and finally "Send".
* **No speculation:** Starts with "Long access" (red), then "Use", and finally "Send".
### Key Observations
* The "Short access" scenarios (a) all involve a shorter access time before authorization, represented by green bars.
* The "Long access" scenarios (b) all involve a longer access time before authorization, represented by red bars.
* The "Auth." point seems to gate or influence the subsequent "Use" and "Send" operations.
* The "No speculation" branch appears to have a delayed start compared to "Unconstrained speculation" in both diagrams.
### Interpretation
The diagrams illustrate how different authorization constraints affect the timing of speculative execution. The "Short access" scenarios suggest a more immediate access attempt, while "Long access" scenarios indicate a delayed or extended access period. The "Auth." point likely represents a security check or permission verification. The different branches represent varying levels of security policies, with "No [Action] without Authorization" branches enforcing stricter controls. The diagrams highlight the trade-offs between performance (early speculation) and security (authorization checks).