\n
## Diagram: Branch Speculation Timing Analysis (Short vs. Long Access)
### Overview
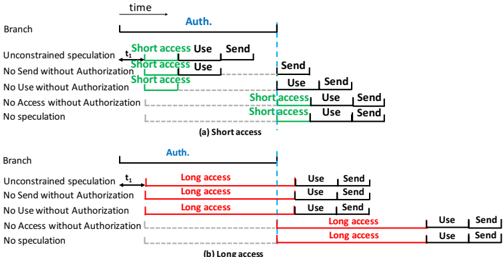
This is a technical diagram comparing two scenarios of speculative execution in a processor branch prediction context. It illustrates the timing relationship between branch speculation, authorization ("Auth."), and memory access operations ("Use" and "Send") for five different security or operational configurations. The diagram is split into two panels: (a) Short access and (b) Long access, showing how the duration of the access phase affects the sequence of events.
### Components/Axes
* **Primary Structure:** Two horizontal timelines, labeled (a) and (b), representing the flow of time from left to right.
* **Vertical Axis (Left Labels):** Lists five branch/speculation configurations for each panel:
1. Unconstrained speculation
2. No Send without Authorization
3. No Use without Authorization
4. No Access without Authorization
5. No speculation
* **Horizontal Axis:** Implicitly represents time, indicated by a right-pointing arrow labeled "time" at the top.
* **Key Event Marker:** A vertical dashed blue line labeled "Auth." (Authorization) cuts through both timelines, serving as a critical synchronization point.
* **Action Labels:** The primary actions plotted on the timelines are "Use" and "Send".
* **Access Duration Indicators:**
* **Panel (a):** Green text and brackets labeled "Short access".
* **Panel (b):** Red text and brackets labeled "Long access".
* **Flow Lines:** Solid black horizontal lines represent the active timeline for each configuration. Dashed gray lines indicate inactive or non-speculative paths.
### Detailed Analysis
The diagram details the sequence of events for each configuration under two different access timing conditions.
**Panel (a) Short Access:**
* **Trend:** For the top three configurations ("Unconstrained speculation", "No Send without Authorization", "No Use without Authorization"), the "Short access" phase (green) begins *before* the "Auth." line. The "Use" action occurs within this pre-authorization access window, and the "Send" action occurs *after* authorization.
* **Data Points/Sequence:**
* **Unconstrained speculation:** `Short access` -> `Use` -> `Auth.` -> `Send`
* **No Send without Authorization:** `Short access` -> `Use` -> `Auth.` -> `Send`
* **No Use without Authorization:** `Short access` -> `Use` -> `Auth.` -> `Send`
* **No Access without Authorization:** `Auth.` -> `Short access` -> `Use` -> `Send` (Access starts only after Auth.)
* **No speculation:** `Auth.` -> `Short access` -> `Use` -> `Send` (Identical to the previous line, no speculative action before Auth.)
**Panel (b) Long Access:**
* **Trend:** The "Long access" phase (red) is significantly extended. For the top three configurations, it starts before "Auth." and continues well past it. The "Use" action is embedded within this long access window, and the "Send" action occurs at the end of it, *after* authorization.
* **Data Points/Sequence:**
* **Unconstrained speculation:** `Long access` (starts pre-Auth) -> `Use` (pre-Auth) -> `Auth.` -> `Send` (post-Auth)
* **No Send without Authorization:** `Long access` (starts pre-Auth) -> `Use` (pre-Auth) -> `Auth.` -> `Send` (post-Auth)
* **No Use without Authorization:** `Long access` (starts pre-Auth) -> `Use` (pre-Auth) -> `Auth.` -> `Send` (post-Auth)
* **No Access without Authorization:** `Auth.` -> `Long access` -> `Use` -> `Send` (Access starts only after Auth.)
* **No speculation:** `Auth.` -> `Long access` -> `Use` -> `Send` (Identical to the previous line.)
### Key Observations
1. **Critical Authorization Line:** The "Auth." line is the pivotal event. Configurations 1-3 allow speculative access ("Use") to begin before this line, while configurations 4-5 strictly enforce that all access begins only after authorization.
2. **Access Duration Impact:** The core difference between panels (a) and (b) is the length of the access window. A "Long access" window means the speculative "Use" action occurs earlier relative to the "Send" action and the "Auth." point.
3. **Identical Non-Speculative Paths:** The last two configurations ("No Access without Authorization" and "No speculation") produce identical event sequences in both panels, as they prohibit any action before authorization.
4. **Color-Coded Semantics:** Green ("Short access") and Red ("Long access") are used consistently to denote the two timing regimes, with the text and bracket color matching the described access type.
### Interpretation
This diagram is a pedagogical or analytical tool for understanding microarchitectural side-channel vulnerabilities (like Spectre variants). It models how different hardware or software security policies ("No Send without Authorization", etc.) interact with speculative execution.
* **What it demonstrates:** It visually argues that the *duration* of a speculative access window ("Short" vs. "Long") changes the temporal relationship between the speculative operation ("Use") and the architectural commitment ("Send") relative to a security checkpoint ("Auth."). A longer access window increases the time an attacker has to manipulate or measure the speculative state before it is resolved.
* **Relationships:** The configurations represent a spectrum from most permissive ("Unconstrained speculation") to most restrictive ("No speculation"). The diagram shows that policies restricting "Use" or "Access" (configs 3 & 4) are more effective at preventing pre-authorization activity than policies only restricting "Send" (config 2).
* **Notable Anomaly/Insight:** The key insight is that simply requiring authorization before a "Send" operation (config 2) is insufficient to prevent speculative "Use" of data, as the "Use" can still occur in the pre-auth window. Effective mitigation requires blocking the "Use" or the "Access" itself before authorization (configs 3 & 4). The "Long access" scenario exacerbates the vulnerability window for the permissive configurations.