## Diagram Type: Flowchart
### Overview
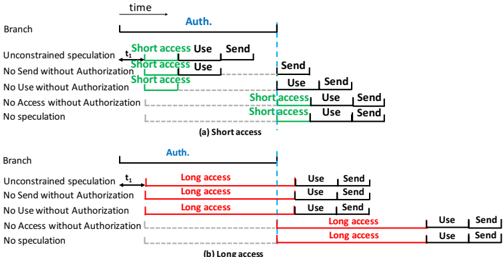
The image is a flowchart that illustrates the process of accessing data based on authorization levels. It is divided into two main sections: (a) Short access and (b) Long access.
### Components/Axes
- **Branch**: Represents the different authorization levels.
- **Auth.**: Indicates whether access is authorized or not.
- **Short access**: Denoted by green lines, this section shows the process for accessing data with short authorization.
- **Long access**: Denoted by red lines, this section shows the process for accessing data with long authorization.
- **time**: Represents the duration of the access process.
- **Use**: Indicates the action taken during the access process.
- **Send**: Indicates the action taken after the access process.
### Detailed Analysis or ### Content Details
- **Short access**:
- **No Send without Authorization**: Access is denied if authorization is not provided.
- **No Use without Authorization**: Access is denied if authorization is not provided.
- **No Access without Authorization**: Access is denied if authorization is not provided.
- **No speculation**: Access is denied if speculation is made without authorization.
- **Long access**:
- **No Send without Authorization**: Access is denied if authorization is not provided.
- **No Use without Authorization**: Access is denied if authorization is not provided.
- **No Access without Authorization**: Access is denied if authorization is not provided.
- **No speculation**: Access is denied if speculation is made without authorization.
### Key Observations
- The flowchart clearly outlines the process for accessing data with short and long authorization levels.
- Both short and long access sections have the same restrictions, indicating that authorization is a critical factor in accessing data.
- The flowchart uses color-coding to differentiate between short and long access, making it easy to understand the process.
### Interpretation
The data suggests that authorization is a crucial factor in accessing data. Both short and long access sections have the same restrictions, indicating that authorization is a critical factor in accessing data. The flowchart clearly outlines the process for accessing data with short and long authorization levels, making it easy to understand the process. The use of color-coding to differentiate between short and long access makes it easy to understand the process. The data suggests that authorization is a crucial factor in accessing data.