\n
## Diagram: Secure Software Deployment Process
### Overview
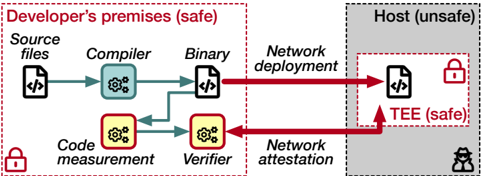
The image depicts a diagram illustrating a secure software deployment process, contrasting a "Developer's premises (safe)" environment with a "Host (unsafe)" environment. The diagram outlines the flow of source code through compilation, verification, and deployment, highlighting security measures like code measurement, attestation, and the use of a Trusted Execution Environment (TEE).
### Components/Axes
The diagram is divided into two main sections: "Developer's premises (safe)" on the left, and "Host (unsafe)" on the right. Within these sections, the following components are present:
* **Developer's premises:**
* Source files (represented by a file icon with `< />` inside)
* Compiler (represented by a gear icon)
* Binary (represented by a file icon with `< />` inside)
* Code measurement (represented by a gear icon)
* Verifier (represented by a gear icon)
* Network deployment (dashed red arrow)
* Network attestation (dashed red arrow)
* **Host:**
* Binary (represented by a file icon with `< />` inside)
* Trusted Execution Environment (TEE) (represented by a rectangle)
* **Security Indicators:** Padlock icons are present to indicate secure areas. A silhouette of a person is present to indicate a potential attacker.
* **Arrows:** Solid green arrows represent secure data flow, while dashed red arrows represent potentially insecure data flow.
### Detailed Analysis or Content Details
The diagram illustrates the following process:
1. **Source Files** are processed by the **Compiler** to create a **Binary**.
2. The **Binary** is subject to **Network deployment** to the **Host**.
3. Simultaneously, the **Source Files** are processed by **Code measurement** and then the **Verifier**.
4. The **Verifier** provides input to **Network attestation**.
5. **Network attestation** communicates with the **Host**.
6. The **Binary** on the **Host** is executed within a **TEE** (Trusted Execution Environment).
The diagram highlights the following security aspects:
* The "Developer's premises" are considered a "safe" environment, indicated by a red border and padlock icons.
* The "Host" is considered an "unsafe" environment, indicated by a gray background.
* The TEE within the Host is a "safe" environment, indicated by a red border and padlock icon.
* The flow from the Developer's premises to the Host via Network deployment is shown as a dashed red arrow, indicating a potential vulnerability.
* The flow from the Verifier to the Host via Network attestation is also shown as a dashed red arrow, indicating a potential vulnerability.
* The flow from Code measurement to the Verifier and from the Verifier to Network attestation are shown as solid green arrows, indicating secure data flow.
* The flow from Network attestation to the TEE is shown as a solid green arrow, indicating secure data flow.
### Key Observations
The diagram emphasizes the importance of verifying the integrity of the software before deployment to an untrusted host. The use of code measurement and network attestation aims to establish trust in the deployed binary. The TEE provides a secure execution environment on the host, protecting the binary from malicious attacks. The dashed red arrows highlight potential attack vectors during network deployment and attestation.
### Interpretation
This diagram illustrates a security architecture for deploying software to an untrusted host. The core idea is to establish trust in the software before it is executed on the host. This is achieved through code measurement, verification, and network attestation. The TEE provides a secure environment for executing the software, even on a compromised host. The diagram suggests a layered security approach, where multiple security mechanisms are employed to mitigate the risk of attacks. The use of color-coded arrows effectively communicates the level of trust associated with each data flow. The diagram is a conceptual representation of a secure software deployment process and does not provide specific details about the implementation of each component. It is a high-level overview of the security architecture. The presence of the attacker silhouette suggests that the system is designed to defend against malicious actors. The diagram implies that the developer has control over the "safe" environment, while the host environment is potentially compromised. The goal is to minimize the impact of a compromised host by isolating the software within a TEE and verifying its integrity before execution.