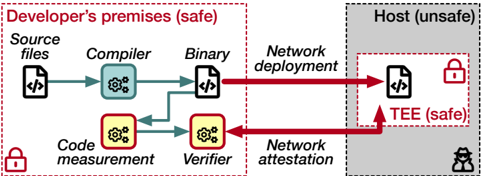
## [System Architecture Diagram]: Secure Software Deployment via Trusted Execution Environment (TEE)
### Overview
This diagram illustrates a secure software deployment workflow that separates a trusted development environment from an untrusted host environment, using a Trusted Execution Environment (TEE) and cryptographic attestation to ensure code integrity. The process involves compiling source code, measuring it, deploying it to a secure enclave on a remote host, and verifying its integrity before execution.
### Components/Axes
The diagram is divided into two primary spatial regions:
1. **Left Region: "Developer's premises (safe)"**
* **Boundary:** Enclosed by a red dashed rectangle with a lock icon in the bottom-left corner, indicating a secure, trusted zone.
* **Components (from left to right):**
* **Source files:** Represented by a document icon with code symbols (`</>`).
* **Compiler:** Represented by a gear icon inside a rounded square.
* **Binary:** Represented by a document icon with code symbols (`</>`).
* **Code measurement:** Represented by a gear icon inside a rounded square.
* **Verifier:** Represented by a gear icon inside a rounded square with a red outline.
2. **Right Region: "Host (unsafe)"**
* **Boundary:** A gray shaded rectangle, indicating an untrusted environment.
* **Sub-component:**
* **TEE (safe):** A smaller red dashed rectangle within the host, containing a document icon with code symbols (`</>`) and a lock icon. This represents the secure enclave.
3. **Flow Arrows & Labels:**
* **Internal Flow (within Developer's premises):** Arrows connect `Source files` → `Compiler` → `Binary`. A separate loop connects `Binary` → `Code measurement` → `Verifier`, with a return arrow from `Verifier` back to `Compiler`.
* **External Flow (between regions):**
* A thick red arrow labeled **"Network deployment"** points from the `Binary` in the safe zone to the `TEE (safe)` in the unsafe zone.
* A thick red arrow labeled **"Network attestation"** points from the `TEE (safe)` back to the `Verifier` in the safe zone.
### Detailed Analysis
The workflow proceeds in a specific sequence:
1. **Build & Measure Phase (Safe Zone):**
* `Source files` are processed by the `Compiler` to produce a `Binary`.
* The `Binary` undergoes `Code measurement` (likely generating a cryptographic hash or signature).
* The measurement is sent to the `Verifier`. The `Verifier` can communicate back to the `Compiler`, possibly to halt the process if verification fails.
2. **Deployment & Attestation Phase (Cross-Zone):**
* The `Binary` is sent via **"Network deployment"** to the `TEE (safe)` on the remote, untrusted `Host`.
* The `TEE` then performs **"Network attestation"**—sending a cryptographic proof of its identity and the integrity of the loaded code—back to the `Verifier` in the trusted developer zone.
### Key Observations
* **Security Boundary Demarcation:** The use of red dashed lines for "safe" zones (developer premises and TEE) versus a solid gray block for the "unsafe" host is a critical visual cue for trust boundaries.
* **Central Role of the Verifier:** The `Verifier` is the only component with a red outline, highlighting its critical role as the trust anchor. It receives measurements from the local build process and attestations from the remote TEE.
* **Bidirectional Communication:** The loop between `Verifier` and `Compiler` suggests a feedback mechanism for build control. The attestation arrow completes a verification loop across the network.
* **Iconography:** Lock icons explicitly denote secure areas. Gear icons represent processing steps (compilation, measurement, verification). Document icons represent data artifacts (source, binary).
### Interpretation
This diagram models a **trusted computing** or **confidential computing** deployment pipeline. Its purpose is to solve the problem of deploying software to an untrusted host (e.g., a cloud server) while maintaining assurance that the correct, unaltered code is running in a protected environment.
* **How Elements Relate:** The system creates a chain of trust. The developer's safe zone is the root of trust. The `Code measurement` creates a fingerprint of the binary. The `Verifier` acts as the policy decision point. The `TEE` on the untrusted host provides a hardware-isolated safe haven for execution. The **"Network attestation"** is the crucial step that cryptographically proves to the `Verifier` that the remote TEE is genuine and is running the exact binary that was measured and approved.
* **Underlying Principle:** The workflow ensures that even if the host operating system or infrastructure is compromised ("unsafe"), the application code and data within the `TEE` remain confidential and integrity-protected. The attestation allows the developer to verify the remote environment *before* releasing sensitive data or secrets to it.
* **Notable Implication:** The diagram emphasizes that security is not just about the final deployed state but involves a verifiable process from build to runtime. The separation of "deployment" (sending the binary) and "attestation" (proving its safe execution) is a key architectural pattern for zero-trust environments.