## Diagram: Secure Software Deployment Architecture
### Overview
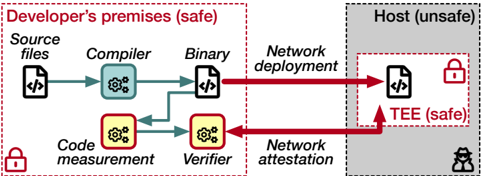
The diagram illustrates a secure software deployment workflow divided into two primary zones:
1. **Developer's premises (safe)** - A secure development environment
2. **Host (unsafe)** - An external, potentially compromised system
The architecture emphasizes code integrity verification and secure execution through a Trusted Execution Environment (TEE).
---
### Components/Axes
**Left Section (Developer's Premises):**
- **Source files** (paper icon with `</>`)
- **Compiler** (gears icon)
- **Binary** (paper icon with `</>`)
- **Code measurement** (gears icon in yellow)
- **Verifier** (gears icon in yellow)
**Right Section (Host):**
- **Network deployment** (red arrow from binary)
- **Network attestation** (red arrow from verifier)
- **TEE (safe)** (paper icon with `</>` + lock symbol)
- **Host (unsafe)** (gray background with detective icon)
**Flow Arrows:**
- Blue arrows: Internal development workflow
- Red arrows: Network interactions
---
### Detailed Analysis
1. **Development Workflow:**
- Source files → Compiler → Binary
- Binary splits into two paths:
- Direct deployment to the host (network deployment)
- Code measurement → Verifier (feedback loop for validation)
2. **Host Interaction:**
- Network deployment delivers binary to the host.
- Network attestation verifies code integrity before execution.
- TEE (safe enclave) executes the code, isolated from the unsafe host environment.
3. **Security Indicators:**
- Lock symbols on source files and TEE denote cryptographic protection.
- Detective icon on the host implies monitoring for threats.
---
### Key Observations
- **Dual-Security Model:**
- Developer's premises ensure code correctness pre-deployment.
- TEE provides runtime security despite the host's unsafe nature.
- **Attestation Criticality:**
- Network attestation acts as a gatekeeper, validating code before TEE execution.
- **Feedback Loop:**
- Code measurement and verifier enable iterative validation of binaries.
---
### Interpretation
This architecture demonstrates a **zero-trust deployment model** where:
1. **Pre-Deployment Security:**
- Code is rigorously validated (compilation, measurement, verification) before leaving the developer's environment.
2. **Runtime Protection:**
- The TEE isolates execution from the host's vulnerabilities, ensuring even compromised hosts cannot tamper with critical operations.
3. **Network Risks:**
- The red arrows highlight network deployment as a potential attack vector, mitigated by attestation checks.
The detective icon suggests continuous monitoring of the host, while lock symbols emphasize cryptographic safeguards. The TEE's "safe" label contrasts sharply with the host's "unsafe" designation, underscoring the necessity of secure enclaves in untrusted environments.