## Diagram: Protocol Negotiation and Data Access
### Overview
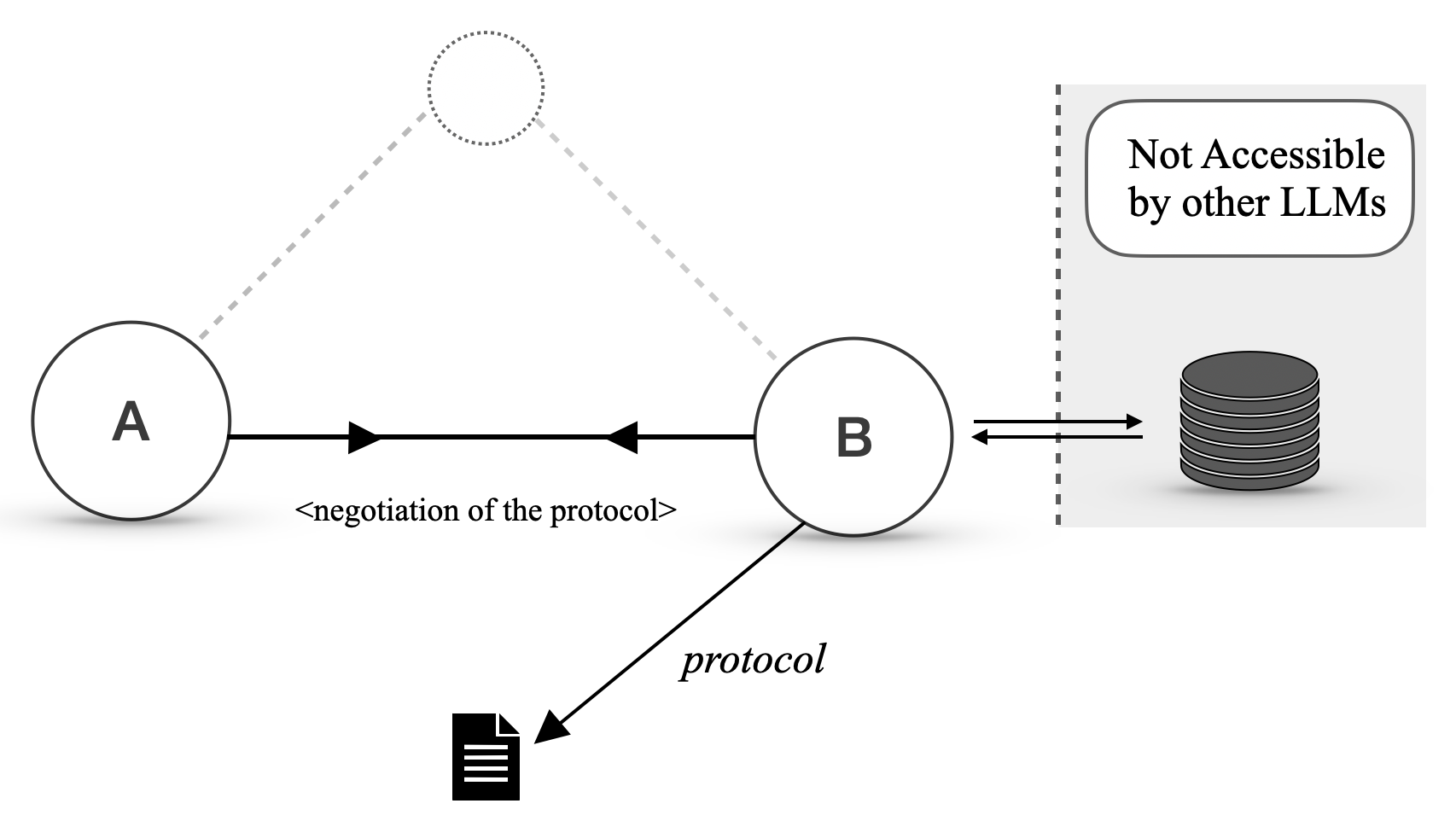
The image is a diagram illustrating a process involving two entities, labeled A and B, and their interaction with a data storage component that is "Not Accessible by other LLMs". The diagram shows a negotiation phase between A and B, followed by B accessing the data storage based on a defined protocol.
### Components/Axes
* **Nodes:**
* Node A: A circle labeled "A".
* Node B: A circle labeled "B".
* Dotted Node: A circle made of dots, located above and between A and B.
* **Data Storage:** A stack of disks, located on the right side of the diagram. It is contained within a rounded rectangle with the label "Not Accessible by other LLMs".
* **Connections:**
* Solid Arrow: A solid arrow pointing from A to B, labeled "<negotiation of the protocol>".
* Solid Arrow: A solid arrow pointing from B to a document icon, labeled "protocol".
* Double Arrow: A double arrow pointing between B and the data storage.
* Dashed Lines: Dashed lines connecting the dotted node to A and B.
### Detailed Analysis or ### Content Details
* **Node A:** Located on the left side of the diagram.
* **Node B:** Located on the right side of the diagram.
* **Negotiation:** A solid arrow indicates the negotiation of the protocol from A to B. The text label is "<negotiation of the protocol>".
* **Protocol:** A solid arrow indicates the protocol from B to a document icon. The text label is "protocol".
* **Data Access:** A double arrow indicates the data access between B and the data storage.
* **Data Storage:** The data storage is labeled "Not Accessible by other LLMs", indicating that it is isolated from other Large Language Models (LLMs).
### Key Observations
* The diagram highlights a process where A and B negotiate a protocol, and B then uses this protocol to access a specific data storage.
* The data storage is explicitly marked as not accessible by other LLMs, suggesting a security or privacy constraint.
* The dotted node and dashed lines suggest a potential third party or intermediary, but its role is not explicitly defined.
### Interpretation
The diagram illustrates a secure data access scenario. Entity A and Entity B negotiate a protocol. Entity B then uses this protocol to access a data storage that is isolated from other LLMs. This isolation suggests a controlled environment, possibly to protect sensitive data or ensure compliance with specific regulations. The negotiation step implies that access is not granted freely but requires a prior agreement or authentication process. The dotted node could represent a trusted third party involved in the negotiation or a shared resource used by both A and B.