\n
## Diagram: System Interaction & Protocol Negotiation
### Overview
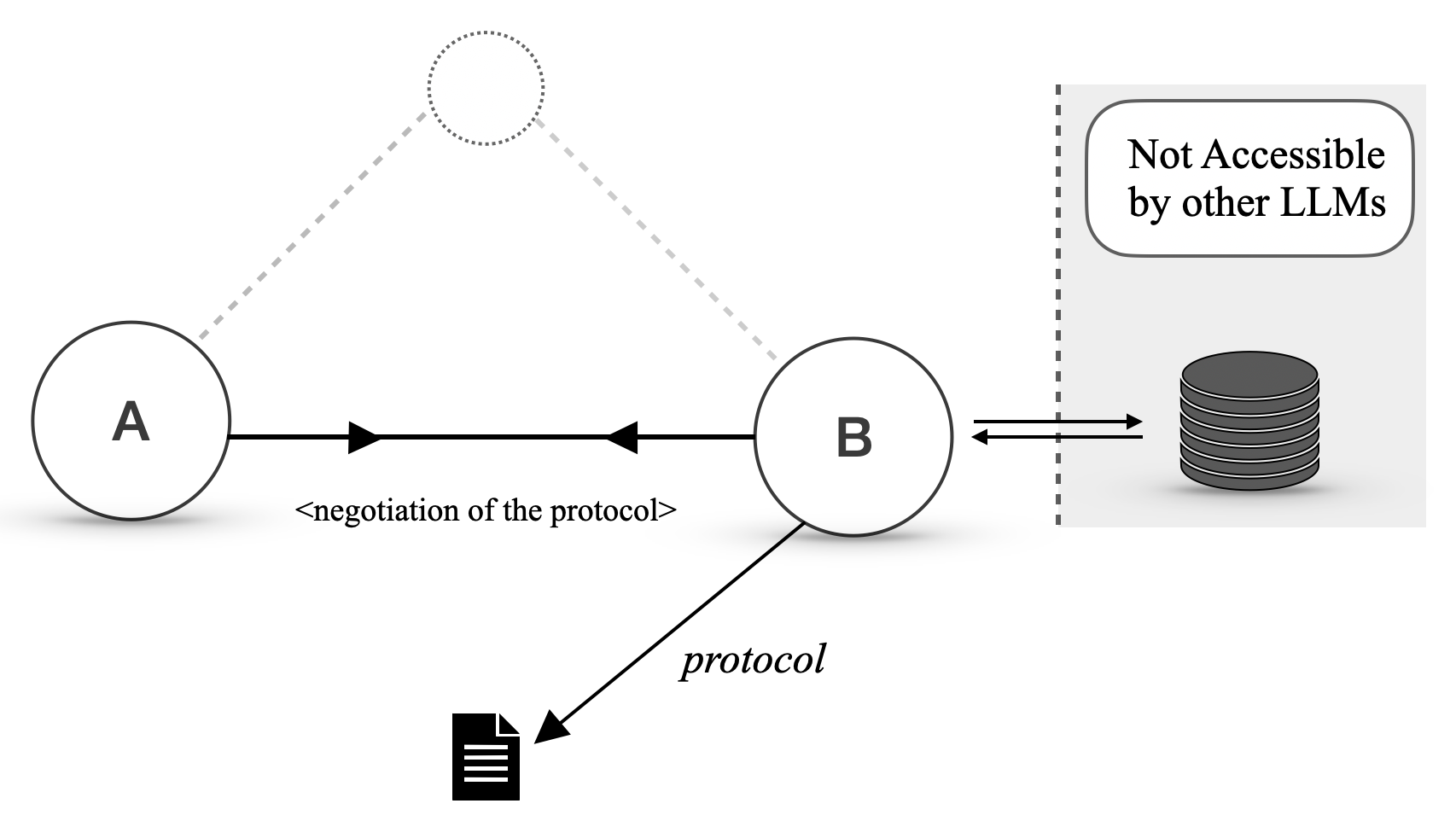
The image depicts a diagram illustrating the interaction between two entities, labeled 'A' and 'B', involving protocol negotiation and access to a data source. The diagram uses circles to represent entities, arrows to indicate data flow, and a dashed box to denote a restricted access area.
### Components/Axes
The diagram consists of the following components:
* **Entity A:** Represented by a circle labeled "A".
* **Entity B:** Represented by a circle labeled "B".
* **Data Source:** Represented by a cylinder stack, indicating a database or storage system.
* **Protocol:** Represented by a document icon with lines, labeled "protocol".
* **Negotiation Flow:** A solid arrow labeled "<negotiation of the protocol>" connecting A and B.
* **Data Flow:** A solid arrow connecting B and the Data Source.
* **Restricted Access:** A dashed box surrounding the Data Source, with the text "Not Accessible by other LLMs".
* **Potential Connection:** A dotted arrow originating from A and pointing towards B, with a dotted circle at the end.
### Detailed Analysis or Content Details
The diagram shows a flow of information:
1. Entity A initiates a protocol negotiation with Entity B, indicated by the arrow labeled "<negotiation of the protocol>".
2. Entity B accesses a data source (database) and retrieves information.
3. Entity B utilizes a "protocol" (represented by the document icon) to interact with the data source.
4. The data source is explicitly marked as inaccessible to other LLMs.
5. There is a potential, but not confirmed, connection from A to B, indicated by the dotted arrow.
### Key Observations
* The diagram emphasizes the importance of protocol negotiation between entities A and B.
* The data source is specifically protected from access by other LLMs, suggesting a security or privacy concern.
* The dotted arrow indicates a possible, but not guaranteed, communication path between A and B.
* The diagram does not provide any quantitative data or specific details about the protocol itself.
### Interpretation
The diagram illustrates a secure system architecture where Entity A interacts with a data source through Entity B. The protocol negotiation step suggests a dynamic or adaptable communication process. The restriction on access for other LLMs highlights a focus on data security and control. The dotted line from A to B suggests a potential for direct communication, but it is not a guaranteed or primary pathway. This setup could represent a scenario where Entity A requests data from Entity B, which then retrieves it from a protected database, ensuring that the data remains inaccessible to unauthorized entities. The diagram is conceptual and does not provide specific implementation details. It focuses on the relationships and access control mechanisms within the system.