## System Interaction Diagram: Protocol Negotiation and Data Access Control
### Overview
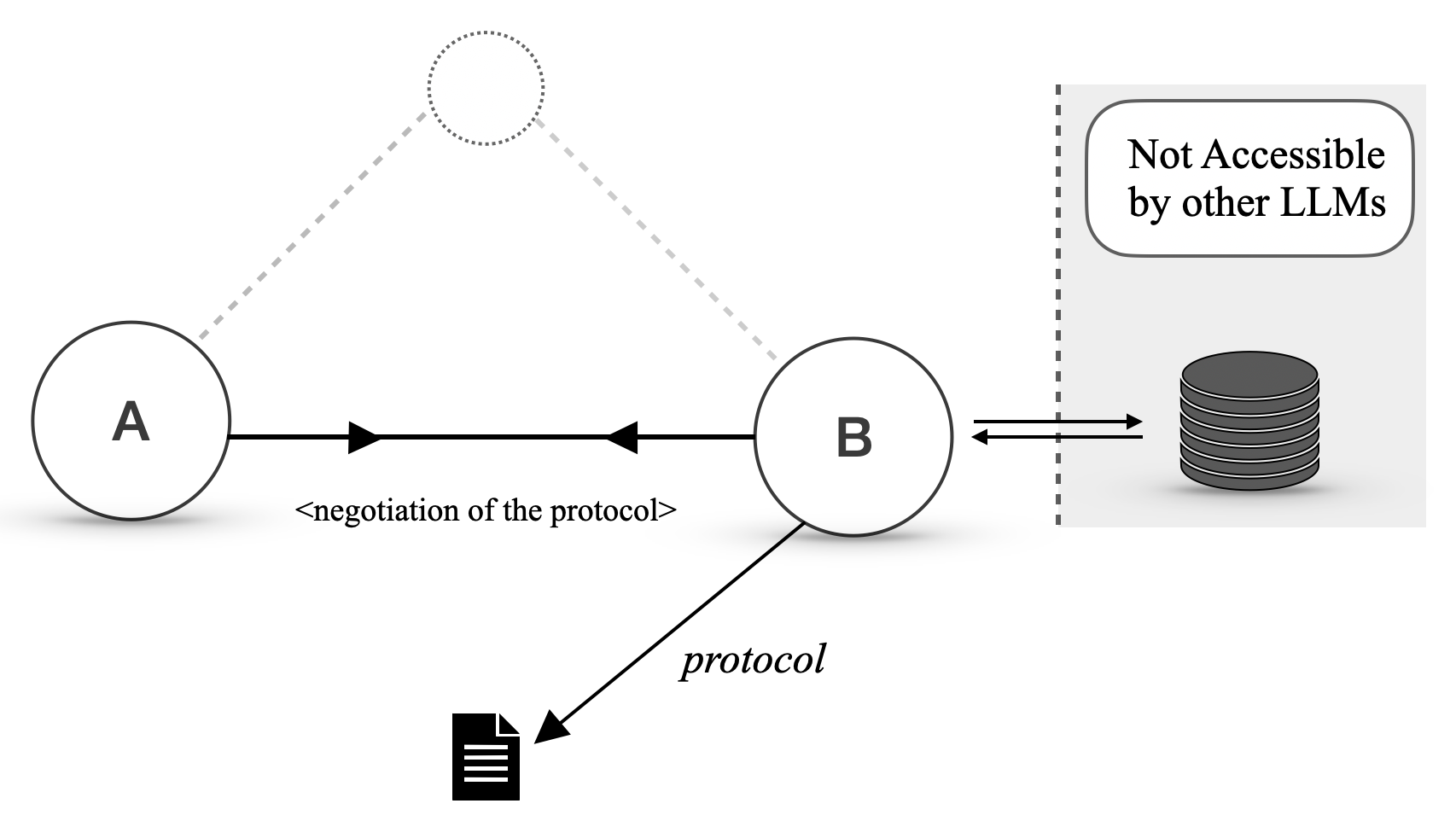
The diagram illustrates a technical interaction between two components (A and B) involving protocol negotiation and data exchange. A third element, a database stack, is marked as "Not Accessible by other LLMs," indicating restricted access. The flow includes bidirectional communication between A and B, a protocol document, and a unidirectional connection to the database.
### Components/Axes
1. **Nodes**:
- **A**: Leftmost circle labeled "A"
- **B**: Rightmost circle labeled "B"
- **Database**: Stack of disks labeled "Not Accessible by other LLMs"
2. **Connectors**:
- **Bidirectional Arrow**: Between A and B, labeled "<negotiation of the protocol>"
- **Unidirectional Arrow**: From B to the database
- **Dashed Lines**: Connecting A and B to an unlabeled central node (possibly a mediator or shared resource)
3. **Symbols**:
- **Document Icon**: Labeled "protocol" pointing to B
### Detailed Analysis
- **Protocol Negotiation**: The bidirectional arrow between A and B suggests a mutual exchange of protocol definitions or parameters. The label "<negotiation of the protocol>" implies dynamic adjustment or agreement on communication standards.
- **Data Flow**: The unidirectional arrow from B to the database indicates that B transmits data to the database after protocol negotiation. The database’s inaccessibility to other LLMs implies encryption, access controls, or proprietary formatting.
- **Dashed Lines**: These may represent indirect dependencies (e.g., shared libraries, environmental variables) or non-critical interactions between A and B.
### Key Observations
1. **Exclusivity**: The database’s restriction to "other LLMs" suggests A and B operate within a closed ecosystem, prioritizing data privacy or security.
2. **Negotiation Dependency**: The protocol negotiation is central to the interaction, acting as a gatekeeper for subsequent data exchange.
3. **Unidirectional Data Transfer**: Data flows only from B to the database, not vice versa, indicating a one-way submission or logging process.
### Interpretation
This diagram likely represents a secure data pipeline where components A and B must first agree on a protocol before B can submit data to a restricted database. The exclusivity of the database implies that A and B are part of a specialized system (e.g., a private AI model or compliance-driven application) where external LLMs (e.g., third-party models) are barred from accessing sensitive data. The dashed lines hint at shared infrastructure or dependencies that enable the negotiation process but are not part of the core data flow. The absence of feedback loops or error-handling mechanisms suggests a simplified or idealized representation of the system.