## Diagram: Homomorphic Encryption
### Overview
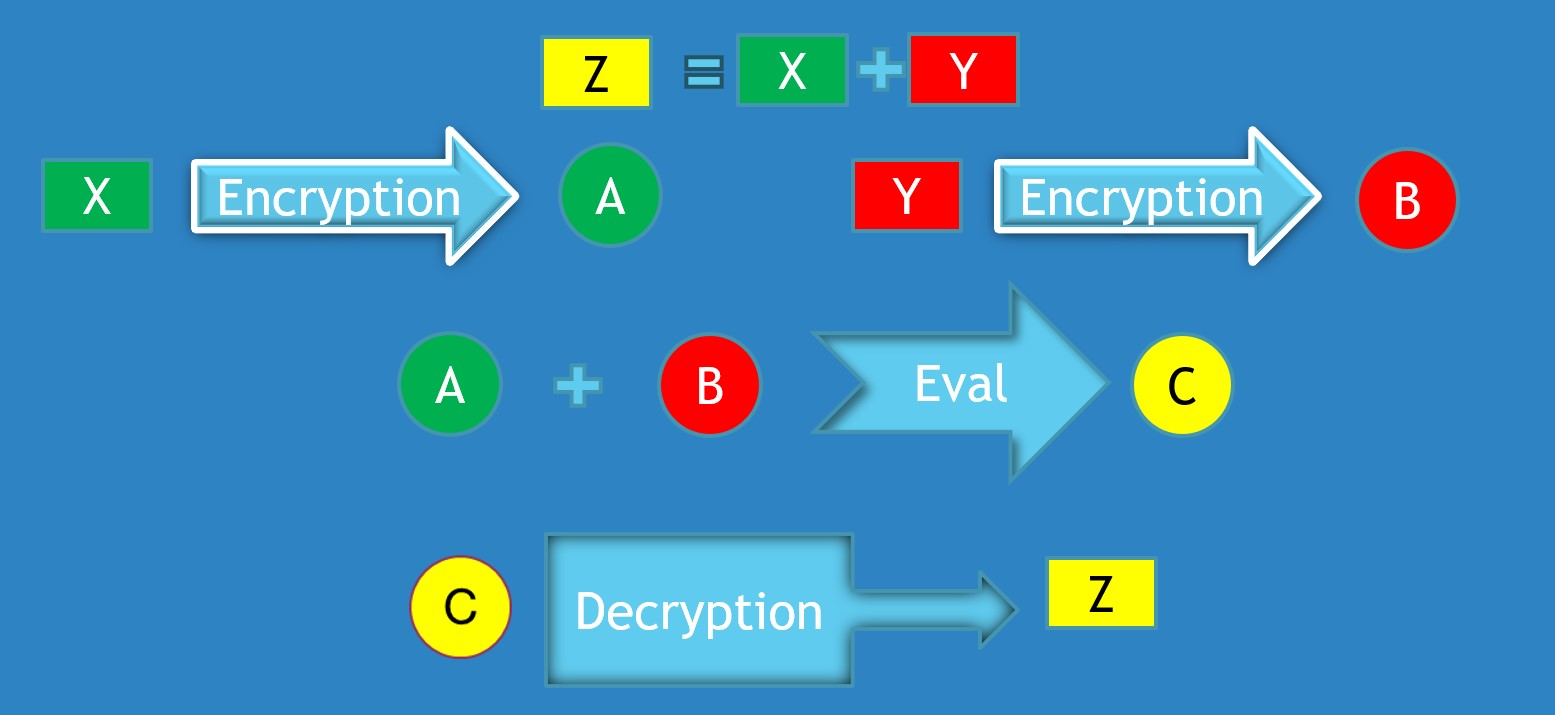
The image illustrates a simplified diagram of a homomorphic encryption process. It shows how two inputs, X and Y, are encrypted separately, then evaluated in their encrypted forms, and finally decrypted to produce a result Z, which is equivalent to X + Y.
### Components/Axes
* **Shapes:** Rectangles, Circles, Arrows
* **Colors:** Green, Red, Yellow, Blue
* **Text Labels:** X, Y, Z, A, B, C, Encryption, Decryption, Eval, +, =
### Detailed Analysis
1. **Top Row:**
* A yellow rectangle labeled "Z" is positioned on the top-left.
* An equals sign (=) is next to "Z".
* A green rectangle labeled "X" is next to the equals sign.
* A plus sign (+) is next to "X".
* A red rectangle labeled "Y" is next to the plus sign.
* The equation "Z = X + Y" is formed.
2. **First Encryption Branch (Left):**
* A green rectangle labeled "X" is present.
* A light blue arrow labeled "Encryption" points from "X" to a green circle labeled "A".
3. **Second Encryption Branch (Right):**
* A red rectangle labeled "Y" is present.
* A light blue arrow labeled "Encryption" points from "Y" to a red circle labeled "B".
4. **Evaluation:**
* A green circle labeled "A" is present.
* A plus sign (+) is next to "A".
* A red circle labeled "B" is next to the plus sign.
* A light blue arrow labeled "Eval" points from "A + B" to a yellow circle labeled "C".
5. **Decryption:**
* A yellow circle labeled "C" is present.
* A light blue arrow labeled "Decryption" points from "C" to a yellow rectangle labeled "Z".
### Key Observations
* The diagram visually represents the process of homomorphic encryption, where operations can be performed on encrypted data.
* The colors (green, red, yellow) seem to differentiate the data at different stages of the process.
* The arrows indicate the flow of data and the transformations applied to it.
### Interpretation
The diagram illustrates the core concept of homomorphic encryption. It demonstrates that by encrypting X and Y separately, performing an evaluation (addition in this case) on the encrypted values (A and B), and then decrypting the result (C), one can obtain the same result (Z) as if the addition was performed on the original unencrypted values of X and Y. This is significant because it allows computations to be performed on sensitive data without ever exposing the raw data itself, maintaining privacy and security.