## Flowchart: Cryptographic Process Diagram
### Overview
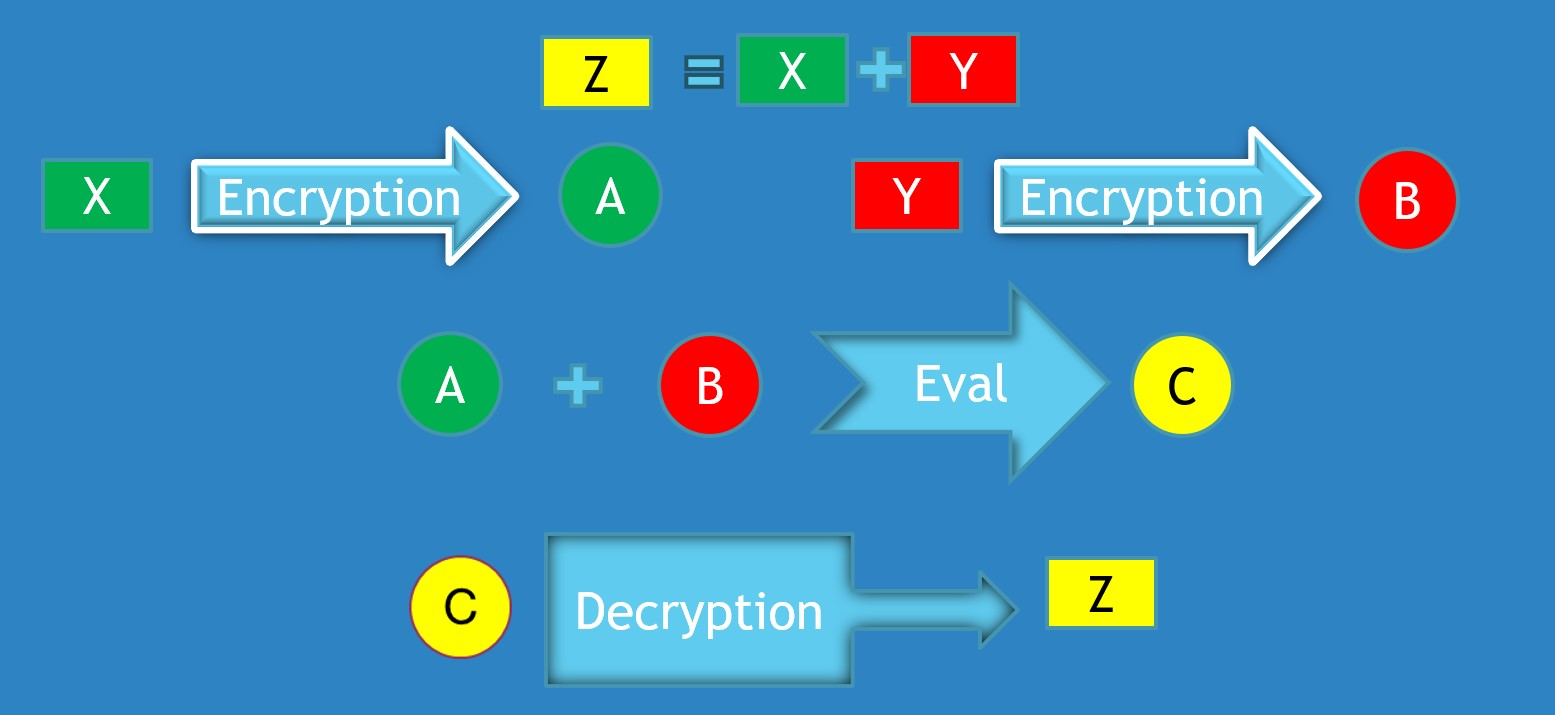
The image depicts a cryptographic workflow involving encryption, evaluation, and decryption steps. It uses colored shapes (rectangles, circles) and arrows to represent data transformations and operations. The diagram emphasizes relationships between variables (X, Y, Z, A, B, C) and processes (Encryption, Decryption, Eval).
### Components/Axes
- **Legend**: Located at the top-center, associating colors with variables:
- Yellow: `Z`
- Green: `X`
- Red: `Y`
- **Key Elements**:
- **Input Variables**:
- `X` (green rectangle, top-left)
- `Y` (red rectangle, top-right)
- **Intermediate Variables**:
- `A` (green circle, middle-left)
- `B` (red circle, middle-right)
- `C` (yellow circle, bottom-center)
- **Output Variable**:
- `Z` (yellow rectangle, top-center)
- **Processes**:
- **Encryption**: Arrows labeled "Encryption" (blue with white text) connecting `X`→`A` and `Y`→`B`.
- **Evaluation**: Arrow labeled "Eval" (blue with white text) connecting `A`+`B`→`C`.
- **Decryption**: Arrow labeled "Decryption" (blue with white text) connecting `C`→`Z`.
### Detailed Analysis
1. **Top Equation**:
- `Z = X + Y` (yellow rectangle `Z` equals green `X` + red `Y`).
2. **Encryption Steps**:
- `X` (green) → `A` (green circle) via "Encryption" arrow.
- `Y` (red) → `B` (red circle) via "Encryption" arrow.
3. **Evaluation**:
- `A` (green circle) + `B` (red circle) → `C` (yellow circle) via "Eval" arrow.
4. **Decryption**:
- `C` (yellow circle) → `Z` (yellow rectangle) via "Decryption" arrow.
### Key Observations
- **Color Consistency**:
- Green (`X`, `A`) and red (`Y`, `B`) maintain their colors through encryption.
- Yellow (`Z`, `C`) represents the final output in both the equation and decryption.
- **Flow Direction**:
- Left-to-right (encryption), top-to-bottom (evaluation), and right-to-left (decryption).
- **No Numerical Data**: The diagram focuses on symbolic relationships rather than quantitative values.
### Interpretation
This diagram illustrates a **homomorphic encryption workflow**, where:
1. **Inputs** (`X`, `Y`) are encrypted into ciphertexts (`A`, `B`).
2. **Operations** (addition) are performed on encrypted data (`A + B`) to produce an intermediate result (`C`).
3. **Decryption** of `C` yields the final output (`Z`), which matches the original equation `Z = X + Y`.
The use of color coding and directional arrows emphasizes the separation of plaintext and ciphertext domains, a core principle in homomorphic encryption. The "Eval" step likely represents a verification or integrity check before decryption.
**Notable Insight**: The diagram abstracts cryptographic operations into a visual pipeline, highlighting how encrypted data can be manipulated without exposing raw values.