## Diagram: Side-Channel Attack Procedures for Image Recovery
### Overview
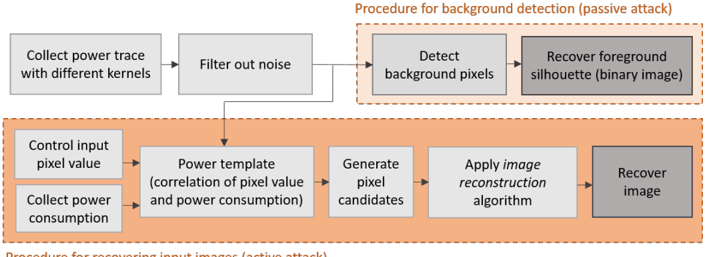
The image is a technical flowchart illustrating two distinct procedures for extracting image information through side-channel analysis of power consumption. It depicts a passive attack for background/foreground detection and an active attack for full image reconstruction. The diagram uses a clean, block-based layout with directional arrows to indicate process flow, enclosed within two dashed-line boxes that separate the two attack methodologies.
### Components/Axes
The diagram is organized into two primary, visually separated procedures:
1. **Top Procedure (Passive Attack):** Enclosed in a dashed orange box labeled **"Procedure for background detection (passive attack)"**.
* **Input Stage:** A block labeled **"Collect power trace with different kernels"**.
* **Processing Stage:** A block labeled **"Filter out noise"**.
* **Attack Core (within dashed box):**
* A block labeled **"Detect background pixels"**.
* An arrow points to a final, darker gray block labeled **"Recover foreground silhouette (binary image)"**.
2. **Bottom Procedure (Active Attack):** Enclosed in a larger dashed orange box labeled **"Procedure for recovering input images (active attack)"**.
* **Input/Control Stage (two parallel blocks on the left):**
* Top block: **"Control input pixel value"**.
* Bottom block: **"Collect power consumption"**.
* **Analysis & Reconstruction Flow:**
* Arrows from both input blocks lead to a central block: **"Power template (correlation of pixel value and power consumption)"**.
* An arrow leads to: **"Generate pixel candidates"**.
* An arrow leads to: **"Apply image reconstruction algorithm"**.
* An arrow leads to the final, darker gray block: **"Recover image"**.
**Visual Flow & Relationships:**
* A primary arrow flows from the "Filter out noise" block of the passive procedure down into the "Power template" block of the active procedure, indicating that filtered data from the passive phase can inform the active attack.
* The two procedures are presented as complementary or sequential methods, with the passive attack being simpler and focused on segmentation, while the active attack is more complex and aims for full reconstruction.
### Detailed Analysis
**Text Transcription (All text is in English):**
* **Procedure Titles:**
* "Procedure for background detection (passive attack)"
* "Procedure for recovering input images (active attack)"
* **Process Blocks (in order of flow):**
1. "Collect power trace with different kernels"
2. "Filter out noise"
3. "Detect background pixels"
4. "Recover foreground silhouette (binary image)"
5. "Control input pixel value"
6. "Collect power consumption"
7. "Power template (correlation of pixel value and power consumption)"
8. "Generate pixel candidates"
9. "Apply image reconstruction algorithm"
10. "Recover image"
**Spatial Grounding:**
* The **legend/labels** for the two main procedures are placed directly above their respective dashed-line containers, aligned to the top-right of each container.
* The **passive attack procedure** occupies the top ~40% of the diagram.
* The **active attack procedure** occupies the bottom ~60% of the diagram.
* The **final output blocks** ("Recover foreground silhouette" and "Recover image") are both shaded a darker gray, visually distinguishing them as the end results of their respective chains.
* The **connecting arrow** between the two procedures runs vertically from the bottom-center of the "Filter out noise" block to the top-center of the "Power template" block.
### Key Observations
1. **Two-Tiered Attack Strategy:** The diagram explicitly separates a simpler, passive reconnaissance attack (detecting background vs. foreground) from a more sophisticated, active attack (reconstructing the full image).
2. **Data Dependency:** The active attack is shown to potentially leverage pre-processed data ("Filter out noise") from the passive attack phase, suggesting a multi-stage attack pipeline.
3. **Core Mechanism:** The active attack hinges on building a **"Power template"** that models the correlation between a pixel's value and its associated power consumption. This template is the key to generating candidate pixels for reconstruction.
4. **Output Specificity:** The passive attack yields a **binary image** (silhouette), while the active attack aims to recover the full **image** (implying grayscale or color data).
### Interpretation
This diagram outlines a methodology for conducting **side-channel attacks on imaging systems**, where an adversary infers visual data by analyzing the power consumption patterns of a device (e.g., a camera sensor or image processor).
* **What it demonstrates:** It shows that such attacks are not monolithic. A **passive attack** can be performed by simply observing power traces during normal operation to segment a scene into background and foreground—a significant privacy breach in itself. An **active attack**, where the attacker can influence input (control pixel values), is more powerful and can reconstruct the actual image content by meticulously mapping the relationship between pixel data and power draw.
* **Relationship between elements:** The flowchart presents a logical progression from data collection and noise filtering to analysis (template building) and finally reconstruction. The link between the two procedures suggests that intelligence gathered passively can lower the cost or increase the accuracy of a subsequent active attack.
* **Notable implications:** The existence of such a procedure highlights a critical vulnerability in hardware design. The fact that power consumption correlates predictably with processed pixel values means that **data-dependent power leakage** can be exploited to exfiltrate sensitive visual information, even without direct access to the image data stream. The "image reconstruction algorithm" is the final, crucial step that translates the side-channel signal into a meaningful visual output, turning abstract power measurements into a stolen image.