## Flow Diagram: Image Recovery Procedures
### Overview
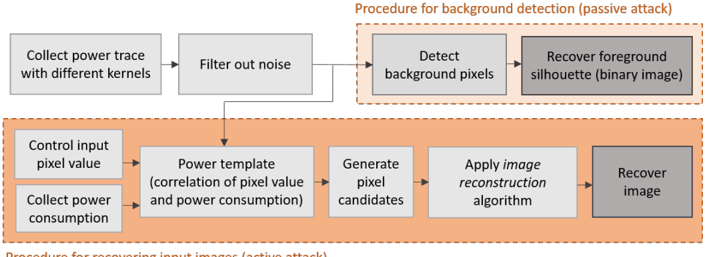
The image presents two flow diagrams outlining procedures for image recovery using power analysis. The first procedure focuses on background detection (passive attack), while the second details the process for recovering input images (active attack). Both diagrams use rectangular boxes to represent steps, with arrows indicating the flow of operations.
### Components/Axes
* **Top Section:** Procedure for background detection (passive attack) - enclosed in a dashed orange border.
* **Bottom Section:** Procedure for recovering input images (active attack) - enclosed in a dashed orange border.
* **Boxes:** Represent individual steps in the procedures.
* **Arrows:** Indicate the flow and sequence of steps.
* **Box Fill Color:** Light gray boxes represent intermediate steps. Dark gray boxes represent the final output.
### Detailed Analysis or ### Content Details
**Procedure for background detection (passive attack):**
1. **Collect power trace with different kernels:** (Light gray box) - Initial step.
2. **Filter out noise:** (Light gray box) - Second step, receives input from the first step.
3. **Detect background pixels:** (Light gray box) - Third step, receives input from the second step.
4. **Recover foreground silhouette (binary image):** (Dark gray box) - Final step, receives input from the third step.
**Procedure for recovering input images (active attack):**
1. **Control input pixel value:** (Light gray box) - Initial step.
2. **Collect power consumption:** (Light gray box) - Initial step.
3. **Power template (correlation of pixel value and power consumption):** (Light gray box) - Third step, receives input from the first and second steps.
4. **Generate pixel candidates:** (Light gray box) - Fourth step, receives input from the third step.
5. **Apply image reconstruction algorithm:** (Light gray box) - Fifth step, receives input from the fourth step.
6. **Recover image:** (Dark gray box) - Final step, receives input from the fifth step.
### Key Observations
* The passive attack focuses on detecting the background to isolate the foreground silhouette.
* The active attack involves manipulating input pixel values and analyzing power consumption to reconstruct the entire image.
* Both procedures culminate in recovering an image or a silhouette.
### Interpretation
The diagrams illustrate two distinct approaches to image recovery using power analysis. The passive attack leverages background detection, while the active attack manipulates input values and analyzes power consumption. The choice of method likely depends on the specific attack scenario and available resources. The use of power analysis suggests a side-channel attack, where information is gleaned from the power consumption of a device during image processing.