## Flowchart: Image Reconstruction and Background Detection Procedures
### Overview
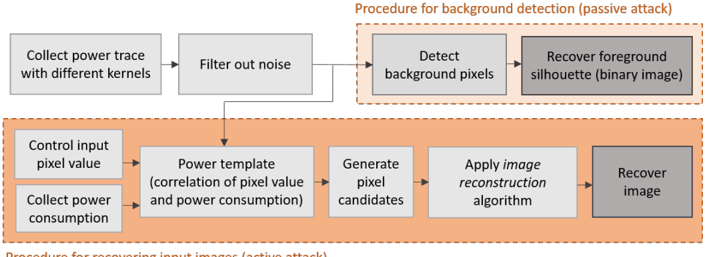
The image depicts a two-part technical workflow for image processing attacks. The top section outlines a **passive attack** for background detection, while the bottom section details an **active attack** for recovering input images. Both procedures involve sequential steps with dependencies, represented by directional arrows.
### Components/Axes
- **Passive Attack Section (Top)**:
- **Steps**:
1. "Collect power trace with different kernels"
2. "Filter out noise"
3. "Detect background pixels"
4. "Recover foreground silhouette (binary image)"
- **Visual Elements**:
- Gray rectangular boxes with black text.
- Black arrows connecting steps.
- Orange dashed line separating the passive attack section from the active attack section.
- **Active Attack Section (Bottom)**:
- **Steps**:
1. "Control input pixel value"
2. "Collect power consumption"
3. "Power template (correlation of pixel value and power consumption)"
4. "Generate pixel candidates"
5. "Apply image reconstruction algorithm"
6. "Recover image"
- **Visual Elements**:
- Gray rectangular boxes with black text.
- Black arrows connecting steps.
- Orange dashed line separating the active attack section from the passive attack section.
### Detailed Analysis
- **Passive Attack Workflow**:
1. **Power Trace Collection**: Initial step involves gathering power consumption data using different computational kernels.
2. **Noise Filtering**: Post-processing to isolate relevant signals from the collected power traces.
3. **Background Pixel Detection**: Identifies pixels associated with the background, likely using statistical or machine learning methods.
4. **Foreground Silhouette Recovery**: Outputs a binary image highlighting the foreground object.
- **Active Attack Workflow**:
1. **Input Pixel Control**: Manipulates pixel values of the input image.
2. **Power Consumption Collection**: Measures power usage during image processing.
3. **Power Template Correlation**: Establishes a relationship between pixel values and power consumption patterns.
4. **Pixel Candidate Generation**: Identifies potential pixel values based on power correlations.
5. **Image Reconstruction**: Applies algorithms (e.g., optimization or iterative methods) to reconstruct the original image.
6. **Image Recovery**: Final output of the reconstructed image.
### Key Observations
- **Dual-Purpose Design**: The flowchart contrasts passive (observational) and active (interventional) attack methodologies.
- **Binary Output**: The passive attack explicitly produces a binary silhouette, suggesting a focus on edge detection or object isolation.
- **Power-Side Channel Exploitation**: Both procedures rely on power consumption data, indicating a focus on side-channel attacks (e.g., power analysis).
- **Sequential Dependency**: Each step in both workflows is strictly ordered, with no branching or parallel processing indicated.
### Interpretation
This flowchart illustrates a framework for exploiting power consumption patterns in computational systems to extract or reconstruct images. The **passive attack** leverages indirect measurements (power traces) to infer background/foreground information, while the **active attack** manipulates inputs to directly recover images. The use of "power templates" suggests a machine learning or statistical approach to model relationships between pixel values and energy usage.
The separation of passive and active attacks implies two distinct threat models: one for eavesdropping on system behavior and another for actively probing systems to reverse-engineer data. The emphasis on binary silhouettes and pixel candidate generation highlights the challenges of reconstructing high-fidelity images from noisy power data.
No numerical data or trends are present, as the image focuses on procedural logic rather than quantitative analysis.