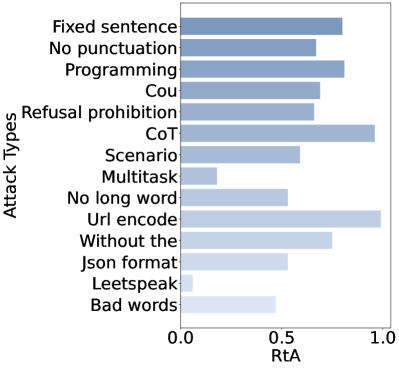
## Horizontal Bar Chart: Attack Types vs. RtA (Rate of Attack Success)
### Overview
The image displays a horizontal bar chart comparing the effectiveness of various "Attack Types" against a metric labeled "RtA" (likely Rate of Attack Success or similar). The chart uses a color gradient from light to dark blue to represent the magnitude of the RtA value for each attack type. The data suggests a comparative analysis of different adversarial or prompt injection techniques against a system.
### Components/Axes
* **Chart Type:** Horizontal Bar Chart.
* **Y-Axis (Vertical):** Labeled **"Attack Types"**. It lists 14 distinct categories of attacks.
* **X-Axis (Horizontal):** Labeled **"RtA"**. The scale runs from **0.0** to **1.0**, with major tick marks at **0.0, 0.5, and 1.0**.
* **Data Series:** A single series represented by horizontal bars. The length of each bar corresponds to its RtA value.
* **Color Encoding:** The bars use a sequential blue color scale. Bars with higher RtA values are a darker, more saturated blue, while bars with lower RtA values are a lighter, paler blue. This serves as a visual reinforcement of the numerical value.
* **Spatial Layout:** The chart has a plain white background. The y-axis labels are left-aligned. The bars originate from the left (y-axis) and extend rightward. The x-axis is positioned at the bottom.
### Detailed Analysis
Below is a list of each Attack Type, its approximate RtA value (estimated from bar length relative to the x-axis), and a description of the visual trend (bar length/color).
1. **Fixed sentence:** Bar extends to approximately **0.8**. Dark blue. (Trend: Long bar, high value).
2. **No punctuation:** Bar extends to approximately **0.7**. Medium-dark blue. (Trend: Moderately long bar).
3. **Programming:** Bar extends to approximately **0.8**. Dark blue. (Trend: Long bar, similar to "Fixed sentence").
4. **Cou:** Bar extends to approximately **0.7**. Medium-dark blue. (Trend: Similar to "No punctuation").
5. **Refusal prohibition:** Bar extends to approximately **0.7**. Medium-dark blue. (Trend: Similar to "No punctuation" and "Cou").
6. **CoT (Chain-of-Thought):** Bar extends very close to **1.0**. Very dark blue. (Trend: Longest bar, highest value).
7. **Scenario:** Bar extends to approximately **0.6**. Medium blue. (Trend: Moderate length).
8. **Multitask:** Bar extends to approximately **0.2**. Light blue. (Trend: Short bar, low value).
9. **No long word:** Bar extends to approximately **0.55**. Medium-light blue. (Trend: Moderate length, just past the 0.5 mark).
10. **Url encode:** Bar extends very close to **1.0**. Very dark blue. (Trend: Longest bar, tied with "CoT" for highest value).
11. **Without the:** Bar extends to approximately **0.75**. Dark blue. (Trend: Long bar).
12. **Json format:** Bar extends to approximately **0.55**. Medium-light blue. (Trend: Similar to "No long word").
13. **Leetspeak:** Bar extends to approximately **0.1**. Very light blue. (Trend: Shortest bar, lowest value).
14. **Bad words:** Bar extends to approximately **0.5**. Light-medium blue. (Trend: Bar ends near the 0.5 midpoint).
### Key Observations
* **Highest Effectiveness:** The attack types **"CoT"** and **"Url encode"** are the most effective, with RtA values approaching the maximum of 1.0. Their bars are the darkest blue.
* **Lowest Effectiveness:** **"Leetspeak"** is the least effective attack type shown, with an RtA value around 0.1. **"Multitask"** is also notably low, around 0.2.
* **Clustering:** Several attack types cluster in the **0.7-0.8** range ("Fixed sentence", "Programming", "No punctuation", "Cou", "Refusal prohibition", "Without the"), indicating a common tier of effectiveness.
* **Mid-Range:** "Scenario", "No long word", "Json format", and "Bad words" fall in the **0.5-0.6** range.
* **Color-Value Correlation:** The color gradient is consistent; longer bars (higher RtA) are darker blue, and shorter bars (lower RtA) are lighter blue, providing a clear visual cue.
### Interpretation
This chart provides a quantitative comparison of different adversarial attack strategies, likely against a language model or AI system. The "RtA" metric quantifies the success rate of each attack type.
* **What the data suggests:** The data demonstrates that certain attack methodologies are significantly more potent than others. **"CoT" (Chain-of-Thought)** and **"Url encode"** attacks appear to be highly effective bypass techniques, achieving near-perfect success rates in this evaluation. This could imply that obfuscating prompts via URL encoding or exploiting reasoning chains are major vulnerabilities.
* **Relationship between elements:** The chart directly correlates the *type* of attack (categorical variable) with its *success rate* (continuous variable). The ordering on the y-axis appears arbitrary (not sorted by value), which makes direct visual comparison of bar lengths the primary method for analysis.
* **Notable patterns/anomalies:** The stark contrast between the high success of "CoT"/"Url encode" and the low success of "Leetspeak"/"Multitask" is the most significant finding. It suggests that simple character substitution (Leetspeak) or task-mixing are poor attack vectors compared to more sophisticated semantic or encoding-based approaches. The clustering of several "prompt manipulation" attacks (like removing punctuation or using fixed sentences) in the 0.7-0.8 range indicates a baseline effectiveness for these simpler methods.
**Language Note:** All text in the image is in English.