## Horizontal Bar Chart: Attack Types vs. RtA Score
### Overview
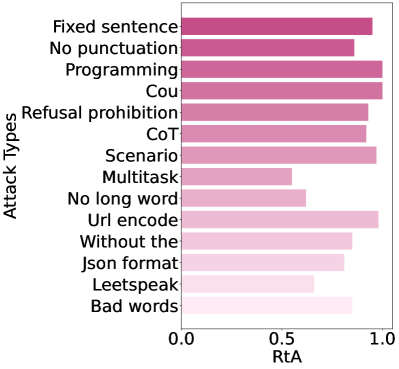
The image displays a horizontal bar chart comparing various "Attack Types" on the y-axis against a metric labeled "RtA" on the x-axis. The chart uses a color gradient for the bars, transitioning from a dark mauve/pink at the top to a very light pink at the bottom. The purpose appears to be to quantify and compare the effectiveness or prevalence (indicated by the RtA score) of different adversarial or prompt injection attack methods.
### Components/Axes
* **Chart Type:** Horizontal Bar Chart.
* **Y-Axis (Vertical):** Labeled **"Attack Types"**. It lists 14 distinct categories of attacks.
* **X-Axis (Horizontal):** Labeled **"RtA"**. The scale runs from **0.0** to **1.0**, with a major tick mark at **0.5**.
* **Legend:** There is no explicit legend. The bar color varies along a gradient from dark (top) to light (bottom), but this gradient is not mapped to a specific variable in the chart. The color change appears to be a stylistic choice for visual separation rather than encoding additional data.
* **Spatial Layout:** The y-axis labels are left-aligned. The bars extend rightward from the y-axis. The x-axis label and numerical markers are centered below the axis line.
### Detailed Analysis
The following table lists each attack type in the order it appears from top to bottom on the y-axis, along with an approximate RtA value estimated from the bar length relative to the x-axis scale. **Note:** Values are visual approximations with inherent uncertainty.
| Attack Type (Y-Axis Label) | Approximate RtA Value | Bar Color (Gradient) |
| :--- | :--- | :--- |
| Fixed sentence | ~0.95 | Dark Mauve |
| No punctuation | ~0.90 | Dark Mauve |
| Programming | ~0.98 | Dark Mauve |
| Cou | ~0.98 | Dark Mauve |
| Refusal prohibition | ~0.92 | Medium-Dark Pink |
| CoT | ~0.88 | Medium-Dark Pink |
| Scenario | ~0.96 | Medium Pink |
| Multitask | ~0.60 | Medium Pink |
| No long word | ~0.70 | Medium-Light Pink |
| Url encode | ~0.96 | Light Pink |
| Without the | ~0.85 | Light Pink |
| Json format | ~0.82 | Very Light Pink |
| Leetspeak | ~0.68 | Very Light Pink |
| Bad words | ~0.85 | Very Light Pink |
**Trend Verification:** The data does not follow a strict monotonic trend from top to bottom. The highest values (near 1.0) are clustered at the top (Fixed sentence, Programming, Cou) and one in the middle (Url encode). The lowest values are for "Multitask" (~0.60) and "Leetspeak" (~0.68), which are in the lower half of the chart. The color gradient does not correlate perfectly with the RtA value (e.g., the light pink "Url encode" bar is among the longest).
### Key Observations
1. **High-Effectiveness Cluster:** Several attack types achieve very high RtA scores (≥0.95): "Programming", "Cou", "Fixed sentence", "Scenario", and "Url encode".
2. **Significant Outlier:** The "Multitask" attack type has a notably lower RtA score (~0.60) compared to all others, suggesting it is substantially less effective or prevalent according to this metric.
3. **Mid-Range Performance:** "No long word" (~0.70) and "Leetspeak" (~0.68) form a lower-performance group, though still above 0.5.
4. **Label Ambiguity:** The label "Cou" is an abbreviation or potential typo. Without context, its exact meaning is unclear (it could stand for "Code obfuscation," "Concatenation," or another term).
5. **Metric Definition:** The metric "RtA" is not defined within the image. Common interpretations in security/AI contexts could be "Rate to Attack," "Resistance to Attack," or "Risk of Attack." Given the high values for known attack methods, it likely measures attack success rate or prevalence, where a higher score indicates a more effective or common attack.
### Interpretation
This chart provides a comparative analysis of different adversarial attack strategies, likely against a language model or similar AI system. The RtA score serves as a quantitative measure of each attack's potency.
* **What the data suggests:** The data indicates that simple, structural attacks ("Fixed sentence", "No punctuation") and encoding-based attacks ("Url encode") are highly effective, rivaling or exceeding more complex methodological attacks like "CoT" (Chain-of-Thought) manipulation. The very high score for "Programming" suggests that using code-like instructions is a particularly potent attack vector.
* **Relationship between elements:** The chart directly correlates categorical attack methods with a continuous performance metric. The lack of a clear trend based on position or color implies the ordering of attack types on the y-axis is not based on the RtA score (e.g., it is not sorted by value).
* **Notable anomalies:** The "Multitask" attack's low score is the most striking anomaly. This could imply that dividing the model's attention across multiple tasks is an ineffective attack strategy, or that defenses against such attempts are particularly robust. The high performance of "Url encode" is also notable, highlighting the vulnerability of systems to obfuscated input.
* **Underlying significance:** For a security researcher or AI engineer, this chart is a prioritization tool. It highlights which attack surfaces (e.g., input formatting, code injection, obfuscation) require the most urgent defensive measures. The high effectiveness of seemingly simple attacks ("Fixed sentence") underscores that vulnerabilities are not solely the domain of complex, sophisticated exploits.