## Diagram: Cryptographic Problem Reduction
### Overview
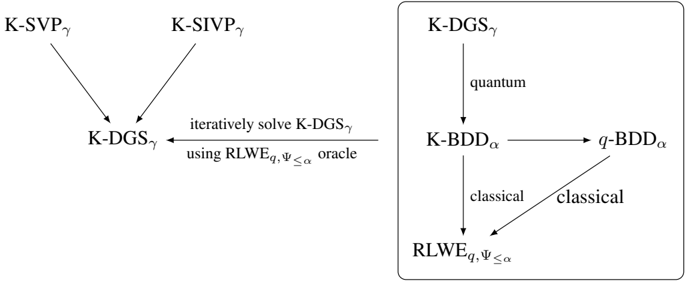
The image is a diagram illustrating the relationships and reductions between different cryptographic problems. It shows how certain problems can be reduced to others, either through quantum or classical algorithms, and iterative solving methods. The diagram is divided into two main sections: one showing the reduction to K-DGSγ from K-SVPγ and K-SIVPγ, and another enclosed in a box, detailing the reductions involving K-DGSγ, K-BDDα, q-BDDα, and RLWEq, Ψ ≤ α.
### Components/Axes
* **Nodes:** The nodes represent cryptographic problems.
* K-SVPγ
* K-SIVPγ
* K-DGSγ
* K-BDDα
* q-BDDα
* RLWEq, Ψ ≤ α
* **Edges:** The edges represent reductions between the problems.
* "iteratively solve K-DGSγ using RLWEq, Ψ ≤ α oracle"
* "quantum"
* "classical"
### Detailed Analysis
* **Left Side:**
* K-SVPγ (located at the top-left) has a directed edge pointing to K-DGSγ (located in the center).
* K-SIVPγ (located at the top-right) has a directed edge pointing to K-DGSγ.
* An arrow points from the right of "iteratively solve K-DGSγ using RLWEq, Ψ ≤ α oracle" back to K-DGSγ, indicating an iterative process.
* **Right Side (Enclosed in a box):**
* K-DGSγ (located at the top) has a directed edge labeled "quantum" pointing to K-BDDα (located in the middle-left).
* K-BDDα has a directed edge pointing to q-BDDα (located in the middle-right).
* K-BDDα has a directed edge labeled "classical" pointing to RLWEq, Ψ ≤ α (located at the bottom).
* q-BDDα has a directed edge labeled "classical" pointing to RLWEq, Ψ ≤ α.
### Key Observations
* K-DGSγ is a central problem, being reduced to from K-SVPγ and K-SIVPγ, and also being the starting point for reductions to other problems on the right side.
* The right side of the diagram shows a mix of quantum and classical reductions.
* The iterative solving of K-DGSγ using RLWEq, Ψ ≤ α suggests a potential vulnerability or a method to solve K-DGSγ.
### Interpretation
The diagram illustrates the relationships between various cryptographic problems and how they can be reduced to one another. The reductions can be achieved through quantum or classical algorithms. The iterative solving of K-DGSγ using RLWEq, Ψ ≤ α as an oracle suggests a potential attack vector or a method for solving K-DGSγ. The diagram highlights the importance of understanding the relationships between these problems to assess the security of cryptographic systems.