## Diagram: Cryptographic Reduction Chain
### Overview
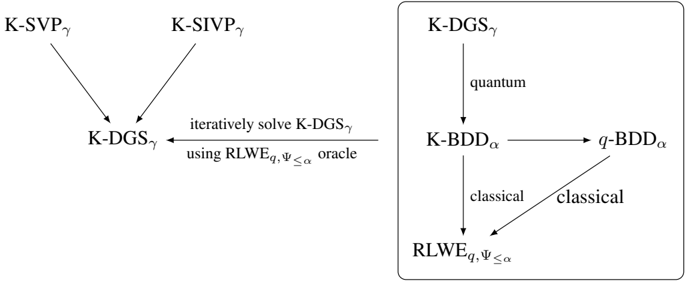
The image displays a technical diagram illustrating relationships and reduction pathways between various computational problems, likely in the domain of lattice-based cryptography. It consists of two main sections: a left-side reduction graph and a right-side process flow contained within a rectangular box, connected by a labeled arrow indicating an iterative solving method.
### Components/Axes
The diagram is composed of text labels (problem names) and directed arrows indicating relationships or reductions. There are no traditional chart axes, legends, or numerical data points. The components are purely conceptual entities.
**Left Section:**
* **Top-Left:** `K-SVPγ`
* **Top-Right:** `K-SIVPγ`
* **Bottom-Center:** `K-DGSγ`
* **Arrows:** Two arrows point downward from `K-SVPγ` and `K-SIVPγ` to `K-DGSγ`.
**Connecting Arrow:**
* A horizontal arrow points from the right section's box back to the left section's `K-DGSγ`.
* **Label above arrow:** `iteratively solve K-DGSγ`
* **Label below arrow:** `using RLWEq,Ψ≤α oracle`
**Right Section (within a rectangular box):**
* **Top:** `K-DGSγ`
* **Middle-Left:** `K-BDDα`
* **Middle-Right:** `q-BDDα`
* **Bottom:** `RLWEq,Ψ≤α`
* **Arrows & Labels:**
* A vertical arrow points from `K-DGSγ` down to `K-BDDα`, labeled `quantum`.
* A horizontal arrow points from `K-BDDα` to `q-BDDα`.
* A diagonal arrow points from `K-BDDα` down to `RLWEq,Ψ≤α`, labeled `classical`.
* A diagonal arrow points from `q-BDDα` down to `RLWEq,Ψ≤α`, labeled `classical`.
### Detailed Analysis
The diagram maps a chain of problem reductions:
1. **Left Side:** The problems `K-SVPγ` (K-Shortest Vector Problem with parameter γ) and `K-SIVPγ` (K-Shortest Independent Vectors Problem with parameter γ) both reduce to `K-DGSγ` (K-Distributed Gaussian Sampling with parameter γ).
2. **Right Side (Boxed Process):** This section details a specific algorithmic relationship.
* `K-DGSγ` is connected to `K-BDDα` (K-Bounded Distance Decoding with parameter α) via a `quantum` reduction or step.
* `K-BDDα` is connected to `q-BDDα` (likely a quantized or variant BDD problem).
* Both `K-BDDα` and `q-BDDα` have `classical` reductions to `RLWEq,Ψ≤α` (Ring Learning With Errors with modulus q and error distribution Ψ≤α).
3. **Overall Flow:** The entire right-side box is connected back to the left-side `K-DGSγ` via an arrow indicating that `K-DGSγ` can be solved iteratively by using an oracle for `RLWEq,Ψ≤α`.
### Key Observations
* **Problem Hierarchy:** The diagram establishes a hierarchy where foundational lattice problems (`SVP`, `SIVP`) lead to sampling problems (`DGS`), which are then connected to decoding (`BDD`) and finally to the foundational `RLWE` problem.
* **Reduction Types:** The diagram explicitly distinguishes between `quantum` and `classical` reductions or algorithmic steps within the right-side box.
* **Cyclical Relationship:** There is a conceptual cycle: `K-DGSγ` (left) is reduced to `RLWEq,Ψ≤α` (right, bottom) via intermediate steps, and `RLWEq,Ψ≤α` is then used as an oracle to solve `K-DGSγ` iteratively.
* **Parameter Notation:** All problem labels include Greek letter parameters (γ, α) and, for RLWE, distribution (Ψ≤α) and modulus (q) specifications, indicating precise problem instances.
### Interpretation
This diagram is a **reduction graph** used in theoretical cryptography and complexity theory. It visually argues for the relative hardness and interconnectedness of specific lattice-based problems.
* **What it demonstrates:** It shows that solving the `K-Distributed Gaussian Sampling (K-DGSγ)` problem is central, as it is implied by both `SVP` and `SIVP` (left side). Furthermore, it demonstrates that `K-DGSγ` can be tackled by leveraging an oracle for the `Ring Learning With Errors (RLWE)` problem, but this requires a multi-step process involving both quantum (`K-DGSγ` to `K-BDDα`) and classical (`BDD` variants to `RLWE`) reductions.
* **Relationships:** The arrows represent **polynomial-time reductions**. If you can solve the problem at the arrow's head efficiently, you can also solve the problem at the arrow's tail. The diagram suggests that `RLWE` is a foundational "hard" problem, as multiple paths lead to it, and it is used as an oracle to solve other problems.
* **Significance:** In cryptography, such reductions are used to prove security. If a scheme is based on the hardness of `RLWE`, and an attack on the scheme would imply an efficient algorithm for `RLWE` (via these reduction chains), then the scheme's security is tied to the presumed hardness of `RLWE`. The inclusion of both quantum and classical steps is particularly relevant for assessing security against both types of adversaries. The iterative solving loop highlights a potential algorithmic strategy or proof technique.