## Diagram: Cryptographic Process Flowchart
### Overview
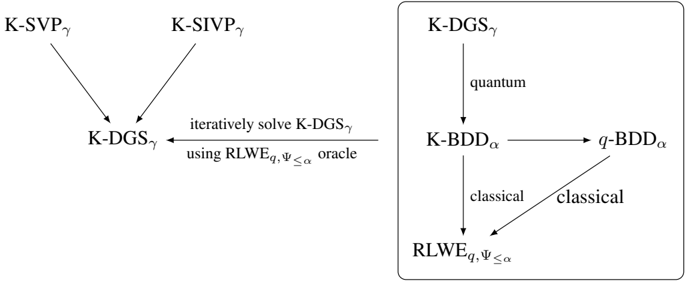
The image depicts a two-part cryptographic process diagram. The left section shows the iterative solving of **K-DGSγ** using an RLWE oracle, while the right section illustrates the quantum and classical derivation of **RLWEq,Ψ≤α** from **K-DGSγ**. Arrows indicate dependencies, transformations, and feedback loops.
### Components/Axes
#### Left Diagram (K-DGSγ Solving Process):
- **Nodes**:
- **K-SVPγ** (top-left)
- **K-SIVPγ** (top-right)
- **K-DGSγ** (center)
- **Arrows**:
- **K-SVPγ** → **K-DGSγ**
- **K-SIVPγ** → **K-DGSγ**
- **K-DGSγ** → "iteratively solve K-DGSγ using RLWEq,Ψ≤α oracle"
#### Right Diagram (RLWE Derivation):
- **Nodes**:
- **K-DGSγ** (top)
- **K-BDDα** (middle-left)
- **q-BDDα** (middle-right)
- **RLWEq,Ψ≤α** (bottom)
- **Arrows**:
- **K-DGSγ** → **K-BDDα** (labeled "quantum")
- **K-BDDα** → **q-BDDα** (labeled "classical")
- **q-BDDα** → **RLWEq,Ψ≤α** (labeled "classical")
- **RLWEq,Ψ≤α** → **K-DGSγ** (feedback loop, labeled "classical")
### Detailed Analysis
1. **Left Diagram**:
- **K-SVPγ** and **K-SIVPγ** are prerequisites for solving **K-DGSγ**.
- **K-DGSγ** is iteratively refined using an RLWE oracle parameterized by **q** and **Ψ≤α**.
2. **Right Diagram**:
- **K-DGSγ** is transformed into **K-BDDα** via a quantum process.
- **K-BDDα** is classically converted to **q-BDDα**, which is further classically processed into **RLWEq,Ψ≤α**.
- **RLWEq,Ψ≤α** feeds back into **K-DGSγ**, creating a closed-loop system.
### Key Observations
- **Quantum-Classical Hybrid**: The right diagram explicitly separates quantum and classical steps, suggesting a hybrid cryptographic framework.
- **Iterative Refinement**: The left diagram emphasizes iterative solving of **K-DGSγ**, implying optimization or error correction.
- **Feedback Loop**: The circular dependency between **RLWEq,Ψ≤α** and **K-DGSγ** indicates a self-reinforcing or adaptive system.
### Interpretation
This diagram outlines a cryptographic protocol where **K-DGSγ** (likely a key derivation or encryption scheme) is solved using RLWE (Ring Learning With Errors) parameters. The left side focuses on the mathematical foundation (iterative solving with an oracle), while the right side details the practical implementation:
- **Quantum Step**: **K-DGSγ** → **K-BDDα** (possibly a quantum-resistant transformation).
- **Classical Steps**: **K-BDDα** → **q-BDDα** → **RLWEq,Ψ≤α** (post-processing to derive RLWE parameters).
- **Feedback**: **RLWEq,Ψ≤α** refines **K-DGSγ**, suggesting adaptive security or parameter optimization.
The use of RLWE (a lattice-based cryptographic primitive) and the hybrid quantum-classical workflow align with post-quantum cryptography research, where RLWE is a candidate for quantum-resistant algorithms. The feedback loop implies that the system dynamically adjusts parameters (e.g., **q**, **Ψ≤α**) to maintain security against evolving threats.
### Uncertainties
- The exact mathematical definitions of **K-SVPγ**, **K-SIVPγ**, and **K-DGSγ** are not provided, limiting precise interpretation of their roles.
- The relationship between **q-BDDα** and **RLWEq,Ψ≤α** is abstract; further context on **BDDα** (Bounded Distance Decoding) is needed to clarify its role in RLWE derivation.