## Diagram: Covert Sending Classification
### Overview
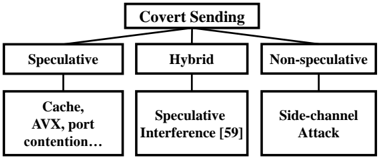
The image is a hierarchical diagram illustrating the classification of "Covert Sending" techniques. It branches into three main categories: Speculative, Hybrid, and Non-speculative. Each of these categories further branches into specific methods or attacks.
### Components/Axes
* **Top-Level Node:** "Covert Sending" - This is the root of the classification.
* **Second-Level Nodes:**
* "Speculative" - A category of covert sending.
* "Hybrid" - A category of covert sending.
* "Non-speculative" - A category of covert sending.
* **Third-Level Nodes:**
* Under "Speculative": "Cache, AVX, port contention..."
* Under "Hybrid": "Speculative Interference [59]"
* Under "Non-speculative": "Side-channel Attack"
### Detailed Analysis
The diagram shows a top-down classification.
* **Covert Sending** is at the top.
* It branches into three categories: Speculative, Hybrid, and Non-speculative.
* Each of these categories has a specific example or method associated with it:
* Speculative includes "Cache, AVX, port contention..."
* Hybrid includes "Speculative Interference [59]"
* Non-speculative includes "Side-channel Attack"
### Key Observations
* The diagram provides a clear hierarchical structure for understanding different types of covert sending techniques.
* The "[59]" notation next to "Speculative Interference" likely refers to a citation or reference.
* The "..." after "Cache, AVX, port contention..." indicates that the list is not exhaustive.
### Interpretation
The diagram illustrates a taxonomy of covert sending methods. It categorizes these methods based on whether they are speculative, hybrid, or non-speculative. The specific examples provided under each category give insight into the types of techniques that fall under each classification. The diagram is useful for understanding the different approaches to covert sending and how they relate to each other.