\n
## Diagram: Covert Sending Taxonomy
### Overview
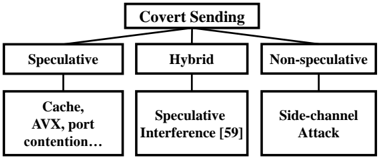
The image presents a hierarchical diagram outlining a taxonomy of "Covert Sending" techniques. It categorizes these techniques into three main branches: Speculative, Hybrid, and Non-speculative. Each of these branches further subdivides into more specific methods. The diagram is structured as a tree, with "Covert Sending" at the root and the specific techniques as leaf nodes.
### Components/Axes
The diagram consists of rectangular boxes connected by lines representing hierarchical relationships. The boxes contain text labels describing the different categories and techniques. There are no axes or scales present, as it is a categorical diagram.
### Detailed Analysis or Content Details
The diagram can be broken down as follows:
* **Root Node:** "Covert Sending" - positioned at the top-center of the diagram.
* **First Level Branches:**
* "Speculative" - positioned to the left of the root node.
* "Hybrid" - positioned directly below the root node.
* "Non-speculative" - positioned to the right of the root node.
* **Second Level Branches (under "Speculative"):**
* "Cache, AVX, port contention..." - positioned below "Speculative". The text is truncated, indicating there are likely more elements not fully visible.
* **Second Level Branches (under "Hybrid"):**
* "Speculative Interference [59]" - positioned below "Hybrid". The "[59]" likely refers to a citation or reference number.
* **Second Level Branches (under "Non-speculative"):**
* "Side-channel Attack" - positioned below "Non-speculative".
### Key Observations
The diagram illustrates a classification of covert sending techniques based on whether they rely on speculative execution, a combination of techniques (hybrid), or do not involve speculative execution (non-speculative). The "Speculative" branch appears to have more detailed sub-categories, but the text is incomplete. The inclusion of a citation "[59]" suggests that "Speculative Interference" is a well-defined technique with existing research.
### Interpretation
This diagram provides a high-level overview of the different approaches used in covert sending attacks. Covert sending refers to techniques where an attacker can transmit information through a system without using traditional communication channels. The categorization helps to understand the underlying mechanisms of these attacks.
* **Speculative techniques** likely exploit vulnerabilities in modern processors that rely on speculative execution to improve performance. These attacks manipulate the speculative execution process to leak information.
* **Hybrid techniques** combine speculative and non-speculative methods, potentially offering increased stealth or effectiveness.
* **Non-speculative techniques** rely on side channels, such as timing variations or power consumption, to transmit information.
The diagram suggests that speculative execution is a significant area of concern in covert sending attacks, as it has a dedicated branch and further sub-categorization. The incomplete text in the "Cache, AVX, port contention..." box indicates that there are multiple ways to exploit speculative execution for covert sending. The diagram is a useful starting point for understanding the landscape of covert sending attacks and the different techniques employed by attackers.