\n
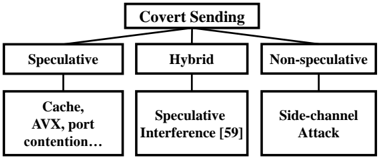
## Diagram: Covert Sending Taxonomy
### Overview
The image is a hierarchical flowchart diagram illustrating a taxonomy of "Covert Sending" techniques. It presents a top-down classification system, breaking down the main concept into three primary categories, each with a specific sub-type or example. The diagram is rendered in a simple, black-and-white schematic style with rectangular boxes connected by lines.
### Components/Axes
The diagram consists of a single hierarchical tree structure with three levels:
1. **Top-Level Node (Root):** A single box labeled "Covert Sending".
2. **Second-Level Nodes (Categories):** Three boxes branching from the root, labeled from left to right:
* "Speculative"
* "Hybrid"
* "Non-speculative"
3. **Third-Level Nodes (Sub-types/Examples):** Three boxes, each connected to one of the second-level nodes:
* Connected to "Speculative": A box containing the text "Cache, AVX, port contention..."
* Connected to "Hybrid": A box containing the text "Speculative Interference [59]"
* Connected to "Non-speculative": A box containing the text "Side-channel Attack"
**Spatial Grounding:** The "Covert Sending" box is centered at the top. The three category boxes ("Speculative", "Hybrid", "Non-speculative") are arranged horizontally in a row directly below it. The three sub-type boxes are arranged in a corresponding horizontal row below their parent categories, creating a clear, aligned three-column structure.
### Detailed Analysis
The diagram defines a classification framework for covert communication or data exfiltration methods, likely in the context of computer security or microarchitectural attacks.
* **Primary Classification:** Covert Sending is divided based on the underlying mechanism or principle:
* **Speculative:** Relies on speculative execution, a common performance optimization in modern CPUs.
* **Hybrid:** A combination approach, explicitly noted as involving "Speculative Interference."
* **Non-speculative:** Does not depend on speculative execution.
* **Specific Techniques/Examples:**
* The **Speculative** category is exemplified by resource contention attacks, specifically mentioning "Cache" (cache-based attacks), "AVX" (Advanced Vector Extensions, a CPU instruction set), and "port contention" (execution port conflicts). The ellipsis ("...") indicates this list is not exhaustive.
* The **Hybrid** category is exemplified by "Speculative Interference," with a citation marker "[59]" indicating this term or concept is referenced from source number 59 in a bibliography.
* The **Non-speculative** category is exemplified by the classic "Side-channel Attack," which exploits indirect information leakage from a system's physical implementation.
### Key Observations
1. **Hierarchical Structure:** The diagram presents a clear, top-down taxonomy, suggesting "Covert Sending" is the overarching concept being categorized.
2. **Citation Presence:** The inclusion of "[59]" in the "Hybrid" branch is a key detail, indicating this diagram is likely extracted from an academic paper or technical report where "Speculative Interference" is a defined or cited term.
3. **Asymmetric Detail:** The "Speculative" branch provides a list of multiple examples (Cache, AVX, port contention), while the "Hybrid" and "Non-speculative" branches each provide a single, named technique.
4. **Terminology:** The use of terms like "AVX," "port contention," and "Side-channel Attack" places this diagram firmly within the domain of hardware security and computer architecture research.
### Interpretation
This diagram serves as a conceptual map for understanding different families of covert channel attacks in computing systems. It organizes them by their core operational principle: whether they exploit speculative execution (a performance feature), a hybrid of speculation and interference, or traditional side-channels that do not involve speculation.
The taxonomy highlights the evolution and diversification of attack vectors. The "Speculative" branch reflects the security challenges introduced by modern CPU optimizations like speculative execution (famously exploited by attacks like Spectre). The "Hybrid" category suggests more complex, novel attacks that combine multiple principles. The "Non-speculative" branch represents the established class of attacks (e.g., timing attacks, power analysis) that remain relevant.
The citation "[59]" is crucial for a technical reader, as it points to the source material where the "Hybrid" category or the specific "Speculative Interference" technique is formally described, allowing for deeper investigation. Overall, the diagram provides a structured lens for analyzing and categorizing security vulnerabilities related to covert data transmission.