## Tree Diagram: Covert Sending
### Overview
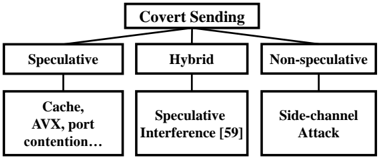
The diagram illustrates the different types of covert sending methods, categorized into speculative, hybrid, and non-speculative. Each category is further divided into specific techniques.
### Components/Axes
- **Covert Sending**: The main category at the top.
- **Speculative**: A sub-category under covert sending.
- **Hybrid**: Another sub-category under covert sending.
- **Non-speculative**: A sub-category under covert sending.
- **Cache, AVX, port contention...**: A technique under speculative.
- **Speculative Interference [59]**: A technique under hybrid.
- **Side-channel Attack**: A technique under non-speculative.
### Detailed Analysis or ### Content Details
- **Speculative**: Techniques include Cache, AVX, and port contention.
- **Hybrid**: Techniques include Speculative Interference.
- **Non-speculative**: Techniques include Side-channel Attack.
### Key Observations
- The diagram shows a clear distinction between speculative and non-speculative methods.
- Speculative methods involve techniques like Cache, AVX, and port contention.
- Hybrid methods involve Speculative Interference.
- Non-speculative methods involve Side-channel Attack.
### Interpretation
The diagram provides a visual representation of different covert sending methods, which are techniques used to send data without being detected. Speculative methods involve techniques like Cache, AVX, and port contention, which can be used to send data by manipulating the cache and AVX instructions. Hybrid methods involve Speculative Interference, which can be used to send data by manipulating the interference between different instructions. Non-speculative methods involve Side-channel Attack, which can be used to send data by manipulating the side-channel information.
The diagram is useful for understanding the different techniques used in covert sending and how they can be used to send data without being detected. It can also be used to identify the strengths and weaknesses of each technique and to develop countermeasures to detect covert sending.