TECHNICAL ASSET FINGERPRINT
4e2f59f648982a9374e221e5
Click to view fullscreen
Press ESC or click to close
FOUND IN PAPERS
EXPERT: gemini-2.0-flash VERSION 1
RUNTIME: nugit/gemini/gemini-2.0-flash
INTEL_VERIFIED
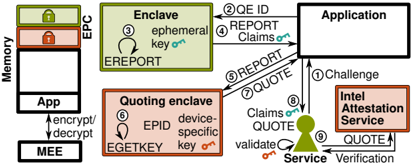
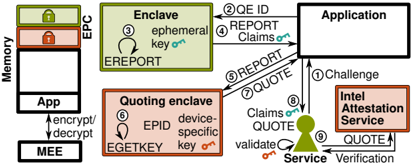
## Attestation Diagram: Enclave Verification Process
### Overview
The image is a diagram illustrating the process of attestation for an enclave, involving components like memory, EPC, enclave, quoting enclave, application, Intel Attestation Service, and a generic service. The diagram outlines the flow of information and cryptographic operations between these components to verify the integrity and authenticity of the enclave.
### Components/Axes
* **Memory:** Represents the system memory, containing the application and the MEE (likely Management Engine Environment).
* **App:** Application running in memory.
* **MEE:** Management Engine Environment.
* **EPC:** Enclave Page Cache, a protected memory region. It has two lock icons, one green on top and one red below.
* **Enclave:** A secure region within memory.
* Label: "Enclave"
* Text: "ephemeral key" with a key icon.
* Process: EREPORT
* **Quoting Enclave:** A specialized enclave responsible for generating quotes.
* Label: "Quoting enclave"
* Text: "EPID device-specific key" with a key icon.
* Process: EGETKEY
* **Application:** The application that needs to verify the enclave.
* Label: "Application"
* **Intel Attestation Service:** A service provided by Intel for attestation.
* Label: "Intel Attestation Service"
* **Service:** A generic service that validates the quote.
* Label: "Service"
* Text: "validate" and "Verification"
### Detailed Analysis or Content Details
The diagram depicts a series of steps, numbered 1 through 9, illustrating the attestation process:
1. **Challenge:** The Application sends a challenge to the Service.
2. **QE ID:** The Enclave sends the QE ID to the Application.
3. **EREPORT:** The Enclave generates a report (EREPORT) using an ephemeral key.
4. **REPORT Claims:** The Enclave sends a REPORT containing claims to the Application.
5. **REPORT QUOTE:** The Application sends a REPORT and requests a QUOTE from the Quoting Enclave.
6. **EGETKEY:** The Quoting Enclave uses EGETKEY to generate a device-specific key and EPID.
7. **QUOTE:** The Quoting Enclave sends a QUOTE to the Application.
8. **Claims QUOTE:** The Application sends Claims and the QUOTE to the Service.
9. **QUOTE:** The Service sends the QUOTE to the Intel Attestation Service for verification. The Intel Attestation Service sends the QUOTE back to the Service.
Additional details:
* The Enclave is colored light green.
* The Quoting Enclave and Intel Attestation Service are colored light red.
* The Service is represented by a green keyhole icon.
* The Application is a white rectangle.
* The Memory block is white with a black outline.
* The EPC has a green lock on top and a red lock below.
* Arrows indicate the direction of data flow.
* The application encrypts/decrypts data to/from the MEE.
### Key Observations
* The diagram highlights the interaction between different components to establish trust in the Enclave.
* The use of cryptographic keys and reports is central to the attestation process.
* The Intel Attestation Service plays a crucial role in verifying the QUOTE.
* The process involves multiple steps to ensure the integrity and authenticity of the Enclave.
### Interpretation
The diagram illustrates a typical remote attestation process for enclaves. The application, seeking to trust the enclave, initiates a challenge. The enclave, through a series of cryptographic operations and interactions with the quoting enclave and the Intel Attestation Service, provides evidence of its integrity and authenticity. The service validates this evidence, allowing the application to establish trust in the enclave. The use of ephemeral keys and device-specific keys adds layers of security to the process. The diagram demonstrates the complexity involved in establishing trust in secure enclaves, highlighting the importance of secure key management and robust attestation mechanisms.
DECODING INTELLIGENCE...
EXPERT: gemma-3-27b-it-free VERSION 1
RUNTIME: google-free/gemma-3-27b-it
INTEL_VERIFIED
\n
## Diagram: Intel Attestation Service Flow
### Overview
This diagram illustrates the flow of data and interactions between an Application, an Enclave, a Quoting Enclave, and the Intel Attestation Service, utilizing Intel's Enhanced Privacy Protection (EPC) and related technologies. The diagram depicts a secure attestation process, where the application verifies the integrity of the enclave before trusting its computations. The diagram uses numbered arrows to indicate the sequence of operations.
### Components/Axes
The diagram features the following components:
* **Memory:** Labelled on the left side, indicating the memory space.
* **App:** Represents the main Application.
* **Enclave:** A secure area within memory, utilizing EPC.
* **Quoting Enclave:** Another secure area within memory, responsible for generating quotes.
* **Intel Attestation Service:** A remote service for verifying the integrity of the enclaves.
* **MEE:** Marked as encrypt/decrypt.
* **EPC:** Marked as a memory region.
The diagram also includes the following labels and text embedded within components:
* **ephemeral key on:** Inside the Enclave.
* **EREPORT:** Inside the Enclave.
* **EPID:** Inside the Quoting Enclave.
* **EGETKEY:** Inside the Quoting Enclave.
* **device-specific key on:** Inside the Quoting Enclave.
* **Challenge:** From Application to Intel Attestation Service.
* **REPORT:** Exchanged between Application and Quoting Enclave.
* **QUOTE:** Exchanged between Quoting Enclave and Intel Attestation Service.
* **Claims on:** Labels on arrows indicating data claims.
* **validate on:** Label on arrow indicating validation.
* **Service Verification:** Label on the bottom right.
### Detailed Analysis / Content Details
The diagram shows a numbered sequence of operations:
1. **Challenge:** The Application sends a challenge to the Intel Attestation Service.
2. **QE ID REPORT:** The Application requests the Enclave's ID and a REPORT.
3. **ephemeral key on:** The Enclave generates an ephemeral key.
4. **Claims on REPORT:** The Application receives the REPORT and associated claims.
5. **REPORT:** The Application sends the REPORT to the Quoting Enclave.
6. **EPID EGETKEY device-specific key on:** The Quoting Enclave uses EPID and EGETKEY to generate a device-specific key.
7. **QUOTE:** The Quoting Enclave generates a QUOTE.
8. **Claims on QUOTE:** The Quoting Enclave sends the QUOTE and associated claims to the Intel Attestation Service.
9. **QUOTE:** The Intel Attestation Service receives the QUOTE.
10. **Service Verification:** The Intel Attestation Service performs service verification.
The arrows indicate the direction of data flow. The "encrypt/decrypt" label on the MEE suggests that the MEE is responsible for encrypting and decrypting data between the Application and the Enclave. The "EPC" label indicates that the Enclave resides within the EPC memory region.
### Key Observations
The diagram highlights a multi-step attestation process. The Quoting Enclave plays a crucial role in generating a QUOTE, which is then verified by the Intel Attestation Service. The use of EPID and EGETKEY suggests a hardware-based root of trust. The flow emphasizes the secure exchange of information and the validation of the enclave's integrity.
### Interpretation
This diagram demonstrates a secure attestation process designed to establish trust in a remote computation environment. The Intel Attestation Service acts as a trusted third party, verifying the integrity of the Enclave before the Application relies on its results. The use of EPC and hardware-based keys (EPID, EGETKEY) enhances the security of the process. The diagram suggests a system where sensitive computations are performed within a secure enclave, and the application can confidently verify that the enclave has not been tampered with. The process is complex, involving multiple steps and components, but it provides a robust mechanism for ensuring the integrity of remote computations. The "Claims on" labels suggest that the reports and quotes contain assertions about the enclave's configuration and state, which are verified by the Attestation Service. The diagram illustrates a critical component of Intel's security architecture, enabling secure remote execution and data protection.
DECODING INTELLIGENCE...
EXPERT: healer-alpha-free VERSION 1
RUNTIME: free/openrouter/healer-alpha
INTEL_VERIFIED
## Technical Diagram: Intel SGX Remote Attestation Flow
### Overview
This image is a technical process diagram illustrating the remote attestation workflow for Intel Software Guard Extensions (SGX). It depicts the interaction between an application running within an enclave, a quoting enclave, a relying party service, and the Intel Attestation Service (IAS). The diagram uses labeled boxes, arrows with numbered steps, and icons to represent cryptographic keys and operations, detailing the sequence of actions required to establish trust in a remote execution environment.
### Components/Elements
The diagram is organized into several key regions and components:
1. **Memory Region (Left Side):**
* **EPC (Enclave Page Cache):** A rectangular box containing a smaller box labeled **"App"**. An arrow labeled **"encrypt/decrypt"** points from the EPC to the **MEE (Memory Encryption Engine)** below it.
* **MEE:** A box at the bottom-left corner.
2. **Core Components (Center & Right):**
* **Enclave:** A large rounded rectangle in the upper-center. It contains:
* Text: **"ephemeral key"** with a key icon.
* Text: **"EREPORT"**.
* **Quoting enclave:** A large rounded rectangle below the Enclave. It contains:
* Text: **"EPID"** and **"device-specific key"** with a key icon.
* Text: **"EGETKEY"**.
* **Application:** A rectangle in the upper-right.
* **Service:** A rectangle in the lower-right, containing a person/user icon.
* **Intel Attestation Service:** A distinct, outlined rectangle on the far right.
3. **Data Flow & Labels:**
Arrows connect the components, each associated with a numbered step and a label describing the data or action:
* **① Challenge:** Arrow from **Service** to **Application**.
* **② REPORT:** Arrow from **Enclave** to **Application**.
* **③ QE ID:** Arrow from **Quoting enclave** to **Application**.
* **④ REPORT, QUOTE:** Arrow from **Application** to **Service**.
* **⑤ Claims, QUOTE:** Arrow from **Service** to **Intel Attestation Service**.
* **⑥ validate:** Arrow from **Intel Attestation Service** back to **Service**.
* **⑦ QUOTE:** Arrow from **Intel Attestation Service** to **Service**.
* **⑧ Verification:** Arrow from **Service** to the user icon within its own box.
* **⑨ EREPORT:** Arrow from **Enclave** to **Quoting enclave**.
* **⑩ EGETKEY:** Arrow from **Quoting enclave** to the **MEE**.
### Detailed Analysis: Step-by-Step Flow
The diagram outlines a 10-step attestation process:
1. **Challenge Initiation:** The relying party (**Service**) sends a cryptographic **Challenge** (①) to the **Application** that needs to be attested.
2. **Report Generation:** The **Application** requests a report from its **Enclave**. The Enclave generates a **REPORT** (②) containing measurements of its code and data, signed with its **ephemeral key**.
3. **Quoting Enclave Identification:** The **Quoting enclave** provides its identity (**QE ID** (③)) to the Application.
4. **Quote Request:** The **Application** forwards the Enclave's **REPORT** along with the **QE ID** to the **Quoting enclave** (via the arrow labeled **REPORT, QUOTE** (④)). The Quoting enclave verifies the REPORT and signs it with its **device-specific key** (obtained via **EGETKEY** (⑩) from the MEE), creating a **QUOTE**.
5. **Attestation Submission:** The **Service** collects **Claims** (e.g., user data) and the **QUOTE** from the Application and submits them to the **Intel Attestation Service** (⑤).
6. **IAS Validation:** The **Intel Attestation Service** **validates** (⑥) the QUOTE by checking the signature against Intel's root of trust and verifying the enclave's measurements against known good values.
7. **Attestation Result:** The IAS sends a **QUOTE** (⑦) response (likely a signed attestation result or token) back to the **Service**.
8. **Final Verification:** The **Service** performs a final **Verification** (⑧) of the IAS response and the claims, deciding whether to trust the remote enclave.
9. **Internal Enclave Communication:** The **Enclave** generates an **EREPORT** (⑨) for the **Quoting enclave**, which is a local attestation report used for intra-platform communication.
10. **Key Retrieval:** The **Quoting enclave** retrieves its **device-specific key** by issuing an **EGETKEY** (⑩) instruction to the **MEE**.
### Key Observations
* **Dual-Key Architecture:** The process involves two distinct keys: a short-lived **ephemeral key** within the target Enclave and a persistent, hardware-backed **device-specific key** within the Quoting Enclave.
* **Central Role of the Quoting Enclave:** It acts as a privileged, platform-entitled component that bridges the user application enclave and the external Intel Attestation Service, converting local reports into globally verifiable quotes.
* **Layered Trust Model:** Trust is established through a chain: Hardware (MEE) -> Quoting Enclave (with device key) -> Intel Attestation Service (root of trust) -> Relying Party Service.
* **Separation of Concerns:** The diagram clearly separates the untrusted **Application**, the trusted execution environment (**Enclave**), the platform's trusted services (**Quoting enclave**), and the external authority (**Intel Attestation Service**).
### Interpretation
This diagram is a blueprint for **confidential computing** using Intel SGX. It demonstrates how a system can cryptographically prove to a remote party that a specific piece of code (the enclave) is running genuine, unmodified Intel SGX hardware in a secure environment.
* **What it enables:** This process allows services (**Service**) to safely process sensitive data within a remote, untrusted host by first verifying the integrity and authenticity of the execution environment. The **Claims** (⑤) likely contain the data or requests the service will only process if attestation succeeds.
* **Security Guarantees:** The flow ensures **integrity** (code/data hasn't been tampered with), **attestation** (proof of where it's running), and **confidentiality** (via the MEE's encryption). The use of a fresh **ephemeral key** per session provides forward-secrecy.
* **Underlying Assumptions:** The model assumes trust in Intel as the root of trust (via IAS) and in the hardware implementation of the MEE and Quoting Enclave. The security of the entire chain depends on the robustness of the **device-specific key** protection within the Quoting Enclave.
* **Missing Details:** The diagram abstracts away specific cryptographic algorithms (e.g., EPID vs. ECDSA-based attestation), network protocols, and the exact structure of the REPORT and QUOTE payloads. It focuses on the architectural flow and component responsibilities.
**Language Note:** All text in the diagram is in English.
DECODING INTELLIGENCE...
EXPERT: nemotron-free VERSION 1
RUNTIME: free/nvidia/nemotron-nano-12b-v2-vl:free
INTEL_VERIFIED
## Diagram: Secure Data Enclave and Attestation Workflow
### Overview
The diagram illustrates a secure data processing workflow involving memory encryption, enclave-based computation, and attestation services. It depicts interactions between hardware components (EPC, MEE), software enclaves, and external services (Intel Attestation Service) to ensure data confidentiality and integrity.
### Components/Axes
- **Key Components**:
- **Memory (EPC)**: Contains "App" and "EPC" sections with locked icons (green and red).
- **Enclave**: Labeled with "ephemeral key" and "EREPORT."
- **Quoting Enclave**: Contains "device-specific key" and "EGETKEY."
- **Application**: Receives "REPORT Claims" and "QUOTE" inputs.
- **Intel Attestation Service**: Sends "QUOTE" and "Challenge" to the Application.
- **Service**: Validates "QUOTE" and interacts with the Application.
- **MEE**: Handles "encrypt/decrypt" operations.
- **Arrows/Steps**:
- Numbered steps (1–9) indicate sequential processes:
1. **Challenge** (Application → Intel Attestation Service).
2. **QUOTE ID** (Intel Attestation Service → Application).
3. **EREPORT** (Enclave → Application).
4. **REPORT Claims** (Application → Intel Attestation Service).
5. **REPORT** (Application → Service).
6. **QUOTE** (Quoting Enclave → Service).
7. **QUOTE** (Service → Application).
8. **Validate** (Service → Application).
9. **Verification** (Application → Service).
- **Colors**:
- Green: Enclave, EREPORT, QUOTE.
- Red: EPC, EGETKEY.
- Orange: Quoting Enclave, EGETKEY.
- Black: Arrows, text, and borders.
### Detailed Analysis
- **Memory (EPC)**:
- Contains two locked sections: "App" (white) and "EPC" (red lock).
- Connected to MEE via bidirectional "encrypt/decrypt" arrows.
- **Enclave**:
- Generates "EREPORT" using an "ephemeral key" (green box).
- Sends "EREPORT" to the Application (step 3).
- **Quoting Enclave**:
- Uses a "device-specific key" (orange box) and "EGETKEY" to produce a "QUOTE" (step 6).
- Sends "QUOTE" to the Service for validation.
- **Intel Attestation Service**:
- Issues a "Challenge" to the Application (step 1).
- Receives "REPORT Claims" (step 4) and "QUOTE" (step 7).
- Sends "QUOTE" back to the Application for verification.
- **Service**:
- Validates "QUOTE" (step 8) and interacts with the Application (step 9).
- **MEE**:
- Encrypts/decrypts data between the App and Memory (EPC).
### Key Observations
1. **Security Layers**:
- Ephemeral and device-specific keys ensure transient and hardware-bound security.
- Locked icons (EPC, EGETKEY) suggest restricted access to sensitive data.
2. **Flow Direction**:
- Data flows from the Enclave to the Application, then to external services (Intel Attestation Service) for validation.
- The Service acts as a trusted intermediary for attestation.
3. **Redundancy**:
- "QUOTE" is exchanged twice (steps 6 and 7), indicating iterative verification.
### Interpretation
This diagram represents a secure enclave-based architecture where data is processed in isolated environments (Enclave, Quoting Enclave) and attested via the Intel Attestation Service. The use of ephemeral keys ensures short-lived encryption, while device-specific keys tie operations to hardware identity. The bidirectional MEE (Memory Encryption Engine) secures data at rest and in transit. The Intel Attestation Service validates the integrity of enclave-generated reports, ensuring trust in the system. The workflow emphasizes confidentiality (encryption), integrity (attestation), and accountability (verification).
**Note**: No numerical data or trends are present; the diagram focuses on process flow and component interactions.
DECODING INTELLIGENCE...