\n
## Diagram: Intel Attestation Service Flow
### Overview
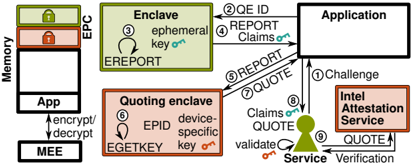
This diagram illustrates the flow of data and interactions between an Application, an Enclave, a Quoting Enclave, and the Intel Attestation Service, utilizing Intel's Enhanced Privacy Protection (EPC) and related technologies. The diagram depicts a secure attestation process, where the application verifies the integrity of the enclave before trusting its computations. The diagram uses numbered arrows to indicate the sequence of operations.
### Components/Axes
The diagram features the following components:
* **Memory:** Labelled on the left side, indicating the memory space.
* **App:** Represents the main Application.
* **Enclave:** A secure area within memory, utilizing EPC.
* **Quoting Enclave:** Another secure area within memory, responsible for generating quotes.
* **Intel Attestation Service:** A remote service for verifying the integrity of the enclaves.
* **MEE:** Marked as encrypt/decrypt.
* **EPC:** Marked as a memory region.
The diagram also includes the following labels and text embedded within components:
* **ephemeral key on:** Inside the Enclave.
* **EREPORT:** Inside the Enclave.
* **EPID:** Inside the Quoting Enclave.
* **EGETKEY:** Inside the Quoting Enclave.
* **device-specific key on:** Inside the Quoting Enclave.
* **Challenge:** From Application to Intel Attestation Service.
* **REPORT:** Exchanged between Application and Quoting Enclave.
* **QUOTE:** Exchanged between Quoting Enclave and Intel Attestation Service.
* **Claims on:** Labels on arrows indicating data claims.
* **validate on:** Label on arrow indicating validation.
* **Service Verification:** Label on the bottom right.
### Detailed Analysis / Content Details
The diagram shows a numbered sequence of operations:
1. **Challenge:** The Application sends a challenge to the Intel Attestation Service.
2. **QE ID REPORT:** The Application requests the Enclave's ID and a REPORT.
3. **ephemeral key on:** The Enclave generates an ephemeral key.
4. **Claims on REPORT:** The Application receives the REPORT and associated claims.
5. **REPORT:** The Application sends the REPORT to the Quoting Enclave.
6. **EPID EGETKEY device-specific key on:** The Quoting Enclave uses EPID and EGETKEY to generate a device-specific key.
7. **QUOTE:** The Quoting Enclave generates a QUOTE.
8. **Claims on QUOTE:** The Quoting Enclave sends the QUOTE and associated claims to the Intel Attestation Service.
9. **QUOTE:** The Intel Attestation Service receives the QUOTE.
10. **Service Verification:** The Intel Attestation Service performs service verification.
The arrows indicate the direction of data flow. The "encrypt/decrypt" label on the MEE suggests that the MEE is responsible for encrypting and decrypting data between the Application and the Enclave. The "EPC" label indicates that the Enclave resides within the EPC memory region.
### Key Observations
The diagram highlights a multi-step attestation process. The Quoting Enclave plays a crucial role in generating a QUOTE, which is then verified by the Intel Attestation Service. The use of EPID and EGETKEY suggests a hardware-based root of trust. The flow emphasizes the secure exchange of information and the validation of the enclave's integrity.
### Interpretation
This diagram demonstrates a secure attestation process designed to establish trust in a remote computation environment. The Intel Attestation Service acts as a trusted third party, verifying the integrity of the Enclave before the Application relies on its results. The use of EPC and hardware-based keys (EPID, EGETKEY) enhances the security of the process. The diagram suggests a system where sensitive computations are performed within a secure enclave, and the application can confidently verify that the enclave has not been tampered with. The process is complex, involving multiple steps and components, but it provides a robust mechanism for ensuring the integrity of remote computations. The "Claims on" labels suggest that the reports and quotes contain assertions about the enclave's configuration and state, which are verified by the Attestation Service. The diagram illustrates a critical component of Intel's security architecture, enabling secure remote execution and data protection.