## Diagram: Secure Data Enclave and Attestation Workflow
### Overview
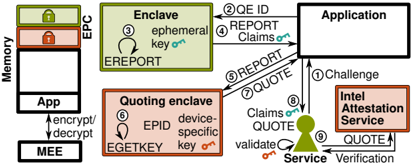
The diagram illustrates a secure data processing workflow involving memory encryption, enclave-based computation, and attestation services. It depicts interactions between hardware components (EPC, MEE), software enclaves, and external services (Intel Attestation Service) to ensure data confidentiality and integrity.
### Components/Axes
- **Key Components**:
- **Memory (EPC)**: Contains "App" and "EPC" sections with locked icons (green and red).
- **Enclave**: Labeled with "ephemeral key" and "EREPORT."
- **Quoting Enclave**: Contains "device-specific key" and "EGETKEY."
- **Application**: Receives "REPORT Claims" and "QUOTE" inputs.
- **Intel Attestation Service**: Sends "QUOTE" and "Challenge" to the Application.
- **Service**: Validates "QUOTE" and interacts with the Application.
- **MEE**: Handles "encrypt/decrypt" operations.
- **Arrows/Steps**:
- Numbered steps (1–9) indicate sequential processes:
1. **Challenge** (Application → Intel Attestation Service).
2. **QUOTE ID** (Intel Attestation Service → Application).
3. **EREPORT** (Enclave → Application).
4. **REPORT Claims** (Application → Intel Attestation Service).
5. **REPORT** (Application → Service).
6. **QUOTE** (Quoting Enclave → Service).
7. **QUOTE** (Service → Application).
8. **Validate** (Service → Application).
9. **Verification** (Application → Service).
- **Colors**:
- Green: Enclave, EREPORT, QUOTE.
- Red: EPC, EGETKEY.
- Orange: Quoting Enclave, EGETKEY.
- Black: Arrows, text, and borders.
### Detailed Analysis
- **Memory (EPC)**:
- Contains two locked sections: "App" (white) and "EPC" (red lock).
- Connected to MEE via bidirectional "encrypt/decrypt" arrows.
- **Enclave**:
- Generates "EREPORT" using an "ephemeral key" (green box).
- Sends "EREPORT" to the Application (step 3).
- **Quoting Enclave**:
- Uses a "device-specific key" (orange box) and "EGETKEY" to produce a "QUOTE" (step 6).
- Sends "QUOTE" to the Service for validation.
- **Intel Attestation Service**:
- Issues a "Challenge" to the Application (step 1).
- Receives "REPORT Claims" (step 4) and "QUOTE" (step 7).
- Sends "QUOTE" back to the Application for verification.
- **Service**:
- Validates "QUOTE" (step 8) and interacts with the Application (step 9).
- **MEE**:
- Encrypts/decrypts data between the App and Memory (EPC).
### Key Observations
1. **Security Layers**:
- Ephemeral and device-specific keys ensure transient and hardware-bound security.
- Locked icons (EPC, EGETKEY) suggest restricted access to sensitive data.
2. **Flow Direction**:
- Data flows from the Enclave to the Application, then to external services (Intel Attestation Service) for validation.
- The Service acts as a trusted intermediary for attestation.
3. **Redundancy**:
- "QUOTE" is exchanged twice (steps 6 and 7), indicating iterative verification.
### Interpretation
This diagram represents a secure enclave-based architecture where data is processed in isolated environments (Enclave, Quoting Enclave) and attested via the Intel Attestation Service. The use of ephemeral keys ensures short-lived encryption, while device-specific keys tie operations to hardware identity. The bidirectional MEE (Memory Encryption Engine) secures data at rest and in transit. The Intel Attestation Service validates the integrity of enclave-generated reports, ensuring trust in the system. The workflow emphasizes confidentiality (encryption), integrity (attestation), and accountability (verification).
**Note**: No numerical data or trends are present; the diagram focuses on process flow and component interactions.