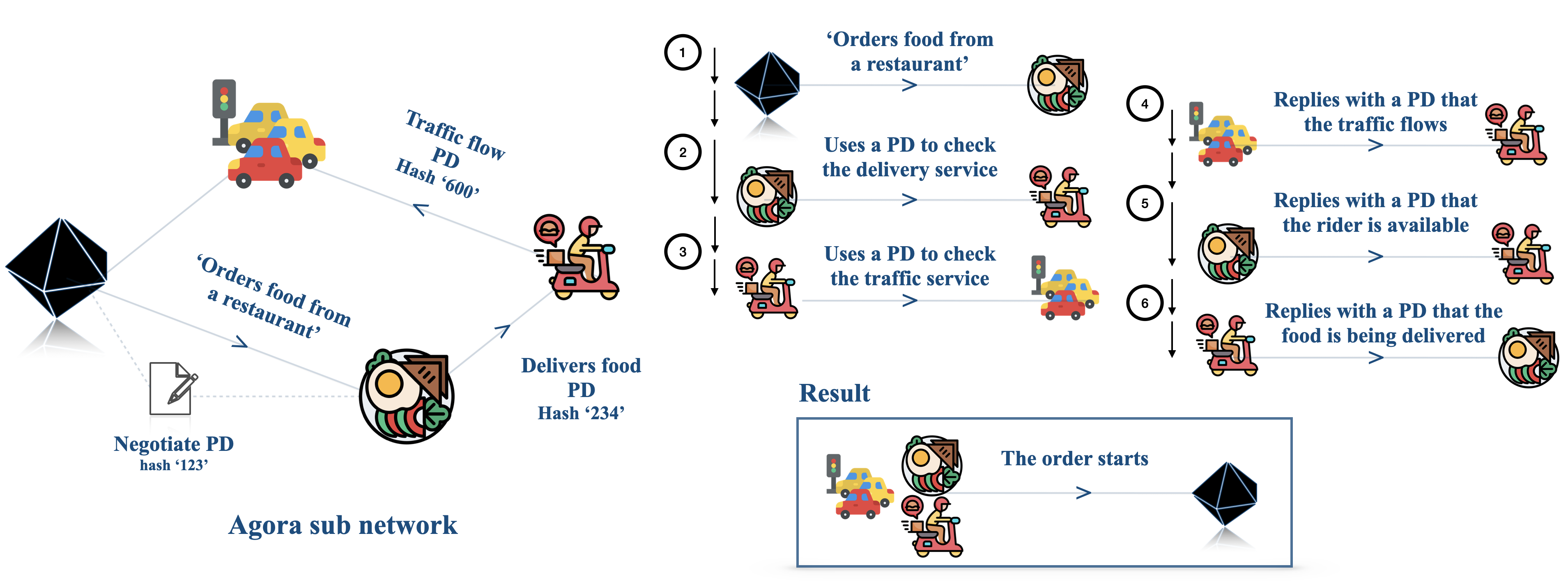
## Flowchart: Food Delivery Process with Proof of Delivery (PD) Hashes
### Overview
The diagram illustrates a decentralized food delivery workflow within the Agora subnetwork, emphasizing cryptographic verification via Proof of Delivery (PD) hashes. It shows interactions between a restaurant, delivery service, traffic service, and rider, with PD hashes ensuring trust at each stage.
### Components/Axes
- **Key Elements**:
- **Agora Subnetwork**: Centralized hub for PD hash negotiation (PD hash '123').
- **Restaurant**: Initiates order (PD hash '234' for food delivery).
- **Delivery Service**: Verifies traffic flow (PD hash '600') and rider availability.
- **Traffic Service**: Confirms traffic conditions via PD hash '600'.
- **Rider**: Completes delivery, triggering final PD confirmation.
- **Flow Direction**:
- Left-to-right progression: Restaurant → Delivery Service → Traffic Service → Rider.
- Circular feedback loops for PD verification at each step.
### Detailed Analysis
1. **Order Initiation**:
- Restaurant sends PD hash '234' to Agora subnetwork to negotiate food delivery.
- Agora subnetwork replies with PD hash '123' to confirm order.
2. **Traffic Flow Check**:
- Delivery service queries traffic service using PD hash '600'.
- Traffic service replies with PD confirming traffic flow.
3. **Rider Availability**:
- Delivery service checks rider availability via PD hash '600'.
- Rider confirms availability, triggering PD hash '600' response.
4. **Delivery Completion**:
- Rider delivers food, prompting PD hash '234' confirmation from delivery service.
- Final PD hash '600' confirms delivery completion.
### Key Observations
- **PD Hash Reuse**: PD hash '600' is reused for traffic flow and rider availability checks, suggesting a standardized verification mechanism.
- **Sequential Trust**: Each party (restaurant, delivery service, traffic service, rider) must validate their role via PD hashes before proceeding.
- **Cryptographic Security**: PD hashes act as immutable records, preventing tampering and ensuring accountability.
### Interpretation
This workflow demonstrates a trustless system where cryptographic proofs replace traditional intermediaries. The Agora subnetwork facilitates secure PD hash negotiation, while sequential PD checks ensure:
1. **Authenticity**: Each participant’s role is verified (e.g., rider availability).
2. **Transparency**: Traffic conditions and delivery status are publicly verifiable.
3. **Efficiency**: Automated PD exchanges reduce manual oversight, enabling real-time updates.
The reuse of PD hash '600' for multiple checks implies a modular design, where a single hash can validate multiple trust nodes (traffic, rider). This system could scale to other services (e.g., logistics) by extending PD hash applications.