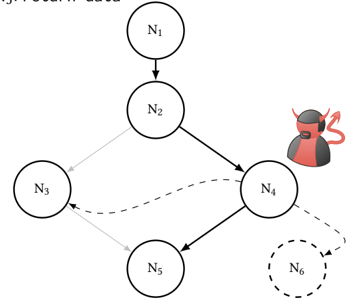
## Directed Graph Diagram: System with Malicious Actor Infiltration
### Overview
The image displays a directed graph diagram consisting of six circular nodes labeled N₁ through N₆, interconnected by arrows indicating flow or dependency. A distinct visual element—a stylized devil or hacker icon—is positioned adjacent to node N₄, suggesting a malicious actor or compromised component within the system. The diagram uses solid and dashed lines to differentiate between types of connections or states.
### Components/Axes
* **Nodes:** Six circular nodes, each containing a label:
* **N₁:** Top-center position.
* **N₂:** Directly below N₁.
* **N₃:** To the left of the central vertical axis, below N₂.
* **N₄:** To the right of the central vertical axis, below N₂. This node has a devil/hacker icon placed to its immediate right.
* **N₅:** Below and between N₃ and N₄.
* **N₆:** Bottom-right position, enclosed within a dashed circle.
* **Connections (Edges):**
* **Solid Arrows:** Indicate primary or direct flow/dependency.
* N₁ → N₂
* N₂ → N₃
* N₂ → N₄
* N₄ → N₅
* **Dashed Arrows:** Indicate secondary, indirect, or potentially malicious/untrusted flow.
* N₃ → N₅ (dashed line)
* N₄ → N₆ (dashed line)
* **Icon:** A red and black icon depicting a horned figure (devil/hacker) is placed to the right of node N₄.
### Detailed Analysis
The diagram illustrates a hierarchical and interconnected system with a clear point of compromise.
1. **Primary Flow (Solid Lines):** The main process originates at N₁, flows to N₂, and then splits to N₃ and N₄. From N₄, the primary flow continues to N₅. This establishes a core pathway: N₁ → N₂ → (N₃, N₄) → N₅.
2. **Secondary/Malicious Flow (Dashed Lines):** Two dashed connections exist:
* A dashed line from N₃ to N₅, creating an alternative or parallel path to the primary N₄→N₅ link.
* A dashed line from N₄ to N₆. Node N₆ is itself highlighted with a dashed circular border, setting it apart from the other solid-bordered nodes.
3. **Spatial Grounding of Key Element:** The devil icon is positioned in the **center-right** region of the diagram, immediately adjacent to node N₄. Its placement directly associates the malicious actor with that specific node.
### Key Observations
* **Node N₄ is the focal point of compromise.** It is the only node directly associated with the malicious actor icon.
* **Node N₆ is uniquely styled.** Its dashed border and the dashed incoming arrow from N₄ suggest it is an external, untrusted, or compromised endpoint.
* **The system has redundancy or alternative paths.** Node N₅ receives input from both N₃ (dashed) and N₄ (solid), indicating it can be reached via two different routes.
* **The malicious actor (at N₄) has direct influence.** It has a primary (solid) connection to N₅ and a secondary (dashed) connection to the external/untrusted node N₆.
### Interpretation
This diagram models a system where a malicious actor has infiltrated a specific component (N₄). The infiltration has two potential consequences:
1. **Direct Corruption of Downstream Process:** The compromised N₄ can directly affect node N₅ via the primary, trusted pathway (solid arrow). This represents a supply-chain or dependency-based attack where a trusted component is used to propagate malicious activity.
2. **Data Exfiltration or Communication with External Entity:** The dashed connection from N₄ to N₆ suggests the compromised node is communicating with or sending data to an external, untrusted system (N₆). The dashed styling of both the arrow and N₆'s border reinforces its untrusted or clandestine nature.
The presence of the dashed line from N₃ to N₅ is notable. It could represent a legitimate backup process, but in the context of the compromise at N₄, it might also indicate an attempt by the system to route around the compromised node, or conversely, a secondary attack vector being established. The diagram effectively visualizes a security threat model, highlighting the critical node (N₄) and the potential paths for attack propagation and data leakage.